Test 5(L9 and L10)
0.0(0)
Studied by 3 peopleCard Sorting
1/15
Earn XP
Description and Tags
Last updated 12:41 PM on 10/17/22
Name | Mastery | Learn | Test | Matching | Spaced | Call with Kai |
|---|
No analytics yet
Send a link to your students to track their progress
16 Terms
1
New cards
Q.1 Name the two paradigms (architectures) in applications layers?
- Client-server architecture
- Peer-to-Peer architecture
- Peer-to-Peer architecture
2
New cards
Q.2 What are the important aspects/services that one may consider in transport layer in
developing applications?
developing applications?
- Reliable data transfer: For, some applications such as emails, file transfer, and web
document transfer, financial documents, data loss could have devastating consequences.
Therefore, to support these application transport layer protocol should provide reliable
data transfer service. However, other applications such as multimedia; real-time
audio/video can tolerate some amount of data loss.
- Throughput: Some Internet applications are bandwidth-sensitive requiring guaranteed
throughput service. For example, Internet telephony encodes voice at 32kbps. If transport
layer protocols cannot support this throughput requirement, application would need to
encode the data at a lower rate.
- Timing: For certain applications such as real-time interactive gaming, transport layer
protocols must guarantee timing for each bit that a sender sends to a receiver as these
applications have strict delay constraint.
document transfer, financial documents, data loss could have devastating consequences.
Therefore, to support these application transport layer protocol should provide reliable
data transfer service. However, other applications such as multimedia; real-time
audio/video can tolerate some amount of data loss.
- Throughput: Some Internet applications are bandwidth-sensitive requiring guaranteed
throughput service. For example, Internet telephony encodes voice at 32kbps. If transport
layer protocols cannot support this throughput requirement, application would need to
encode the data at a lower rate.
- Timing: For certain applications such as real-time interactive gaming, transport layer
protocols must guarantee timing for each bit that a sender sends to a receiver as these
applications have strict delay constraint.
3
New cards
Q.3 What is the purpose of SSL (Secure Socket Library)? Explain your answer.
Application layer uses SSL to:
- provides encrypted TCP connection
- data integrity
- end-point authentication
- provides encrypted TCP connection
- data integrity
- end-point authentication
4
New cards
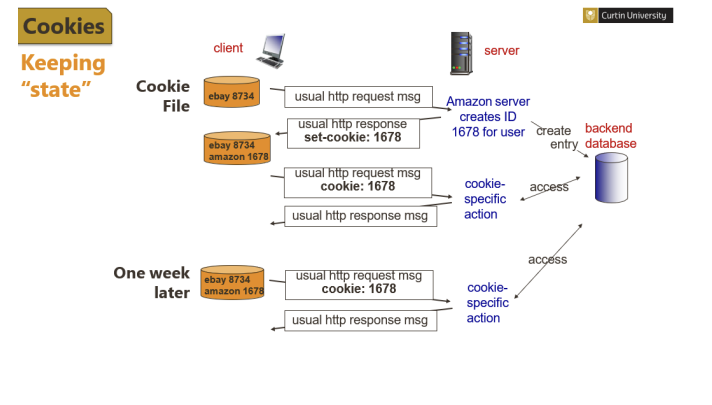
Q.4 How does HTTP maintain the “state” of the user?
HTTP is stateless but by using cookies as protocol end points, it can maintain the state of users,
and this could be beneficial for websites such as online shopping. As explain in the lecture:
and this could be beneficial for websites such as online shopping. As explain in the lecture:
5
New cards
Q.5 What is the difference between GET method and Conditional GET?
The conditional GET method uses an additional field called “if-modified-since” to get the latest
copy of the requested object and store it in the proxy server. When original receives a
conditional GET request, it responds to the proxy server that:
- Content not modified via HTTP 304 response code.
- In case if the contents are modified, then it sends the updated copy of the
document/object to the proxy server.
copy of the requested object and store it in the proxy server. When original receives a
conditional GET request, it responds to the proxy server that:
- Content not modified via HTTP 304 response code.
- In case if the contents are modified, then it sends the updated copy of the
document/object to the proxy server.
6
New cards
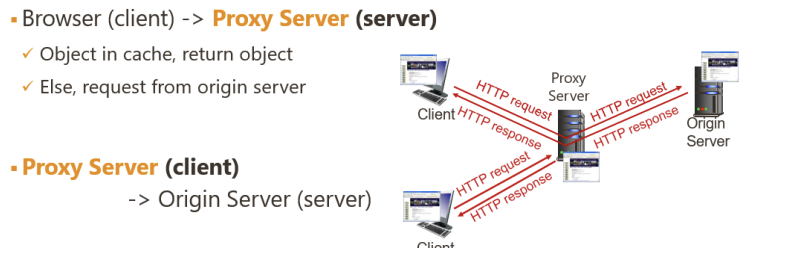
Q.6 Describe an elegant solution for an enterprise to minimize the delay of response for web
requests?
requests?
Web proxy or web cache. The web proxy server is installed by ISP in the University or company
premises to store a local copy of the object each time a client request from the original server.
The web caching significantly reduces the response time for the client request and reduces
traffic on the institutional access link. Please refer to week 9 lecture slide 50
premises to store a local copy of the object each time a client request from the original server.
The web caching significantly reduces the response time for the client request and reduces
traffic on the institutional access link. Please refer to week 9 lecture slide 50
7
New cards
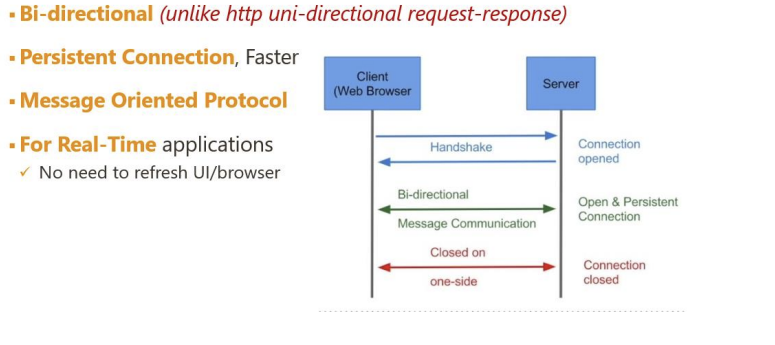
Q.7 What are web sockets and how it is different from typical HTTP communication and TCP
sockets?
sockets?
Compared to a conventional HTTP type communication in which communication between a client
a server occurs in the form request/response one at a time, web socket allows bidirectional data
transfer between client and a server. Web sockets are used for real-time applications, where
HTTP type communication would require refreshing UI every time.
Please refer lecture slide number 45.
a server occurs in the form request/response one at a time, web socket allows bidirectional data
transfer between client and a server. Web sockets are used for real-time applications, where
HTTP type communication would require refreshing UI every time.
Please refer lecture slide number 45.
8
New cards
Q.8 Is WWW another term to refer to “internet”? Explain
Internet is a network of networks
WWW is a distributed system that runs on the top of the network to store and share
information i.e., website
WWW is a distributed system that runs on the top of the network to store and share
information i.e., website
9
New cards
Q.9 Compare and Contrast POP3 and IMAP. Explain how IMAP maintain the user state across
sessions with an example.
sessions with an example.
POP3
- POP: Post Office Protocol version 3: Authorization, Download
- stateless across sessions
Two Modes:
o Download and Delete: Previous example uses this mode Bob cannot reread e-mail if he changes client
o Download and Keep: Copies of messages on different clients
IMAP: Internet Mail Access Protocol: More Features
including manipulation of stored messages on server
- Keeps all messages in one place: at server
- Allows user to organize messages in folders
- IMAP is stateful across sessions
o Names of folders and mappings between message IDs and folder name
- POP: Post Office Protocol version 3: Authorization, Download
- stateless across sessions
Two Modes:
o Download and Delete: Previous example uses this mode Bob cannot reread e-mail if he changes client
o Download and Keep: Copies of messages on different clients
IMAP: Internet Mail Access Protocol: More Features
including manipulation of stored messages on server
- Keeps all messages in one place: at server
- Allows user to organize messages in folders
- IMAP is stateful across sessions
o Names of folders and mappings between message IDs and folder name
10
New cards
Q.1 In DHCP, why is the client required to renew the lease on IP address in use?
DHCP assigns IP address dynamically to any host in a network for a specific lease time. When
the lease period expires, DHCP may assign this IP address to any other host. But in case, if a
host would like to renew the lease (after 50% lease time), host client can send a renew
request which a DHCP server may accept (by sending ACK) or reject (by sending NAK).
the lease period expires, DHCP may assign this IP address to any other host. But in case, if a
host would like to renew the lease (after 50% lease time), host client can send a renew
request which a DHCP server may accept (by sending ACK) or reject (by sending NAK).
11
New cards
Q.2 Can a machine with single DNS name have multiple IP address? How can this occur?
Yes. This is known as round-robin DNS that involves single DNS name with multiple IP
addresses.
addresses.
12
New cards
Q.3 What is the use of “hosts” file? What are the advantages of having a DNS server over
“host” file?
“host” file?
Host file is managed by a operating system to keep a record of IP address for a domain
name, having host file on a local machine is fine for a local test site.
Host file is located:
Windows: C:\Windows\System32\Drivers\etc\hosts
Linux: \etc\hosts
(Open the ‘hostfile’ using notepad and explore the information that hostfile contains.)
Imagine, you have a live website for example twitter. You would need to register this website
and DNS server to keep track of records for domains.
name, having host file on a local machine is fine for a local test site.
Host file is located:
Windows: C:\Windows\System32\Drivers\etc\hosts
Linux: \etc\hosts
(Open the ‘hostfile’ using notepad and explore the information that hostfile contains.)
Imagine, you have a live website for example twitter. You would need to register this website
and DNS server to keep track of records for domains.
13
New cards
Q.4 Consider the following case study.
Alice in Curtin University(alice@curtin.edu.au) wants to send an email to Bob in Yale
University (bob@cs.ai.yale.edu). Write down all the steps involved in the process an email
including the name resolution process via the DNS servers.
You may assume that the DNS servers exist for Curtin, edu (TLD), Yale and Yale Computing
Faculty(cs).
Alice in Curtin University(alice@curtin.edu.au) wants to send an email to Bob in Yale
University (bob@cs.ai.yale.edu). Write down all the steps involved in the process an email
including the name resolution process via the DNS servers.
You may assume that the DNS servers exist for Curtin, edu (TLD), Yale and Yale Computing
Faculty(cs).
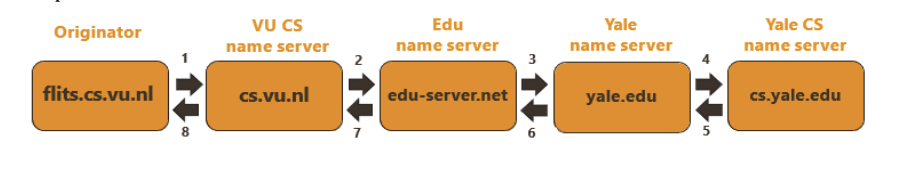
Refer to week 10 lecture slide number 19 which shows a sequence of steps. In the question
originator is from Curtin University. Hence a DNS query from Alice will go to Yale name server
that has the domain name of cs.ai.yale.edu via Curtin’s name server, edu TLD server, and Yale
name server.
originator is from Curtin University. Hence a DNS query from Alice will go to Yale name server
that has the domain name of cs.ai.yale.edu via Curtin’s name server, edu TLD server, and Yale
name server.
14
New cards
Q.5 Compare client-server architecture with P2P. Explain the file distribution of file size F
from one server to N peers to compare both architectures
from one server to N peers to compare both architectures
Let’s determine the file distribution time for the client-server architecture and the file
distribution time by peer-to-peer architecture.
Client-server:
- The server must transmit one copy of file size F bits to each of N peers. Thus, the
server must transmit NF bits. The server upload rate is ‘𝑢𝑠
′, the time to distribute
the file be at least NF/𝑢𝑠
- Let’s suppose 𝑑𝑚𝑖𝑛 denote the minimum rate of the peer with the lowest
download rate. Thus, the minimum distribution time is F/𝑑𝑚𝑖𝑛.
Putting these observations together:
Lower bound on file distribution time with client server:𝐷𝑐𝑠 ≥ max (𝑁𝐹/𝑢𝑠,𝐹/𝑑𝑚𝑖𝑛)
In this equation if N (number of peers/users) is large then file distribution increases
linearly. For example, if the number of peers from one week to the next increases a
thousand-fold from a thousand to a million, the time required to distribute the file
to all peers increases by 1000.
Peer-to-Peer:
P2P architecture is somewhat complicated than the client-server architecture, since the file
distribution time depends on how peers distribute the portion of the file to the other peers.
Some of observations for P2P:
- For P2P, server upload the file size F bits only once and thus the minimum
distribution time is F/𝑢𝑠
.
- As with the client-server, P2P also have a minimum distribution time for a peer
with a lowest download rate as F/𝑑𝑚𝑖𝑛.
- Total upload capacity for P2P is equal to server upload capacity 𝑢𝑠 + the
upload capacity of all peers.
Combining all observations, the distribution time for P2P:
𝐷𝑃2𝑃 ≥ max (𝑁𝐹/𝑢𝑠,𝐹/𝑑𝑚𝑖𝑛,𝑁𝐹/𝑢𝑠 + ∑ 𝑢𝑖𝑛,𝑖=1)
P2P will always have less distribution time than client-server and is scalable.
distribution time by peer-to-peer architecture.
Client-server:
- The server must transmit one copy of file size F bits to each of N peers. Thus, the
server must transmit NF bits. The server upload rate is ‘𝑢𝑠
′, the time to distribute
the file be at least NF/𝑢𝑠
- Let’s suppose 𝑑𝑚𝑖𝑛 denote the minimum rate of the peer with the lowest
download rate. Thus, the minimum distribution time is F/𝑑𝑚𝑖𝑛.
Putting these observations together:
Lower bound on file distribution time with client server:𝐷𝑐𝑠 ≥ max (𝑁𝐹/𝑢𝑠,𝐹/𝑑𝑚𝑖𝑛)
In this equation if N (number of peers/users) is large then file distribution increases
linearly. For example, if the number of peers from one week to the next increases a
thousand-fold from a thousand to a million, the time required to distribute the file
to all peers increases by 1000.
Peer-to-Peer:
P2P architecture is somewhat complicated than the client-server architecture, since the file
distribution time depends on how peers distribute the portion of the file to the other peers.
Some of observations for P2P:
- For P2P, server upload the file size F bits only once and thus the minimum
distribution time is F/𝑢𝑠
.
- As with the client-server, P2P also have a minimum distribution time for a peer
with a lowest download rate as F/𝑑𝑚𝑖𝑛.
- Total upload capacity for P2P is equal to server upload capacity 𝑢𝑠 + the
upload capacity of all peers.
Combining all observations, the distribution time for P2P:
𝐷𝑃2𝑃 ≥ max (𝑁𝐹/𝑢𝑠,𝐹/𝑑𝑚𝑖𝑛,𝑁𝐹/𝑢𝑠 + ∑ 𝑢𝑖𝑛,𝑖=1)
P2P will always have less distribution time than client-server and is scalable.
15
New cards
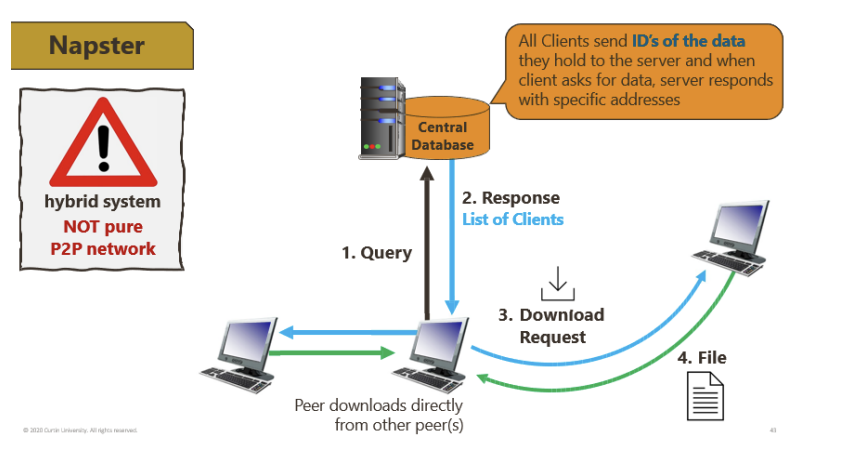
Q.6 Why is Napster not considered a pure P2P protocol? Why is Gnutella considered to be a
pure P2P protocol?
pure P2P protocol?
Napster is not a pure P2P as it uses a central database to store all client IDs before they can
communicate P2P as shown below (lecture slide 42):
communicate P2P as shown below (lecture slide 42):
16
New cards
Q.7 What is the process of joining torrent in BitTorrent protocol? What does the term titfor-tat mean in BitTorrent protocol?
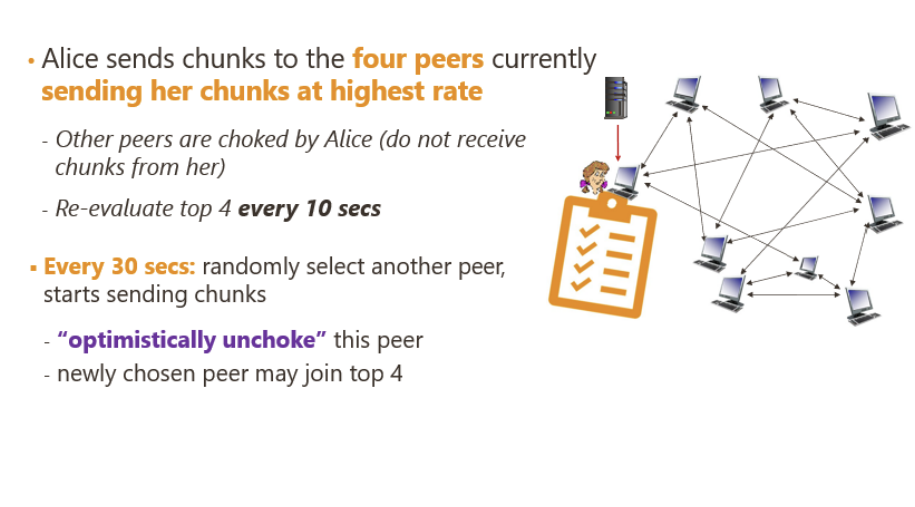
BitTorrent uses a trading algorithm defining tit-for-tat means to reward peers sending
with highest rate (good behaviour) and punishing the ones with bad behaviour.
BitTorrent uses a clever trading algorithm. The basic idea is Alice gives priority to the
neighbours that are supply her the data at the highest rate.
For each of the neighbours, Alice continually measures the rate at which she receives bits
and determines the top four peers feeding her bits at highest rate.
Every 10 seconds she recalculates the rates and possibly modify the list of top four peers.
Also, every 30 seconds, she picks up one additional neighbour and sends it chunks, let’s call
him Bob. Now Alice becomes Bob’s top four neighbour.
with highest rate (good behaviour) and punishing the ones with bad behaviour.
BitTorrent uses a clever trading algorithm. The basic idea is Alice gives priority to the
neighbours that are supply her the data at the highest rate.
For each of the neighbours, Alice continually measures the rate at which she receives bits
and determines the top four peers feeding her bits at highest rate.
Every 10 seconds she recalculates the rates and possibly modify the list of top four peers.
Also, every 30 seconds, she picks up one additional neighbour and sends it chunks, let’s call
him Bob. Now Alice becomes Bob’s top four neighbour.