Cyber Security-4
Network Security Overview
Network security is all about protecting data and resources within a network from unauthorized access, attacks, or misuse. It’s especially critical for any network connected to the public Internet, which is the main medium through which devices communicate globally.
Two Ways to Explain Network Security
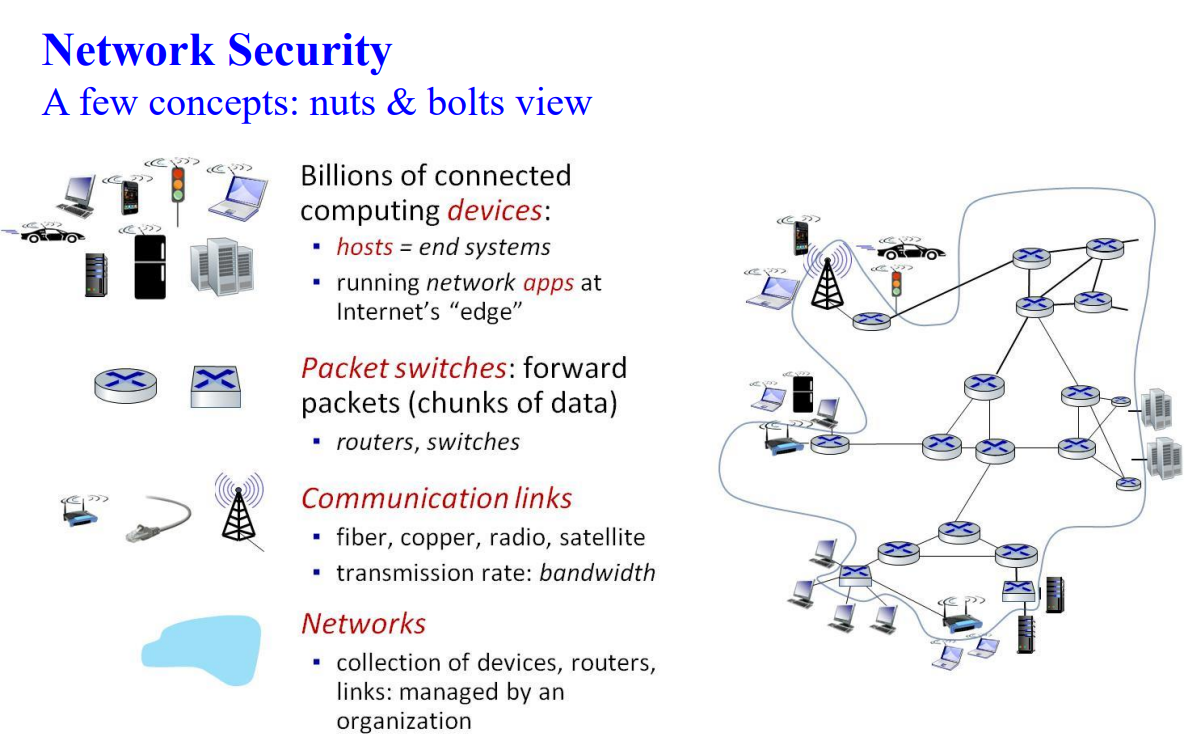
Nuts and Bolts View: This approach focuses on the technical components of network security, like the hardware and software that make a network safe. These components include firewalls, routers, encryption software, antivirus programs, and intrusion detection systems. It’s like looking at the “parts” of a secure network and understanding what each part does to keep data safe.
Services View: Here, the focus is on what the network provides to users and applications rather than the hardware behind it. In this view, network security infrastructure is about enabling services like secure messaging, secure file sharing, and data protection for applications spread across different locations. The goal is to ensure that users can safely access and use these distributed applications without risking data breaches or attacks.
In summary, the "nuts and bolts" view is about the tools and technology of network security, while the "services view" is about what network security enables for users and applications across the Internet. Both views are important to understand the full picture of network security.
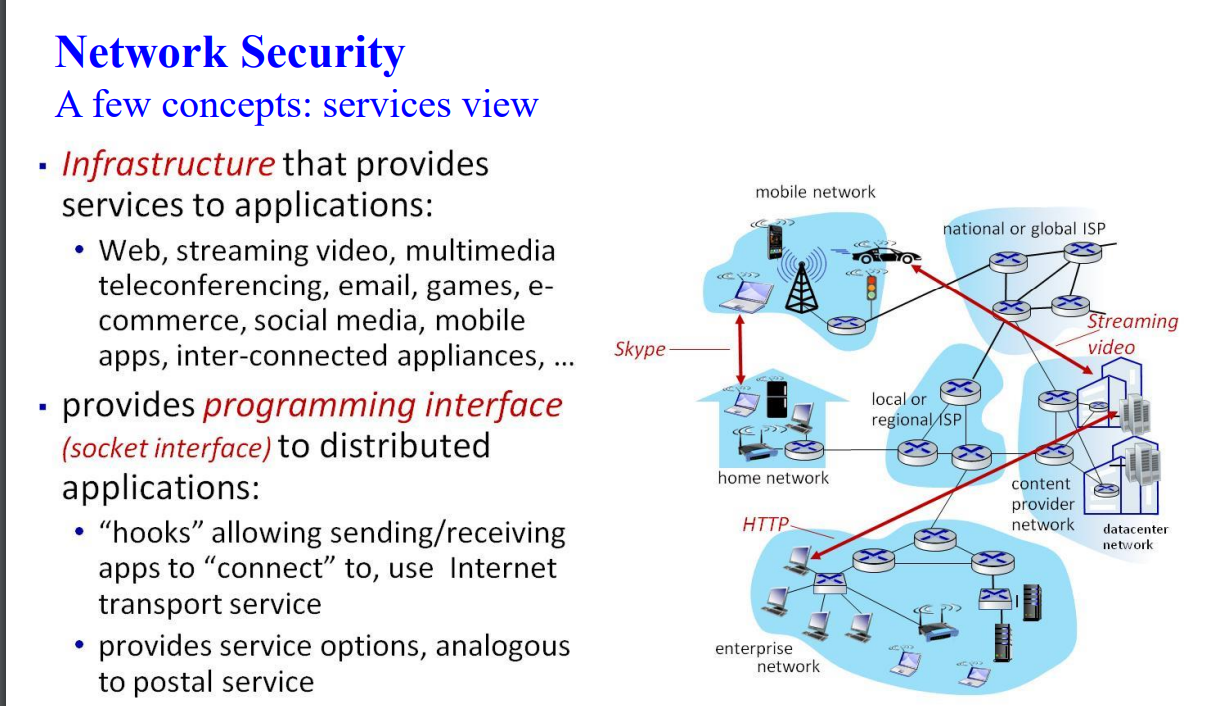
This image explains key concepts of network security from a services perspective. Let me break it down:
Infrastructure Layer:
The diagram shows different types of networks interconnected: home networks, mobile networks, enterprise networks, and datacenter networks
These are connected through local/regional ISPs and national/global ISPs
The infrastructure supports various services like Skype (shown in the example), streaming video, and HTTP connections
Programming Interface:
The image explains that the infrastructure provides a "socket interface" for distributed applications
This interface acts like "hooks" that allow applications to connect and use Internet transport services
It's compared to postal service, suggesting it provides standardized ways to send and receive data
Services Supported:
The infrastructure supports many modern applications including:
Web services
Streaming video
Multimedia teleconferencing
Email
Games
E-commerce
Social media
Mobile apps
Inter-connected appliances
The diagram effectively illustrates how different network types (shown in blue bubbles) are interconnected, and how services like streaming video and Skype (shown with red arrows) traverse these networks to connect users with content and each other. The structure shows a hierarchical organization from local networks up through regional and global ISPs to reach content providers and datacenters.
Network Security
A few concepts: layers
19
Two layers not found in Internet protocol stack!
▪ presentation: allow applications to interpret meaning of data, e.g., encryption, compression, machine-specific conventions
▪ session: synchronization, checkpointing, recovery of data exchange
▪ Internet stack “missing” these layers!
• these services, if needed, must be implemented in application
Warm-up and Basic Concepts (10 Questions)
In public key encryption, if A wants to send an encrypted message to B, which key does A use to encrypt the message?
a) A's private key
b) A's public key
c) B's private key
d) B's public keyWhat is the main use of a cryptographic hash function?
a) Data encryption
b) Data integrity verification
c) Authentication
d) Key generationTrue or False: A cryptographic hash function requires a secret key to compute a hash.
a) False
b) TrueDigital signatures provide:
a) Confidentiality and availability
b) Authentication and integrity
c) Key exchange
d) Non-repudiation and confidentialityWhat does a cipher do?
a) Performs encryption and decryption
b) Stores encrypted data
c) Manages encryption keys
d) Analyzes encrypted textWhich of the following is not true about public key cryptography?
a) Uses different keys for encryption and decryption
b) Public keys must be unique for each user
c) The private key cannot be deduced from the public key
d) It enables secure communicationWhat is the disadvantage of asymmetric cryptography?
a) No need for key distribution
b) Digital signatures are supported
c) Security is high
d) It is inefficient for large dataWhich algorithm is symmetric?
a) RSA
b) ECC
c) AES
d) DSAThe output of a cryptographic hash function is:
a) A fixed-size bit string
b) A variable-size bit string
c) A random string
d) Encrypted textWhich is true about SHA-1?
a) It is a symmetric encryption algorithm.
b) It is a cryptographic hash function.
c) It requires a private key.
d) It is used for key exchange.
Network Layers (10 Questions)
Which layer is responsible for routing data between devices?
a) Application layer
b) Transport layer
c) Network layer
d) Link layerWhat protocol is used at the transport layer for reliable communication?
a) HTTP
b) TCP
c) IP
d) UDPWhat is the purpose of the link layer?
a) Process-to-process communication
b) Routing data packets
c) Transferring data between network elements
d) Encrypting dataWhich layer deals with "bits on the wire"?
a) Physical layer
b) Transport layer
c) Link layer
d) Network layerWhat service is NOT implemented in the Internet protocol stack?
a) Application
b) Transport
c) Network
d) PresentationWhich of the following is an example of an application-layer protocol?
a) TCP
b) IP
c) HTTP
d) EthernetDNS uses which type of queries?
a) TCP queries only
b) UDP queries only
c) Iterative queries only
d) Both iterative and recursive queriesMAC addresses are found at which layer?
a) Application layer
b) Link layer
c) Network layer
d) Physical layerAddress Resolution Protocol (ARP) is used to:
a) Map IP addresses to MAC addresses
b) Encrypt data at the network layer
c) Route data between devices
d) Assign IP addressesWhat is the purpose of the Time-To-Live (TTL) field in an ARP table?
a) Route traffic
b) Map MAC addresses
c) Indicate when an entry should expire
d) Detect ARP spoofing
Network Attacks (20 Questions)
What type of attack involves intercepting communication without altering it?
a) Eavesdropping
b) Man-in-the-Middle
c) Spoofing
d) DoSWhich attack poisons ARP tables to redirect traffic?
a) MAC flooding
b) ARP spoofing
c) DNS spoofing
d) DHCP starvationA DHCP starvation attack aims to:
a) Decrypt network traffic
b) Redirect network traffic
c) Exhaust available IP addresses
d) Overwhelm DNS serversThe main goal of a DoS attack is to:
a) Eavesdrop on communication
b) Overload a system or network
c) Redirect data traffic
d) Modify data in transitWhat is an example of a volumetric DDoS attack?
a) SYN flood
b) UDP flood
c) ARP spoofing
d) Rogue DHCPDNS amplification is an example of:
a) Protocol DDoS
b) Volumetric DDoS
c) Application-layer attack
d) Passive attackWhich attack involves sending partial HTTP requests to overwhelm a server?
a) DNS flood
b) SYN flood
c) Slowloris
d) SQL injectionThe purpose of MAC spoofing is to:
a) Redirect DNS traffic
b) Imitate another device on the network
c) Encrypt data
d) Flood the networkWhat does SYN flooding target?
a) Open ports by overloading with SYN packets
b) IP routing tables
c) DNS resolution
d) ARP tablesWhich type of DDoS attack operates at the application layer?
a) UDP flood
b) SYN flood
c) HTTP flood
d) ICMP floodHow does a rogue DHCP attack work?
a) By exhausting IP addresses
b) By sending malicious DHCP responses
c) By redirecting DNS queries
d) By spoofing ARP tablesICMP flood attacks rely on:
a) Exhausting open ports
b) Overwhelming with echo requests and replies
c) Poisoning ARP tables
d) Manipulating DNS recordsWhat can be used to detect bogus ARP replies?
a) DDoS mitigators
b) IDS/IPS
c) Proxy servers
d) DNS resolversEavesdropping attacks are generally:
a) Passive
b) Active
c) Volumetric
d) Protocol-basedWhich is an example of an active sniffing attack?
a) ICMP flood
b) MITM attack
c) DNS amplification
d) MAC spoofingWhat is the primary purpose of IDS?
a) Block attacks
b) Detect and alert on potential attacks
c) Prevent all vulnerabilities
d) Mask sensitive dataA honeypot is used to:
a) Encrypt network data
b) Monitor ARP tables
c) Attract and study attackers
d) Allocate network zonesWhich attack exploits network traffic for fake responses?
a) SQL injection
b) Rogue DHCP
c) ARP flooding
d) SlowlorisWhat is the effect of an HTTP flood?
a) Overloads IP tables
b) Overloads server resources with legitimate-looking requests
c) Redirects DNS traffic
d) Manipulates ARP entriesWhat type of data is used in DNS amplification?
a) Spoofed DNS requests
b) ARP replies
c) HTTP headers
d) ICMP packets
Defenses and Strategies (10 Questions)
What is a common strategy to mitigate DDoS attacks?
a) Limit the number of connections per IP
b) Disable all DNS servers
c) Increase encryption levels
d) Use static ARP tablesA packet filter checks:
a) Data payloads
b) Headers of packets
c) TCP connections
d) MAC addressesIDS detects attacks using:
a) Firewalls only
b) Statistical and signature-based methods
c) Behavioral and signature-based methods
d) Only AI systemsWhat is the main use of a proxy server?
a) Enforcing ARP protocols
b) Acting as an intermediary for client-server requests
c) Encrypting DNS queries
d) Blocking DoS attacksHoneypots should:
a) Be monitored carefully for suspicious activity
b) Serve real user traffic
c) Use the latest production data
d) Be public-facing onlyFail-safe systems should:
a) Deny all access by default
b) Grant all access by default
c) Reject unpermitted packets
d) Ignore packet headersZone compartmentalization improves security by:
a) Separating sensitive and public systems
b) Granting full access to all zones
c) Eliminating DMZ
d) Disabling network layersWhich protocol is often used for secure web communication?
a) TCP
b) DNS
c) HTTPS
d) ARPContent filters can:
a) Block rogue DHCP requests
b) Scan for malicious payloads
c) Redirect traffic
d) Enforce TTL limitsWPA2 encryption is commonly used to secure:
a) ARP tables
b) DNS lookups
c) Wireless networks
d) MAC addresses