Network Fundamentals Comprehensive Notes
Transmission & Networking Fundamentals
Transmission Time Calculation
Data Rate and Bandwidth understand the concepts and relationship between them.
Transport Layer Protocols
Transmission Control Protocol (TCP)
Features: This includes connection-oriented, reliable delivery, and ordered data transfer.
Reliable delivery is achieved through sequencing and acknowledgment mechanisms.
Flow control manages the rate of data transmission to prevent overwhelming the receiver.
Congestion control prevents network congestion by adjusting the transmission rate.
User Datagram Protocol (UDP)
Features: connectionless, unreliable delivery, suitable for applications where speed is more important than reliability.
Process delivery: data is delivered to specific processes using port numbers.
Multiplexing/demultiplexing: allows multiple applications to use the same network connection.
Network Devices & Protocols
Telnet, SNMP, and DNS
Functionality: Telnet provides remote access to a command-line interface, SNMP is used for network management, and DNS translates domain names to IP addresses.
Network management: SNMP is crucial for monitoring and managing network devices.
ARP, RARP, ICMP, IGMP
ARP (Address Resolution Protocol) resolves IP addresses to MAC addresses.
In order to send the data to destination, having IP address is necessary but not sufficient; we also need the physical address of the destination machine. ARP is used to get the physical address (MAC address) of destination machine Before sending the IP packet, the MAC address of destination must be known. If not so, then sender broadcasts the ARP-discovery packet requesting the MAC address of intended destination. Since ARP-discovery is broadcast, every host inside that network will get this message but the packet will be discarded by everyone except that intended receiver host whose IP is associated. Now, this receiver will send a unicast packet with its MAC address (ARP-reply) to the sender of ARP-discovery packet. After the original sender receives the ARP-reply, it updates ARP-cache and start sending unicast message to the destination
RARP (Reverse Address Resolution Protocol) resolves MAC addresses to IP addresses.
s. When a new machine is setup or any machine which don’t have memory to store IP address, needs an IP address for its own use. So the machine sends a RARP broadcast packet which contains its own MAC address in both sender and receiver hardware address field.A special host configured inside the local area network, called as RARPserver is responsible to reply for these kind of broadcast packets. Now the RARP server attempt to find out the entry in IP to MAC address mapping table. If any entry matches in table, RARP server send the response packet to the requesting device along with IP address.
ICMP (Internet Control Message Protocol) is used for error reporting and diagnostics.
Feedback in the network is reported to the designated host. Meanwhile, if any kind of error occur it is then reported to ICMP. ICMP protocol consists of many error reporting and diagnostic messages. ICMP protocol handles various kinds of errors such as time exceeded, redirection, source quench, destination unreachable, parameter problems etc
IGMP (Internet Group Management Protocol) manages multicast group memberships.
Other hosts connected in the network and routers makes use of IGMP for multicasting communication that have IP networks. In many networks multicast routers are used in order to transmit the messages to all the nodes. Multicast routers therefore receives large number of packets that needs to be sent. But to broadcast this packets is difficult as it would increase the overall network load. Therefore IGMP helps the multicast routers by addressing them while broadcasting. As multicast communication consists of more than one senders and receivers the Internet Group Message Protocol is majorly used in various applications such as streaming media, web conference tools, games, etc.
Switching & Routing
Circuit Switching vs. Packet Switching
Circuit switching establishes a dedicated path between sender and receiver
A circuit-switched network is one of the simplest data communication methods in which a dedicated path is established between the sending and receiving device. In this physical links connect via a set of switches.
Packet switching divides data into packets and sends them independently.
In the Packet switching Network, the message is divide into packets. Each packet contains a header which includes the source address, destination address, and control information.
Distance Vector vs. Link State Routing
Distance vector routing uses neighboring nodes to determine the best path.
Link state routing has each node maintain a map of the entire network.
Routing table analysis (CIDR, subnet masks)
CIDR (Classless Inter-Domain Routing) and subnet masks help determine the destination network.
Analysis involves understanding how IP addresses are divided into network and host portions.
Transmission Media
Guided media (Twisted Pair, Coaxial, Fiber Optics)
Twisted pair cables are commonly used in Ethernet networks.
Coaxial cables are used for cable TV and older network installations.
Fiber optics use light to transmit data and offer high bandwidth and low attenuation.
Unguided media (Radio, Microwave, Infrared)
Radio waves are used for wireless communication over long distances.
Microwave transmission is used in satellite communications.
Infrared is used for short-range communication, such as remote controls.
OSI and TCP/IP Models
OSI Reference Model (7 layers)
Physical, Data Link, Network, Transport, Session, Presentation, Application.
TCP/IP Protocol Suite (layers and protocols)
Application, Transport, Internet, Network Access.
IP Addressing and Subnetting
IPv4 Classes and Format
Classes A, B, C, D, and E each have different ranges and network/host portions.
Subnetting with examples
Subnetting divides a network into smaller, more manageable subnets.
Longest prefix match routing decision
The router selects the route with the most specific (longest) prefix match.
Error Detection & Flow Control
Error Detection Techniques (Parity, Checksum, CRC)
Parity checks if the number of 1s is even or odd.
Checksum adds the data units and checks the sum against a stored value.
CRC (Cyclic Redundancy Check) uses polynomial division to detect errors.
CRC working
CRC involves dividing the data by a generator polynomial and checking the remainder.
Flow Control
Stop-and-Wait: The sender sends one packet and waits for acknowledgment before sending the next.
Sliding Window: The sender can send multiple packets before receiving acknowledgments.
Network Standards and Protocols
IEEE 802.3 (Ethernet)
Frame format: includes preamble, destination address, source address, type, data, and CRC.
MAC addressing: unique hardware address assigned to each network interface.
IEEE 802.4 (Token Bus) vs. 802.5 (Token Ring)
Token Bus: uses a virtual ring topology over a bus.
Token Ring: uses a physical ring topology.
CSMA, CSMA/CD, CSMA/CA protocols
CSMA (Carrier Sense Multiple Access): listens before transmitting.
CSMA/CD (Collision Detection): detects collisions and retransmits.
CSMA/CA (Collision Avoidance): attempts to avoid collisions before they occur.
Signal Types and Conversion
Analog vs. Digital Signals
Analog signals are continuous.
Digital signals are discrete.
Signal Conversions
Digital-to-Digital
Digital-to-Analog (AM, FM, PM, QAM)
AM (Amplitude Modulation), FM (Frequency Modulation), PM (Phase Modulation), QAM (Quadrature Amplitude Modulation).
Analog-to-Digital
Analog-to-Analog
Encryption & Network Security
DES limitations
DES (Data Encryption Standard) has a small key size, making it vulnerable to attacks.
Data Encryption Standard (DES) is a symmetric block cipher. By ‘symmetric’, we mean that the size of input text and output text (ciphertext) is same (64-bits). The ‘block’ here means that it takes group of bits together as input instead of encrypting the text bit by bit. Data encryption standard (DES) has been found vulnerable to very powerful attacks and therefore, it was replaced by Advanced Encryption Standard (AES). It is a block cipher that encrypts data in 64 bit blocks. It takes a 64-bit plaintext input and generates a corresponding 64-bit ciphertext output. The main key length is 64-bit which is transformed into 56-bits by skipping every 8th bit in the key. It encrypts the text in 16 rounds where each round uses 48-bit subkey. This 48-bit subkey is generated from the 56-bit effective key. The same algorithm and key are used for both encryption and decryption with minor changes
Public Key Cryptography
Uses key pairs (public and private) for encryption and decryption. Example: RSA Algorithm.
Public key cryptography is a method of secure communication that uses a pair of keys, a public key, which anyone can use to encrypt messages or verify signatures, and a private key, which is kept secret and used to decrypt messages or sign documents. This system ensures that only the intended recipient can read an encrypted message and that a signed message truly comes from the claimed sender. Public key cryptography is essential for secure internet communications, allowing for confidential messaging, authentication of identities, and verification of data integrity
Quality of Service (QoS)
QoS Concepts
Ensuring certain levels of performance for network traffic.
Quality of Service (QoS) in Computer Network QoS is an overall performance measure of the computer network. Important flow characteristics of the QoS are given below: 1. Reliability If a packet gets lost or acknowledgement is not received (at sender), the retransmission of data will be needed. This decreases the reliability. The importance of the reliability can differ according to the application. For example: E- mail and file transfer need to have a reliable transmission as compared to that of an audio conferencing. 2. Delay Delay of a message from source to destination is a very important characteristic. However, delay can be tolerated differently by the different applications. For example: The time delay cannot be tolerated in audio conferencing (needs a minimum time delay), while the time delay in the e-mail or file transfer has less importance
3. Jitter The jitter is the variation in the packet delay. If the difference between delays is large, then it is called as high jitter. On the contrary, if the difference between delays is small, it is known as low jitter. Example: Case1: If 3 packets are sent at times 0, 1, 2 and received at 10, 11, 12. Here, the delay is same for all packets and it is acceptable for the telephonic conversation. Case2: If 3 packets 0, 1, 2 are sent and received at 31, 34, 39, so the delay is different for all packets. In this case, the time delay is not acceptable for the telephonic conversation. 4. Bandwidth Different applications need the different bandwidth. For example: Video conferencing needs more bandwidth in comparison to that of sending an e-mail. Integrated Services and Differentiated Service These two models are designed to provide Quality of Service (QoS) in the network. 1. Integrated Services( IntServ) Integrated service is flow-based QoS model and designed for IP. In integrated services, user needs to create a flow in the network, from source to destination and needs to inform all routers (every router in the system implements IntServ) of the resource requirement. Following are the steps to understand how integrated services works. I) Resource Reservation Protocol (RSVP) An IP is connectionless, datagram, packet-switching protocol. To implement a flow-based model, a signaling protocol is used to run over IP, which provides the signaling mechanism to make reservation (every applications need assurance to make reservation), this protocol is called as RSVP. ii) Flow Specification While making reservation, resource needs to define the flow specification. The flow specification has two parts: a) Resource specification It defines the resources that the flow needs to reserve. For example: Buffer, bandwidth, etc. b) Traffic specification It defines the traffic categorization of the flow. iii) Admit or deny After receiving the flow specification from an application, the router decides to admit or deny the service and the decision can be taken based on the previous commitments of the router and current availability of the resource
The two classes of services to define Integrated Services are: a) Guaranteed Service Class This service guarantees that the packets arrive within a specific delivery time and not discarded, if the traffic flow maintains the traffic specification boundary. This type of service is designed for real time traffic, which needs a guaranty of minimum end to end delay. For example: Audio conferencing.
b) Controlled Load Service Class This type of service is designed for the applications, which can accept some delays, but are sensitive to overload network and to the possibility to lose packets. For example: E-mail or file transfer. Problems with Integrated Services. The two problems with the Integrated services are: i) Scalability In Integrated Services, it is necessary for each router to keep information of each flow. But, this is not always possible due to growing network.
ii) Service- Type Limitation The integrated services model provides only two types of services, guaranteed and control-load.
The solutions to handle the problems of Integrated Services are explained below: 1. Scalability The main processing unit can be moved from central place to the edge of the network to achieve the scalability. The router does not need to store the information about the flows and the applications (or the hosts) define the type of services they want every time while sending the packets. 2. Service Type Limitation The routers, route the packets on the basis of class of services define in the packet and not by the flow. This method is applied by defining the classes based on the requirement of the applications.
Resource Reservation Protocol (RSVP) The RSVP is a signaling protocol, which helps IP to create a flow and to make resource reservation. It is an independent protocol and also can be used in other different model. RSVP helps to design multicasting (one to many or many to many distribution), where a data can be sent to group of destination computers simultaneously. For example: The IP multicast is technique for one to many communication through an IP infrastructure in the network. RSVP can be also used for unicasting (transmitting a data to all possible destination) to provide resource reservation for all types of traffic.
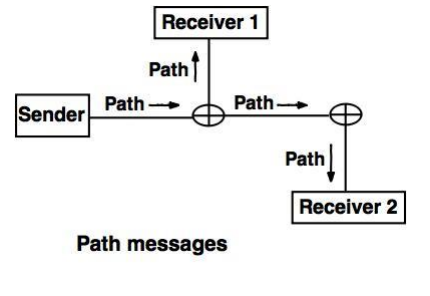
Path message : A path message travels from the sender and reaches to all receivers by multicasting and path message stores the necessary information for the receivers.
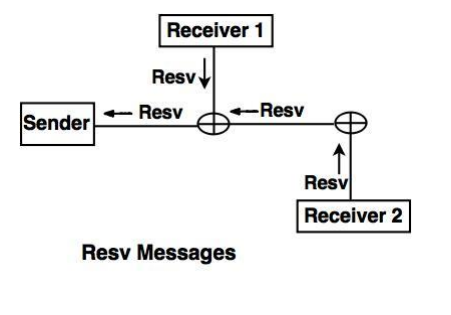
2. Resv messages: After receiving path message, the receiver sends a Resv message. The Resv message travels to the sender and makes a resource reservation on the routers which supports for RSVP.
Techniques (e.g., traffic shaping, priority queuing)
Traffic shaping: controls the rate of traffic.
Priority queuing: gives higher priority to certain types of traffic.
Integrated Services (IntServ)
Provides guaranteed QoS for individual flows.
Network Architecture Models
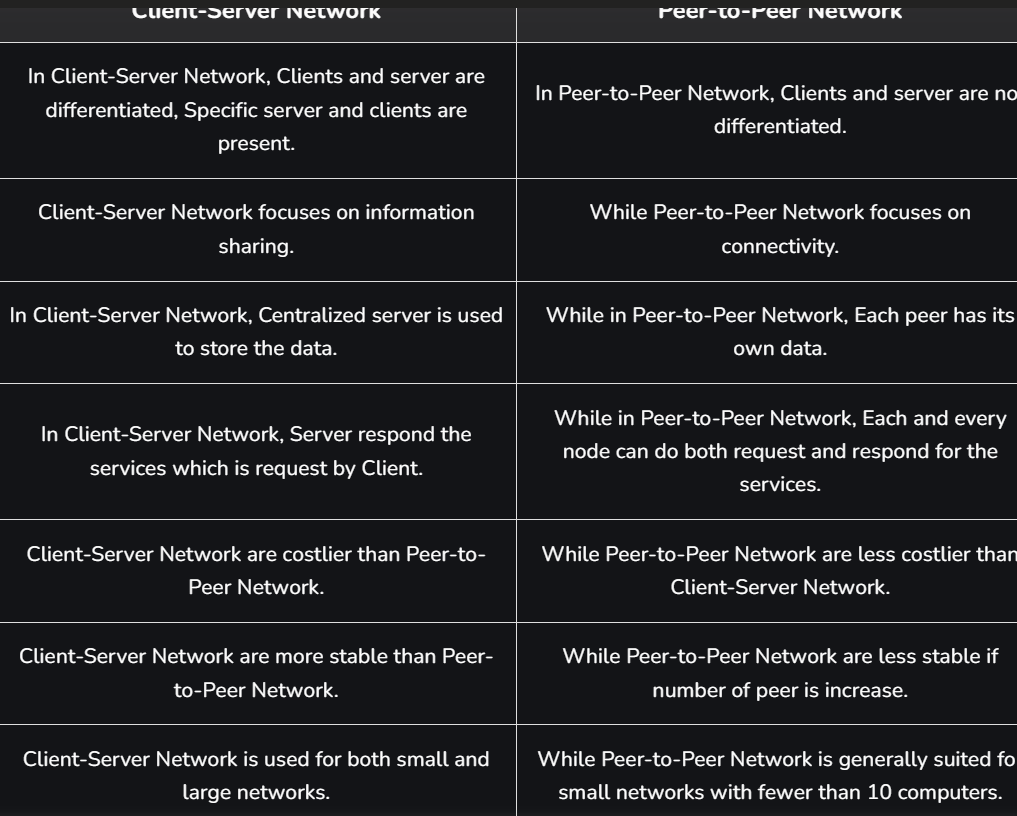
Client-Server vs. Peer-to-Peer
Client-Server: server provides resources to clients.
Peer-to-Peer: each node can act as both client and server.
The P2P process deals with a network structure where any participant in the network known as a node acts as both a client and a server. This means that, rather than relying on a basis server to supply resources or services, everybody from the network of nodes can trade resources and services with one another. In a P2P system, every node has an equal role to play and the same functionalities, which means that the loads are well shared.
Types of P2P Networks
Unstructured P2P Networks: In this type of P2P network, each device is able to make an equal contribution. This network is easy to build as devices can be connected randomly in the network. But being unstructured, it becomes difficult to find content. For example, Napster, Gnutella, etc.
Structured P2P Networks: It is designed using software that creates a virtual layer in order to put the nodes in a specific structure. These are not easy to set up but can give easy access to users to the content. For example, P-Grid, Kademlia, etc.
Hybrid P2P Networks: It combines the features of both P2P networks and client-server architecture. An example of such a network is to find a node using the central server.
In the P2P network architecture, the computers connect with each other in a workgroup to share files, and access to internet and printers. Each computer in the network has the same set of responsibilities and capabilities. Each device in the network serves as both a client and server. The architecture is useful in residential areas, small offices, or small companies where each computer act as an independent workstation and stores the data on its hard drive. Each computer in the network has the ability to share data with other computers in the network. The architecture is usually composed of workgroups of 12 or more computers
Applications in Web, FTP, DNS
Web (HTTP), FTP (File Transfer Protocol), DNS (Domain Name System).
Packet-Switched Network
Structure and data handling
Packets are routed independently across the network, and the network handles its data according to its configuration.