Encryption
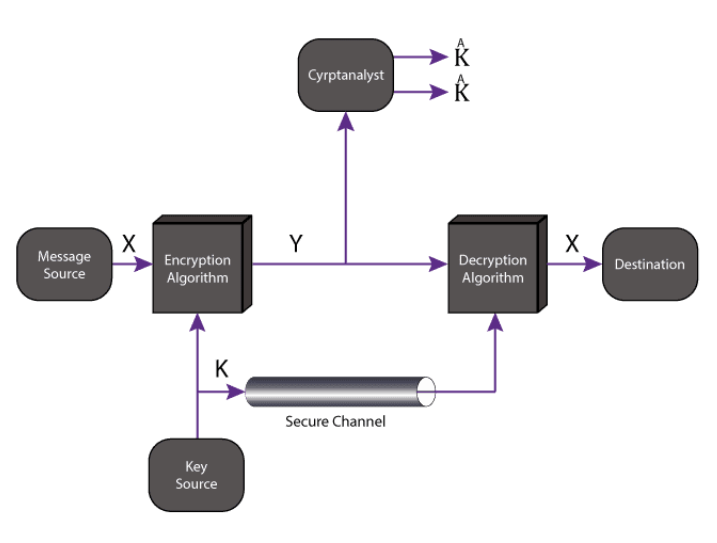
Symmetric encryption/ Private key model \n Requirements
- A Private key
- Three algorithms * A random Private key generator algorithm that generates a random key of a specified length (L): KeyGen(L) -> K * An encryption algorithm that takes the Private key (K) and the plaintext (M) and then returns a ciphertext (C): Enc(K, M) -> C * A decryption algorithm that takes the Private key (K) and the ciphertext (C) and then returns the original plaintext (M): Dec(K, C) -> M
\n Asymmetric encryption / Public key model \n Requirements
- A Private key and a Public key
- Four algorithms
* A random Private key generator algorithm that generates a random key of a specified length (L): KeyGen(L) -> Kₚᵣᵢᵥ
* A random Public key generator algorithm that generates a random key of a specified length (L): KeyGen(L) -> Kₚᵤb
* An encryption algorithm that takes the receiver's public key (Kₚᵤb) and the sender's plaintext (M) and then returns a ciphertext (C): Enc(Kₚᵤb, M) -> C
* A decryption algorithm that takes the receiver's private key (Kₚᵣᵢᵥ) and the ciphertext (C) and then returns the original plaintext (M): Dec(Kₚᵣᵢᵥ, C) -> M
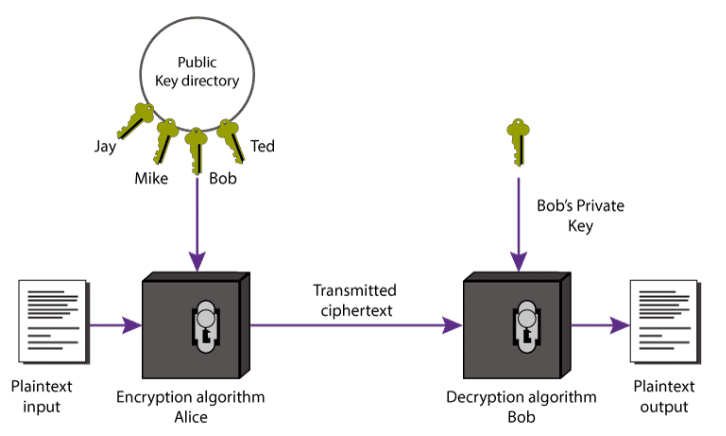
Good:
- key management is much simpler
- Alleviates the need to share secrets before communicating between parties
Bad:
- Much slower than Symmetric cryptography
\