Cisco Securing Networks
Module 1 Notes
General Data:
Networks face routine attacks, with various techniques employed by malicious actors.
Resources like Kaspersky’s Cyberthreat Real-Time Map track live attacks, highlighting the evolving landscape of threats.
Consequences of Security Breaches:
Significant disruption of e-commerce, resulting in financial losses and affected customer trust.
Permanent loss of data, leading to severe consequences for individuals and organizations.
Privacy threats that can compromise sensitive personal information.
Compromised information integrity, jeopardizing organizational decision-making processes and reputations.
Network Attack Vectors
Definition:
A path for threat actors to access servers, hosts, or networks, highlighting the critical need for robust security measures.
Typical Sources:
Both internal and external networks are vulnerable to attacks, with common methods including Denial of Service attacks that can cripple network functionality.
Data Loss Issues
Common Vectors for Data Loss:
Email/Social Media: Intercepted communications that can reveal sensitive data, making user awareness critical.
Unencrypted Devices: Loss of devices like laptops leads to data exposure, underscoring the importance of encryption and data protection features.
Cloud Storage: Weak security can lead to unauthorized access to sensitive information, necessitating strong security protocols.
Removable Media: Risks from unauthorized data transfer or loss of USB drives, emphasizing the need for caution with portable storage devices.
Hard Copy: Improperly disposed documents that can be accessed by unauthorized individuals, highlighting the importance of document shredding and secure disposal methods.
Access Control Issues: Weak passwords allow easy data access for attackers, creating vulnerabilities that can be easily exploited.
Network Topology Overview :
Campus Area Networks (CAN):
Utilize VPNs for data integrity; protected by ASA firewalls and monitored by Intrusion Prevention Systems (IPS) to ensure real-time threat detection.
Small Office/Home Office (SOHO):
Secured via consumer-grade routers with integrated firewalls and WPA2 encryption to enhance security and protect user data.
Wide Area Networks (WANs):
Require robust secure transport mechanisms due to their expansive geographic nature, necessitating extensive security measures.
Data Centers:
Ensure physical and logical separation of networks to protect sensitive data with strong security protocols and measures.
Virtualization and Cloud Networks :
Key Concepts:
Virtualization forms the foundation of cloud computing, enabling diverse operating systems to run on single hardware, simplifying resource allocation and management.
Security Threats to VMs:
Hyperjacking, outdated security policies on activation, and antivirus storms pose significant risks to virtual machines, necessitating stringent security practices.
Borderless Network Concept :
BYOD (Bring Your Own Device):
Facilitates connectivity from various devices anywhere, fostering a flexible work environment but increasing security challenges.
Requires thorough Mobile Device Management (MDM) to enforce security measures, ensuring devices access organizational resources in a secure manner.
Data Encryption: Only devices supporting encryption allowed, minimizing the risk of unauthorized access.
PIN Enforcement: Enhances access security, requiring users to authenticate their devices securely.
Data Wipe: Remotely erasing data on lost devices to mitigate the risk of data theft.
Data Loss Prevention (DLP): Juxtaposes authorized data usage with critical data scenarios, reducing the likelihood of inadvertent data exposure.
Summary of Key Learnings
Network breaches significantly impact businesses and privacy, highlighting the necessity for improved security protocols.
Utilize tools from Cisco Talos for effective threat analysis and mitigation strategies to safeguard networks.
Implement DLP controls that combine various measures for comprehensive security coverage.
Ensure both physical and network security in data centers to safeguard critical infrastructure and sensitive information.
Understand vulnerabilities unique to virtual machines and secure them accordingly to prevent exploitation.
Foster a Borderless Network for user access from multiple locations while implementing associated security measures to protect the organization's assets.
Module 2: Cisco Securing Networks
Four common ways to manage risk are listed below
Risk Avoidance: Implement controls that eliminate or mitigate risks to reduce the potential for loss.
Risk Transfer: Shift the risk to a third party, such as through insurance or outsourcing.
Risk Acceptance: Acknowledge the risk and decide to accept it, often after weighing the potential benefits against the risks.
Risk Reduction: Implement measures to reduce the impact or likelihood of risks occurring.
Hacker vs Threat Actor
Hacker: An individual who gains unauthorized access to systems or networks, often for malicious purposes.
Threat Actor: A broader term encompassing any entity that conducts malicious activities against a network, including hackers, nation-states, and organized crime groups.
3 diff types of hackers : white hat, gray hat, and black hat hackers
White Hat Hackers: Ethical hackers who use their skills to improve security by finding and fixing vulnerabilities with permission from the organization.
Gray Hat Hackers: Individuals who may violate ethical standards or laws but do not have malicious intent; they may exploit vulnerabilities but inform the organization afterward.
Black Hat Hackers: Criminal hackers who exploit vulnerabilities for personal gain or malicious intent, often causing damage or theft.
Threat Actor
Cybersecurity TasksCybersecurity TasksScript Kiddies: Inexperienced hackers who use existing scripts or tools developed by others to launch attacks, often lacking the technical skills to create their own exploits.
Hacktivists: Hacktivists are grey hat hackers who rally and protest against different political and social ideas.
State- Sponsored are State-Sponsored hackers are threat actors who steal government secrets, gather intelligence.
Cybercriminals is a term for black hat hackers who are either selfemployed or working for large cybercrime organizations.
bVulnerability Brokers are grey hat hackers who attempt to discover exploits and report them to vendors, sometimes for prizes or rewards.
Cybersecurity Tasks
• Use a trustworthy IT vendor
• Keep security software up-to-date
• Perform regular penetration tests
• Back up to cloud and hard disk
• Periodically change WIFI password
• Keep security policy up-to-date
• Enforce use of strong passwords
• Use two factor authentication
Indicators of attack
IOCs can be features that identify the f
ollowing:
• malware files
• IP addresses of servers that are used in attacks
• filenames
• characteristic changes made to end system software
Indicators of attack (IOA) focus more on the motivation behind an attack and the potential means by which threat actors have, or will, compromise vulnerabilities to gain access to assets. IOAs are concerned with the strategies that are used by attackers.
Categories of Attacks
man-in-the-middle attack
Compromised key attack
sniffer attack
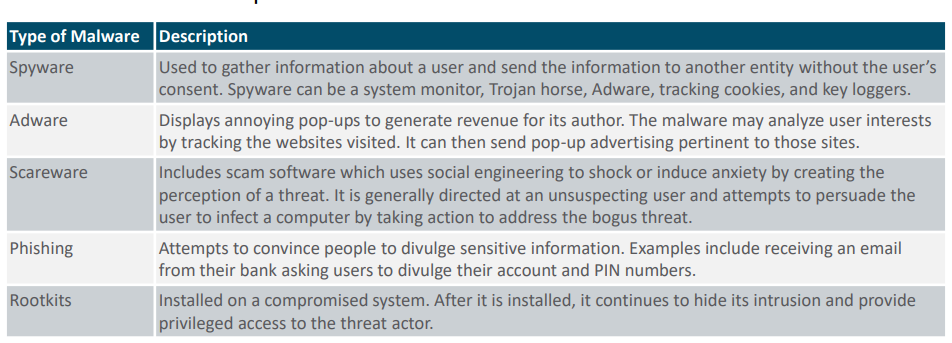
Malware
Types of Malware :
• virus
• worm
• Trojan horse
Types of Network Attacks
•Reconnaissance Attacks - information gathering
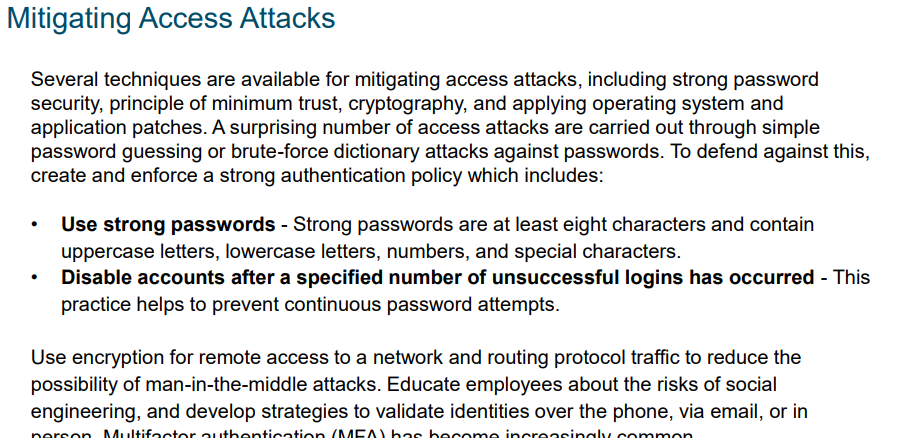
•Access Attacks - Access attacks explox zit known vulnerabilities in authentication services, FTP services, and web services to gain entry to web accounts, confidential databases, and other sensitive information.
•DoS Attacks
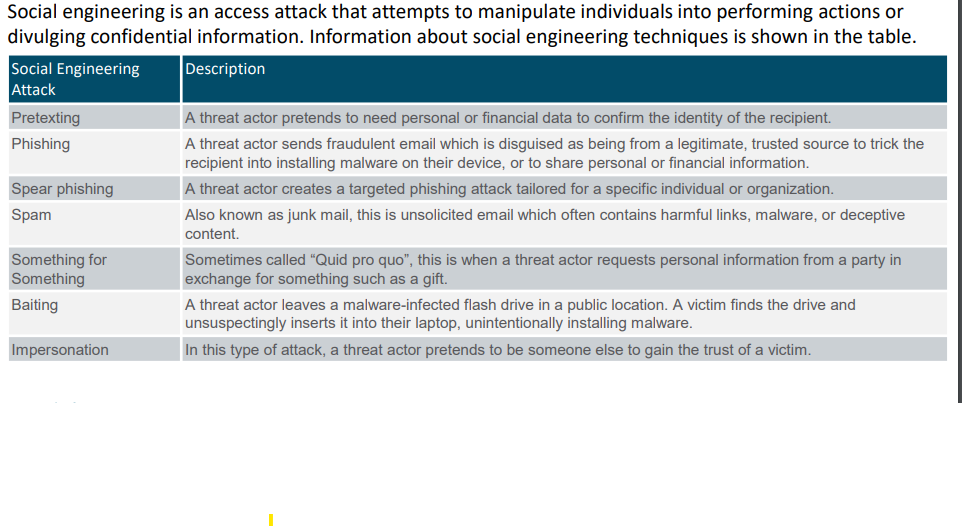
Social Engineering Attacks
Social engineering is an access attack that attempts to manipulate individuals into performing actions or divulging confidential information. Information about social engineering techniques is shown in the table
DoS and DDoS Attacks
A Denial of Service (DoS)
There are two major types of DoS attacks:
•Overwhelming Quantity of Traffic
•Maliciously Formatted Packets
A Distributed DoS Attack (DDoS) is like a DoS attack, but it originates from multiple, coordinated sources.
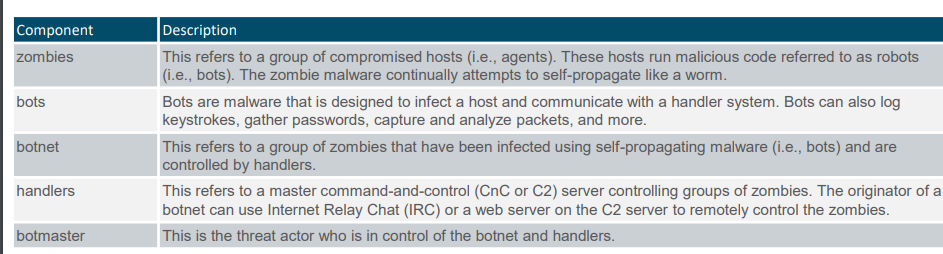
Components of DDoS Attacks
Buffer Overflow Attack
The goal of a threat actor when using a buffer overflow DoS attack is to find a system memoryrelated flaw on a server and exploit it. Exploiting the buffer memory by overwhelming it with unexpected values usually renders the system inoperable, creating a DoS attack. It is estimated that one third of malicious attacks are the result of buffer overflows.
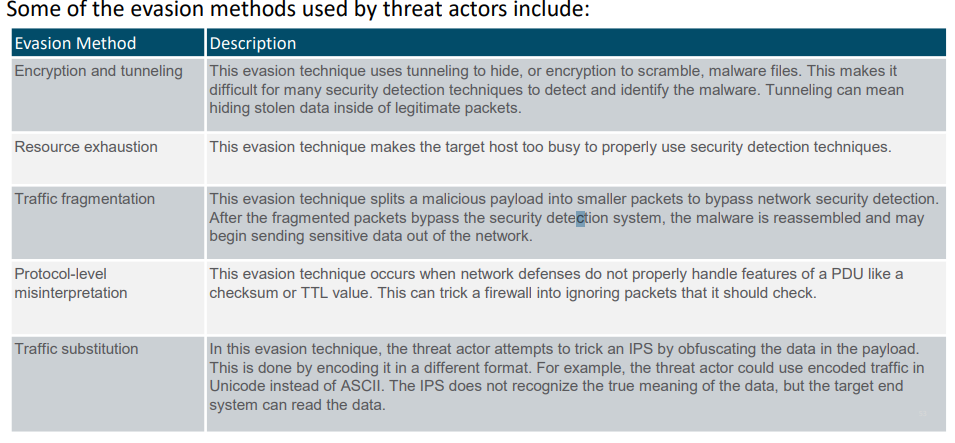
Evasion Methods
Summary
• Understanding network security requires you to understand the following terms: threat, vulnerability, attack surface, exploit, and risk.
• Four common ways to manage risk are risk acceptance, risk avoidance, risk reduction, and risk transfer.
• Threat actors include script kiddies, vulnerability brokers, hacktivists, cybercriminals, and state-sponsored hackers.
• Threat actors use a variety of attack tools including password crackers, wireless hacking tools, network security scanning and hacking tools, packet crafting tools, and many more.
• Categories of attacks include eavesdropping attacks, data modification attacks, IP address spoofing attacks, password-based attacks, denial-of-service attacks, man-in the-middle attacks, and others.
• Three common types of malware include are virus, worm, and Trojan horse. • A virus spreads by inserting a copy of itself into another program.
• Trojan horse malware is software that appears to be legitimate, but it contains malicious code that exploits the privileges of the user that runs it.
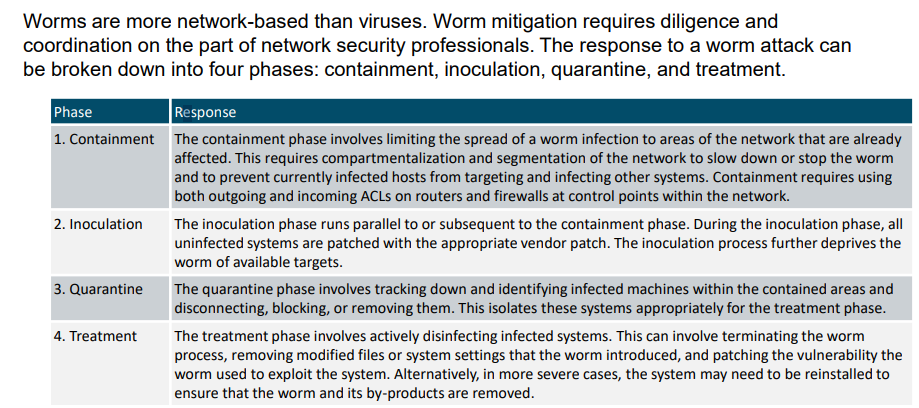
• Worms are similar to viruses because they replicate and can cause the same type of damage. Viruses require a host program to run. Worms can run themselves.
•Ransomware denies access to the infected system or its data and then demands payment to release the computer system.
• Reconnaissance is information gathering where threat actors perform unauthorized discovery and mapping of systems, services, or vulnerabilities.
• Access attacks exploit known vulnerabilities and include password attacks, spoofing attacks, trust exploitation attacks, and others.
• Social engineering is an access attack that attempts to manipulate individuals into performing unsafe actions or divulging confidential information and include pretexting, phishing, spam, impersonation, tailgating, shoulder surfing, dumpster diving, etc.
• There are two major types of DoS attacks: overwhelming quantity of traffic and maliciously formatted packets.
• DDoS attacks are similar in intent to DoS attacks, except that the DDoS attack increases in magnitude because it originates from multiple, coordinated sources.
• The following terms are used to describe DDoS attacks: zombies, bots, botnet, handlers, and botmaster.
• Evasion methods include encrypting and tunneling, resource exhaustion, traffic fragmentation, and more.
Module 3: Mitigating Threats
Network Security Professionals
• They must constantly upgrade their skill set to keep abreast of the latest threats.
• They must attend training and workshops.
• They must subscribe to real-time feeds regarding threats.
• They must peruse security websites daily.
• They must maintain familiarity with network security organizations. These organizations often have the latest information on threats and vulnerabilities.
Defending the Network
• Develop a written security policy for the company.
• Educate employees about the risks of social engineering, and develop strategies to validate identities over the phone, via email, or in person.
• Control physical access to systems.
• Use strong passwords and change them often.
• Encrypt and password-protect sensitive data.
• Implement security hardware and software such as firewalls, IPSs, virtual private network (VPN) devices, antivirus software, and content filtering.
• Perform backups and test the backed-up files on a regular basis.
• Shut down unnecessary services and ports.
• Keep patches up-to-date by installing them weekly or daily, if possible, to prevent buffer overflow and privilege escalation attacks.
• Perform security audits to test the network.
Mitigating Malwares
Module 4: Secure Device Access
The goal of a threat actor when using a buffer overflow DoS attack is to find a system memory related flaw on a server and exploit it. Exploiting the buffer memory by overwhelming it with unexpected values usually renders the system inoperable, creating a DoS attack. It is estimated that one third of malicious attacks are the result of buffer overflows.
Three Areas of Router Security
Physical - Place the router and physical devices that connect to it in a secure locked room that is accessible only to authorized personnel.
• Operating System - Configure the router with the maximum amount of memory possible.
• Router Hardening - Ensure that only authorized personnel have access and that their level of access is controlled.
Secure Administrative Access
Restrict device accessibility • Log and account for all access • Authenticate access • Authorize actions • Present legal notification • Ensure the confidentiality of data
A router can be accessed for administrative purposes locally or remotely:
Module 6: Device Monitoring and Management
The Cisco IOS resilient configuration feature allows for faster recovery if someone maliciously or unintentionally reformats flash memory or erases the startup configuration file in nonvolatile random-access memory (NVRAM).
Lock Down a Router Using AutoSecure
The intent of CDP and LLDP is to make it easier for administrators to discover and troubleshoot other devices on the network. However, because of the security implications, these discovery protocols should be used with caution. - Edge devices are an example of a device that should have this feature disabled.
AutoSecure can lock down the management plane functions and the forwarding plane services and functions of a router.
Dynamic Routing Protocols
• Dynamic routing protocols perform several activities: including network discovery and maintaining routing tables.
• Important advantages of dynamic routing protocols are the ability to select a best path, and the ability to automatically discover a new best path when there is a change in the topology.
• A dynamic routing protocol allows the routers to automatically learn about these networks from other routers.
Types of Management Access
In-band - Information flows across an enterprise production network, the Internet, or both, using regular data channels.
• Out-of-band (OOB) - Information flows on a dedicated management network on which no production traffic resides
Notes
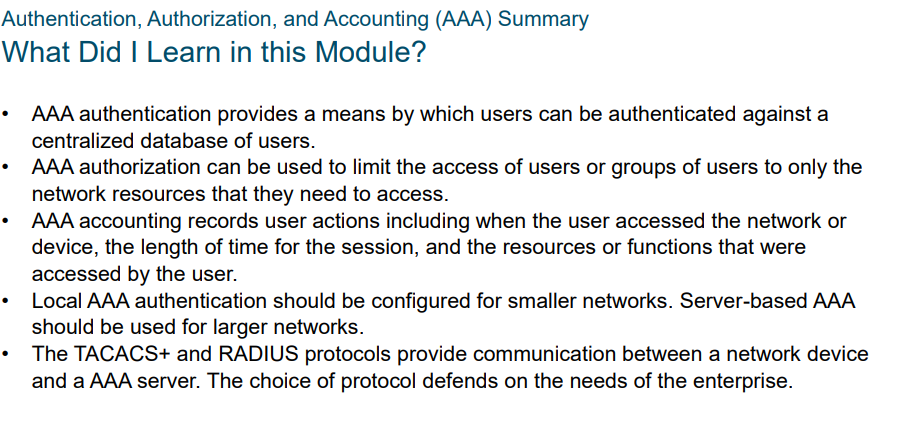
Module 7: Authentication, Authorization, and Accounting (AAA)
Cisco Identity Services Engine (ISE)
•Asset Visibility •Posture assessment
•Segmentation •Guest management and secure wireless
•Threat Containment
Module 8: Access Control Lists
Numbered and Named ACLs
Module 9: Secure Network with FireWalls
Types of Firewalls:
Packet Filtering (Stateless) firewalls based on Layer 3 and Layer 4
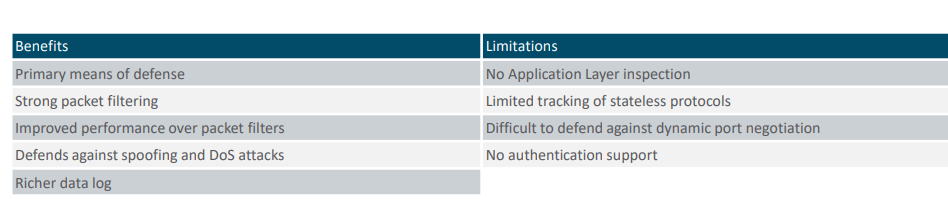
Stateful firewalls - common firewall technologies
Application Gateway (Proxy) – These filter information at Layers 3, 4, 5, and 7.
Next Generation firewalls - by providing integrated intrusion prevention, application awareness and control,
Benefits of Packet Filtering Firewalls
• They implement simple permit or deny rule sets.
• They have a low impact on network performance.
• They are easy to implement and are supported by most routers.
• They provide an initial degree of security at the network layer.
• They perform many of the tasks of a high-end firewall at a much lower cost.
Limitations of Packet Filtering Firewalls
• They are susceptible to IP spoofing.
• They do not reliably filter fragmented packets.
• They use complex ACLs, which can be difficult to implement and maintain.
• They cannot dynamically filter certain services.
• They are stateless.
three common firewall designs:
• Private and Public
• Demilitarized Zone (DMZ)
• Zone-Based Policy
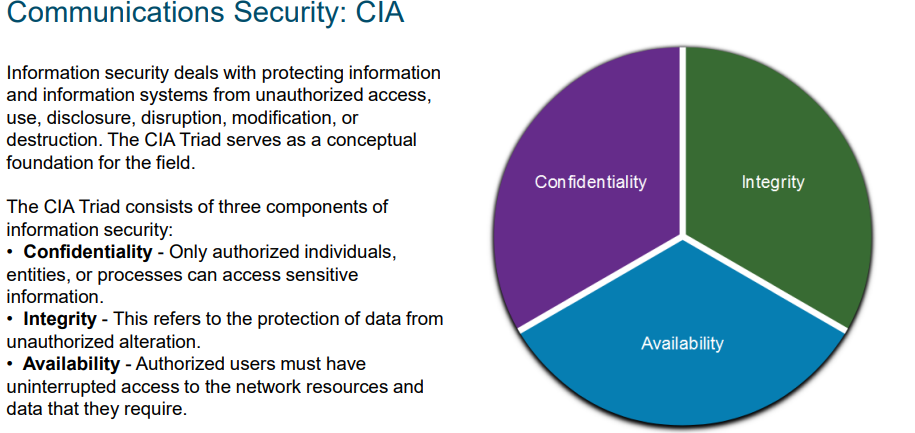
Layered Defense:
1. Network Core security - Protects against malicious software and traffic anomalies, enforces network policies, and ensures survivability
2.Perimeter security - Secures boundaries between zones
3. Communications security - Provides information assurance
4.Endpoint security- Provides identity and device security policy compliance
This partial list of best practices can serve as a starting point for a firewall security policy.
• Position firewalls at security boundaries. Firewalls are a critical part of network security, but it is unwise to rely exclusively on a firewall for security.
• Deny all traffic by default.
• Permit only services that are needed.
• Ensure that physical access to the firewall is controlled.
• Regularly monitor firewall logs.
• Practice change management for firewall configuration changes.
• Remember that firewalls primarily protect from technical attacks originating from the outside.
Module 10: Zone-Based Policy Firewalls
ZPF Overview
• Classic Firewall - The traditional configuration model in which firewall policy is applied on interfaces.
• Zone-based Policy Firewall (ZPF) - The new configuration mode in which interfaces are assigned to security zones, and firewall policy is applied to traffic moving between the zones.
Benefits:
It is not dependent on ACLs
he router security posture is to block unless explicitly allowed.
Virtual and physical interfaces can be grouped into zones.
Policies are applied to unidirectional traffic between zones
ZPF Actions:
Three possible actions: Inspect,Drop,Pass
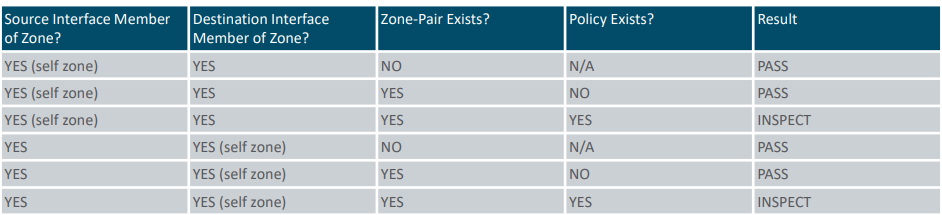
Transit Traffic
Rules for Transit Traffic
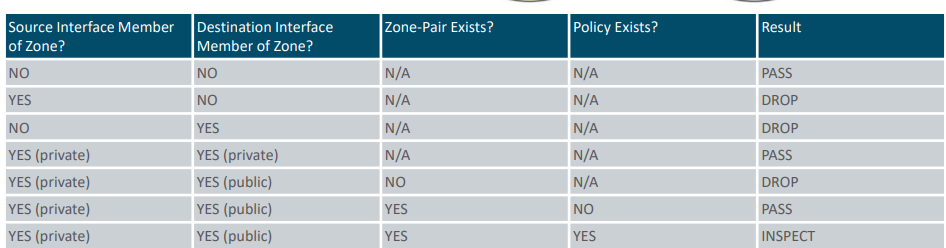
Rules for Traffic to the Self Zone