Network commands Basic Network Commands
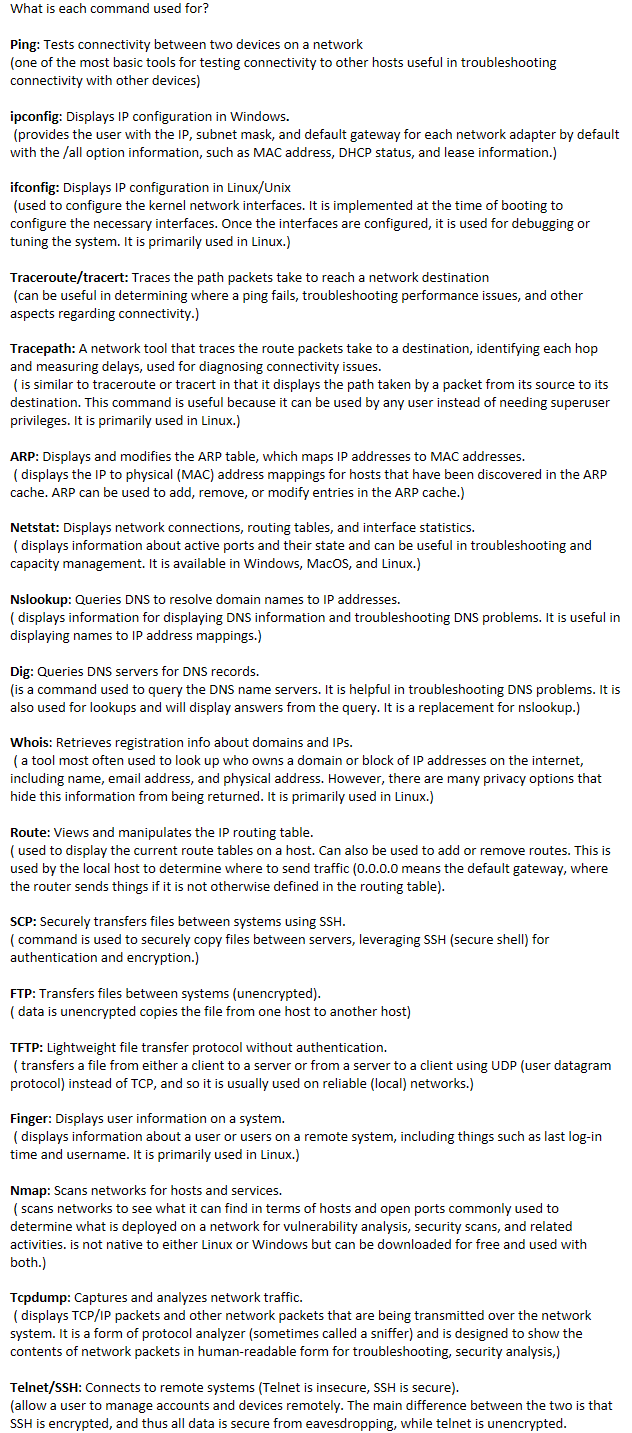
What is each command used for?
Ping: Tests connectivity between two devices on a network
(one of the most basic tools for testing connectivity to other hosts useful in troubleshooting connectivity with other devices)
ipconfig: Displays IP configuration in Windows.
(provides the user with the IP, subnet mask, and default gateway for each network adapter by default with the /all option information, such as MAC address, DHCP status, and lease information.)
ifconfig: Displays IP configuration in Linux/Unix
(used to configure the kernel network interfaces. It is implemented at the time of booting to configure the necessary interfaces. Once the interfaces are configured, it is used for debugging or tuning the system. It is primarily used in Linux.)
Traceroute/tracert: Traces the path packets take to reach a network destination
(can be useful in determining where a ping fails, troubleshooting performance issues, and other aspects regarding connectivity.)
Tracepath: A network tool that traces the route packets take to a destination, identifying each hop and measuring delays, used for diagnosing connectivity issues.
( is similar to traceroute or tracert in that it displays the path taken by a packet from its source to its destination. This command is useful because it can be used by any user instead of needing superuser privileges. It is primarily used in Linux.)
ARP: Displays and modifies the ARP table, which maps IP addresses to MAC addresses.
( displays the IP to physical (MAC) address mappings for hosts that have been discovered in the ARP cache. ARP can be used to add, remove, or modify entries in the ARP cache.)
Netstat: Displays network connections, routing tables, and interface statistics.
( displays information about active ports and their state and can be useful in troubleshooting and capacity management. It is available in Windows, MacOS, and Linux.)
Nslookup: Queries DNS to resolve domain names to IP addresses.
( displays information for displaying DNS information and troubleshooting DNS problems. It is useful in displaying names to IP address mappings.)
Dig: Queries DNS servers for DNS records.
(is a command used to query the DNS name servers. It is helpful in troubleshooting DNS problems. It is also used for lookups and will display answers from the query. It is a replacement for nslookup.)
Whois: Retrieves registration info about domains and IPs.
( a tool most often used to look up who owns a domain or block of IP addresses on the internet, including name, email address, and physical address. However, there are many privacy options that hide this information from being returned. It is primarily used in Linux.)
Route: Views and manipulates the IP routing table.
( used to display the current route tables on a host. Can also be used to add or remove routes. This is used by the local host to determine where to send traffic (0.0.0.0 means the default gateway, where the router sends things if it is not otherwise defined in the routing table).
SCP: Securely transfers files between systems using SSH.
( command is used to securely copy files between servers, leveraging SSH (secure shell) for authentication and encryption.)
FTP: Transfers files between systems (unencrypted).
( data is unencrypted copies the file from one host to another host)
TFTP: Lightweight file transfer protocol without authentication.
( transfers a file from either a client to a server or from a server to a client using UDP (user datagram protocol) instead of TCP, and so it is usually used on reliable (local) networks.)
Finger: Displays user information on a system.
( displays information about a user or users on a remote system, including things such as last log-in time and username. It is primarily used in Linux.)
Nmap: Scans networks for hosts and services.
( scans networks to see what it can find in terms of hosts and open ports commonly used to determine what is deployed on a network for vulnerability analysis, security scans, and related activities. is not native to either Linux or Windows but can be downloaded for free and used with both.)
Tcpdump: Captures and analyzes network traffic.
( displays TCP/IP packets and other network packets that are being transmitted over the network system. It is a form of protocol analyzer (sometimes called a sniffer) and is designed to show the contents of network packets in human-readable form for troubleshooting, security analysis,)
Telnet/SSH: Connects to remote systems (Telnet is insecure, SSH is secure).
(allow a user to manage accounts and devices remotely. The main difference between the two is that SSH is encrypted, and thus all data is secure from eavesdropping, while telnet is unencrypted.