Information Flow Control
Controlling the flow of data in order to ensure its confidentiality by monitoring the shared data
Information Channels
- Covert channels
- Timing channels
- Storage channels
\n
Information Flow Control is considered impractical as a form of access control because it's extremely difficult to stop covert channel attacks
\
Data Labels
In order for information control flow to work, we need to label each piece of data to indicate permitted information flows
- (ex: Where the data is from, where it's allowed to flow, etc.)
\ Data labelling specifies a set of policies:
Confidentiality Constraints
Who may read a given piece of data?
\
- Label example: {Alice: Bob, Eve; Charlie: Bob, Eve} * Alice and Charlie conjointly own a given set of data * Bob and Eve are permitted to read it
\
Integrity Constraints
Who may modify a given piece of data?
\
- Label Example: {Alice ? Bob} * Alice owns the given set of data * Bob is permitted to modify it
\
During Computation
During computation, an authorized entity can also rewrite part of the label
- Example: Alice and Bob own a piece of data
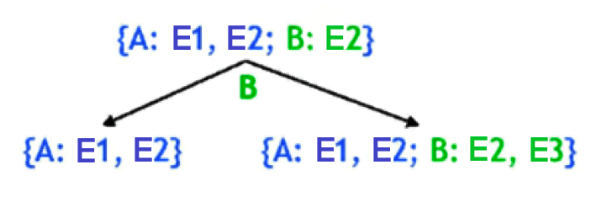
- Originally, Alice specified that Entity 1 (E1) and Entity 2 (E2) can access this data, meanwhile, Bob only specified Entity 2 (E2)
- However, Bob wants to add Entity 3 (E3) to this list of entities that can read this data
- In order to do so, Bob can rewrite his portion of the label
\ Labels can also get naturally propagated during computation
- Example: If you perform some action where you reassign X to equal Y, then X's labels are thrown away and they get the labels of Y
\