ISC^2 NOTES
CIA- Confidentiality, Integrity, and Availability
HIPAA- Health Insurance Portability and Acountability Act
GDPR- General Data Protection Regulation
Vulnerability- gap or weakness in an organizations protection of its valuable assets including info.
Threat- Something that aims to exploit a vulnerability to gain access.
Threat Vector: how a bad actor exploits a vulnerability
An asset: is something in need of protection.
A vulnerability: is a gap or weakness in those protection efforts.
A threat: is something or someone that aims to exploit a vulnerability to thwart protection efforts.
Risk Assessment: Analysis performed as part of risk management
treatment, avoidance (avoiding risk overall), mitigation(to some degree), transfer(outsourcing), and acceptance of risk
Prioritization of risk via: qualitative and quantitative risk
Risk Threshold: how much risk a company can take
SECURITY CONTROLS
3TYPES: PHYSICAL, ADMINISTRATIVE, AND TECHNICAL
Physical: guards, scanners, biometrics, and doors.
Technical: network topologies, ACL’s, and Technological protocol
Administrative: managerial controls, policies, and whatnot
ISO: International Organization for Standardization (ISO) develops and publishes international standards on a variety of technical subjects
NIST: National Institute of Standards and Technology (NIST) is a United States government agency under the Department of Commerce and publishes a variety of technical standards
IETF: Internet Engineering Task Force (IETF), there are standards in communication protocols that ensure all computers can connect with each other across borders
IEEE: Institute of Electrical and Electronics Engineers (IEEE) also sets standards for telecommunications, computer engineering, and similar disciplines.
Regulations=Law, Standard=Law, Policies= Guided by Law, Procedures= Necessary Operation.
ISC² PREAMBLE AND CANNONS
The safety and welfare of society and the
common good, duty to our principles, and
duty to each other require that we adhere
and be seen to adhere to the highest
ethical standards of behavior
CANNON:
Protect society, the common
good, necessary public trust and
confidence, and the infrastructure.
● Act honorably, honestly, justly,
responsibly, and legally.
● Provide diligent and competent
service to principles.
● Advance and protect the profession
Breach: loss of control, compromise, where a user access personally identifiable information for an unauthorized purpose.
Event: obeservable occurence in network or system.
Exploit: Attack that exploits systems vulnerabilities
Incident: An even that potentially jeopardizes the CIA of a system
Intrusion: security event where an intruder tries to gain access into a system
Threat:event with the potential to impede companies processes.
Zero-Day: Unknown vulnerability that cripples a system or can cause processes to stop.
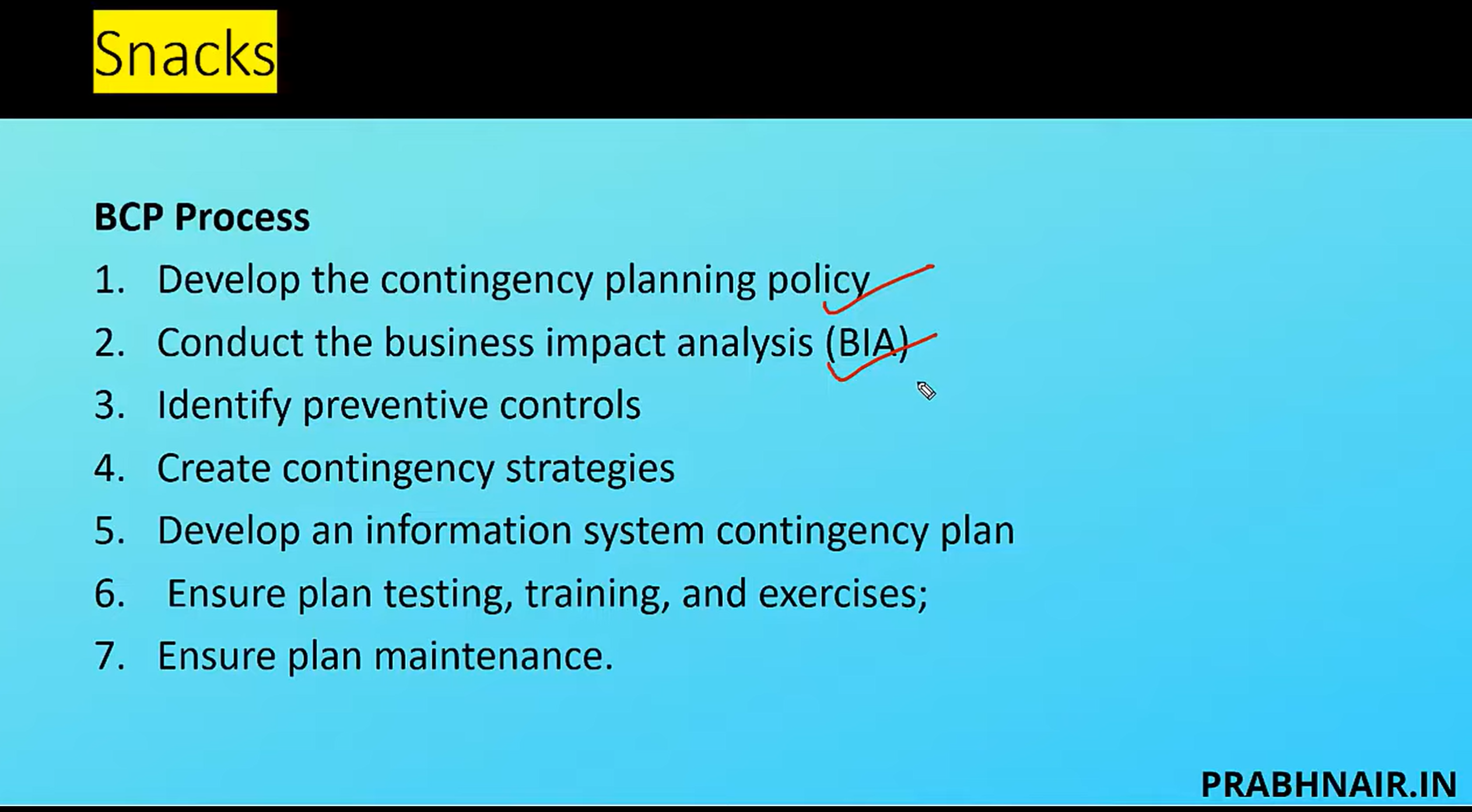
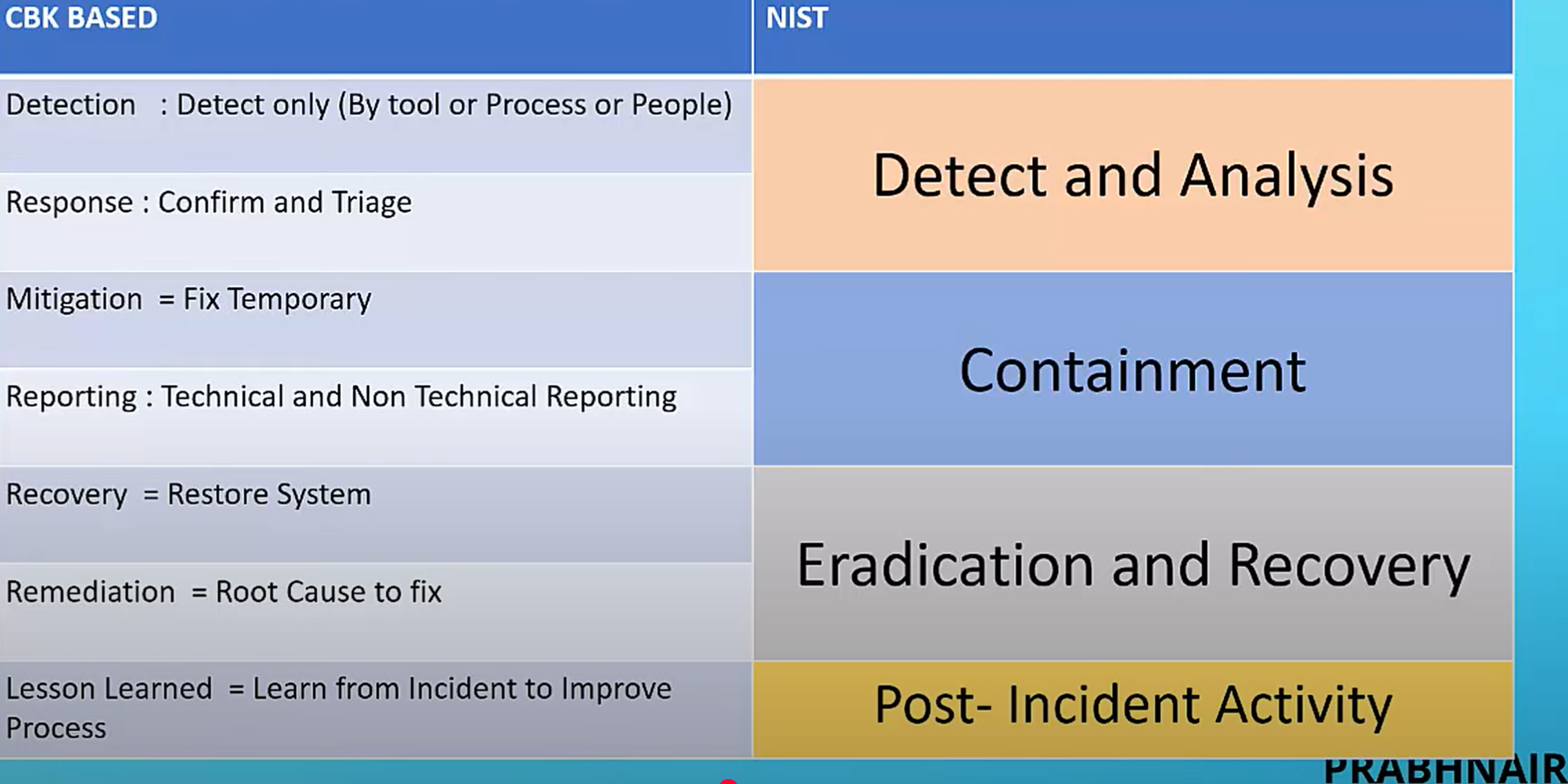
IRP- Incident Response Plan- Plan that tackles procedures in the event of an Incident.
Components found in Incident Response plans:
Preparation, Detection and Analysis, Containment Eradication and Recovery, and Post Incident Activity.
PDCP:
Preparation: policies put in place,
Detection and Analysis: Monitor Attack Vectors, Prioritize incident response Containment: Isolation of Attack, gather evidence
Post Incident Activity: Identify evidence that may need to be retained, documents lesson learned.
Teams Dedicated to Incident Response: CIRTS (Computer Incident Response Teams:
Determine the damage, Determine whether confidential info was compromised, implement any necessary recovery procedures, supervise the implementation of said actions.
RED BOOK: red book" typically refers to a logbook or notebook, often red-covered, used to document key business information and operations
Business Continuity: enabling critical aspects of an organization to fjunctions perhaps at a reduced capacity during a disruption caused by failures such as attacks or disasters.
Business Continuity Plan: planning for response and recovery for some, but not all, products and services of the business.
Disaster Recovery Plan (DRP) guides the actions of emergency response personnel until the end goal is reached—which is to see the business restored to full last-known reliable operations.
COMPONENTS OF BCP
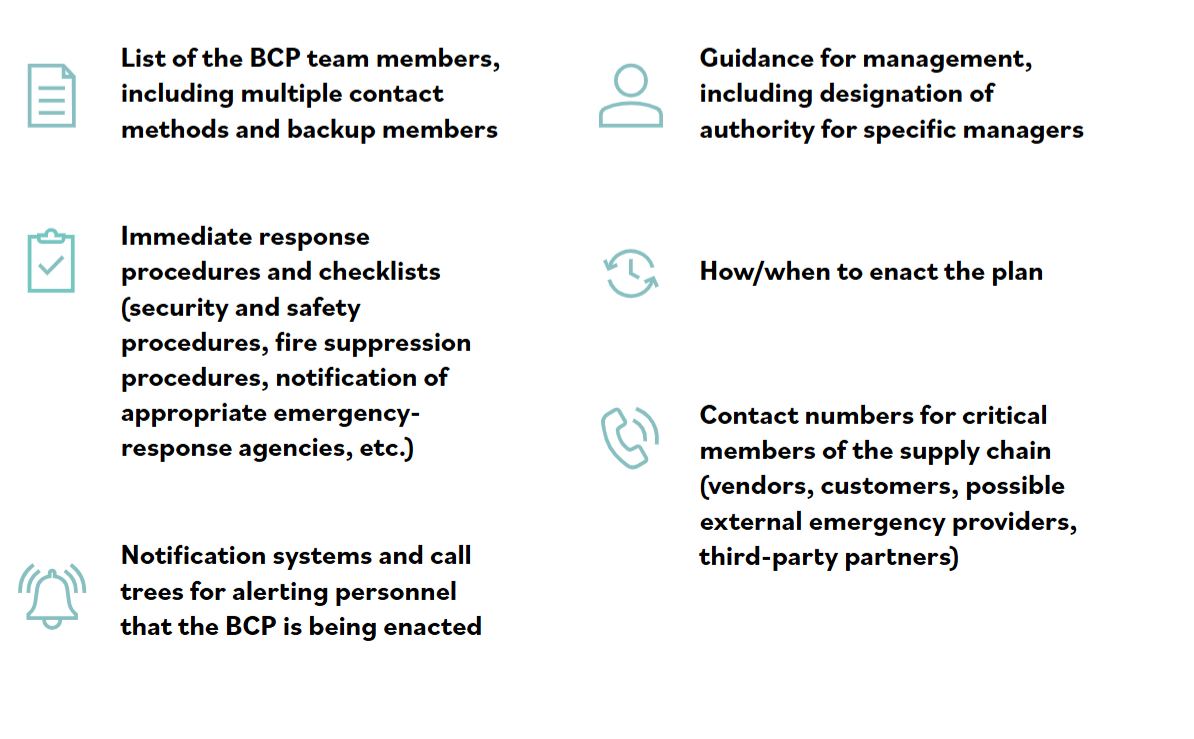
COMPONENTS OF DRP
Giving teams checklists, giving technical guides to IT, personell, full copies of plans to other members.
DOMAIN 3
Control: safeguard or countermeasure designed to preserve the Confidentiality, Integrity, and Availability of data
Access control: involves limiting what objects can be available to what subjects according to what rules
Access is based on 3 elements: Subjects, Objects, and Rules
Subjects: Entity requesting access to a system or resource, initiator of a request ( active )
Objects: anything that responds to a subject, or something a subject tries to request/ access (passive) waits for a subject request
Rules: Instructions put in place to deny or permit access to an object. (firewalls)
Defense in depth describes an information security strategy that integrates people, technology, and operational capabilities to establish variable barriers across multiple layers and missions of the organization. (Think MFA, Many factors of authentication)
Least Priviledge: What you need and nothing else
priviledged users should be- audited more, have to use more MFA, have to have deeper background checks, and should have records of activity kept for easy auditing.
Seperation of Duties: the idea that a high level transaction should not be done by one person or department. ( Separation of duties breaks the transaction into separate parts and requires a different person to execute each part of the transaction) Used to deter fraud
Collusion: when two or more parties agree to commit fraud by bypassing their seperation of duties
Dual Control: two people have different keys, combined together they can open an asset ( banks and vaults needing two people to open it)
2 person integrity: one person to surveil the other to ensure fraud is not commited.
Users are provisioned in 3 ways: new employee, change of position, and seperation of employment.
Crime Prevention Through Environmental Design (CPTED): Approaches the challenge of creating safer workspaces through passive design elements ( an environment that stimulates behavior)
Biometric uses Enrollment and Verification. Enrollment: code is stored biometrically in a system
Verification: biometric data is presented and verified
Logical Access Controls: electronic methods that limit someone from getting access to systems, and sometimes even to tangible assets or areas. ( passwords, badge readers)
DAC( Discretionary Access Control - Control policy that is enforced over all subjects and objects in an information system priviledge and control setting. security is up to the owner
MAC ( Mandatory Access Control) - Policy whereby Admins can modify security rules MAC= Admin Controlled, while DAC is owner controlled
RBAC- Role Based Access Control- Role-based access control provides each worker privileges based on what role they have in the organization
Privilege/Permissions Creep- When a user exceed their level of access via inheritance can be prevented by not copying old user profiles.
Network: two or more computers linked together that share data, info, or resources.
LAN- Local Area Network ( Network spanning a single floor or building)
WAN- Wide Area Network (Network spanning a large geographical area (think ex: russia and the U.S)
IEEE 802.3- standard that defines wired connections of networked devices
First 3 Bytes of a MAC 00-22-00 address denotes the manufacturer of the NIC
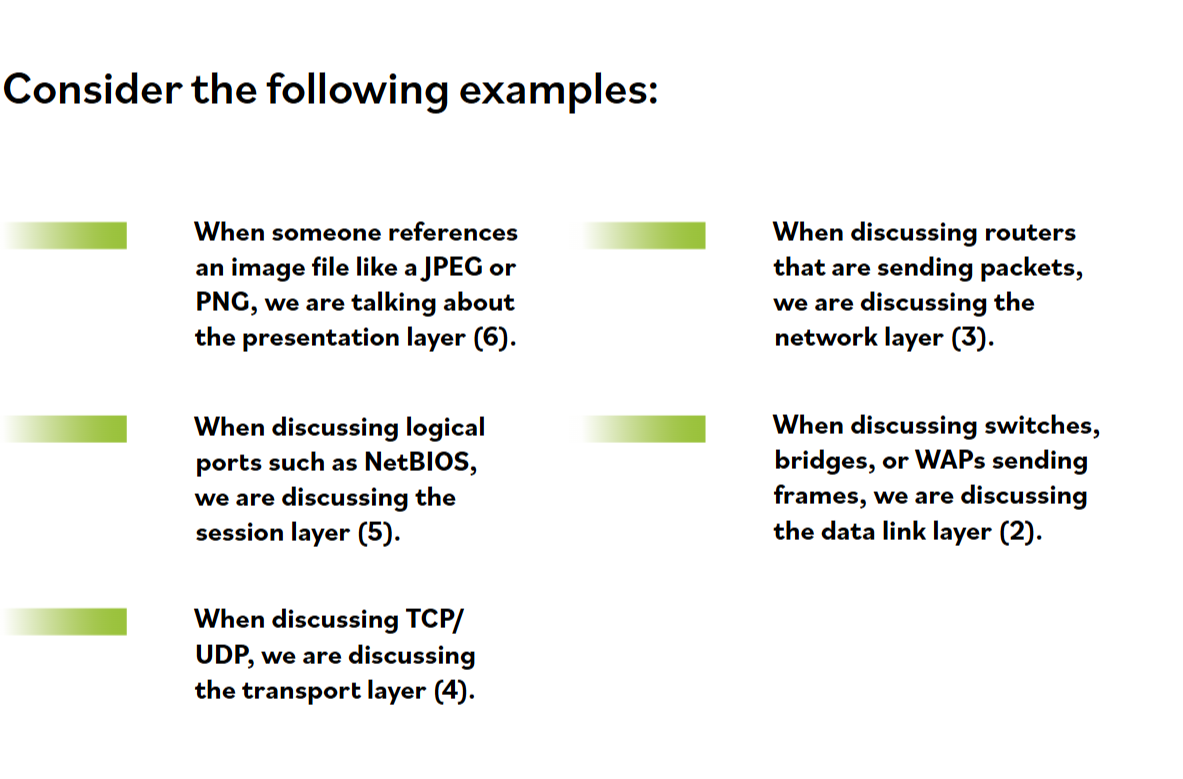
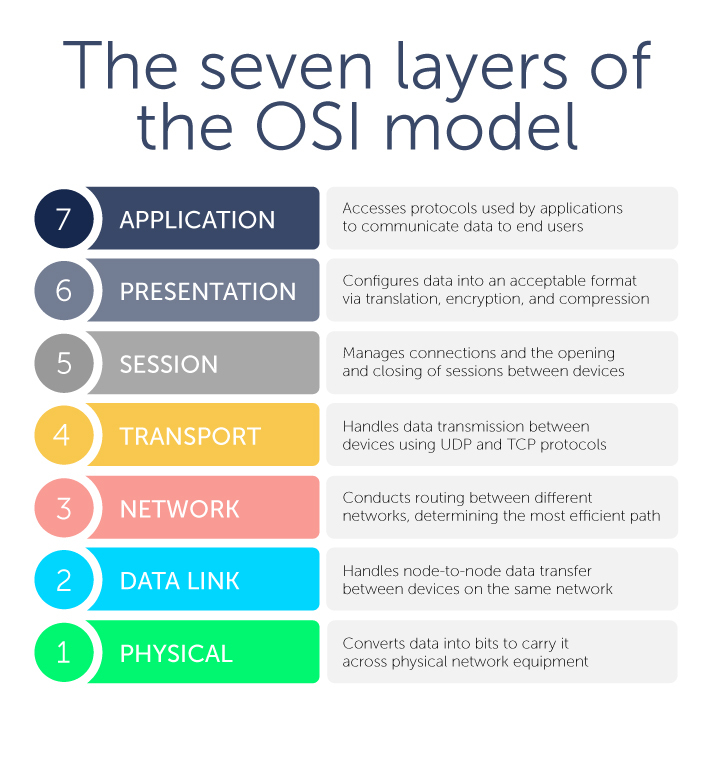
OSI Layers:Physical, Data Link, Network, Transport, Session, Presentation, and Application.
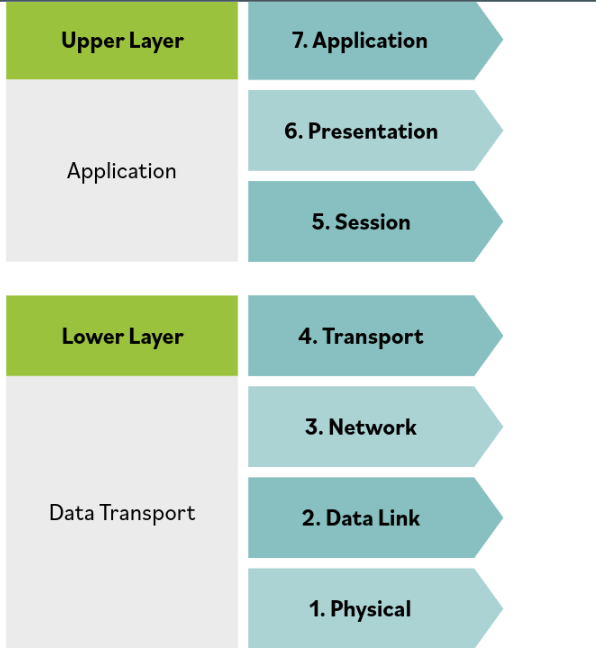
Upper Layer manages integrity of a connection and controls session
Lower Layer responsible for receiving bits and information and converting it to frames
OSI has 7 layers
Encapsulation- addition of header and footer data by a protocol used at that layer of the OSI Model.
De- encapsulation- happens as you go up the header data header and footer becomes less and less.
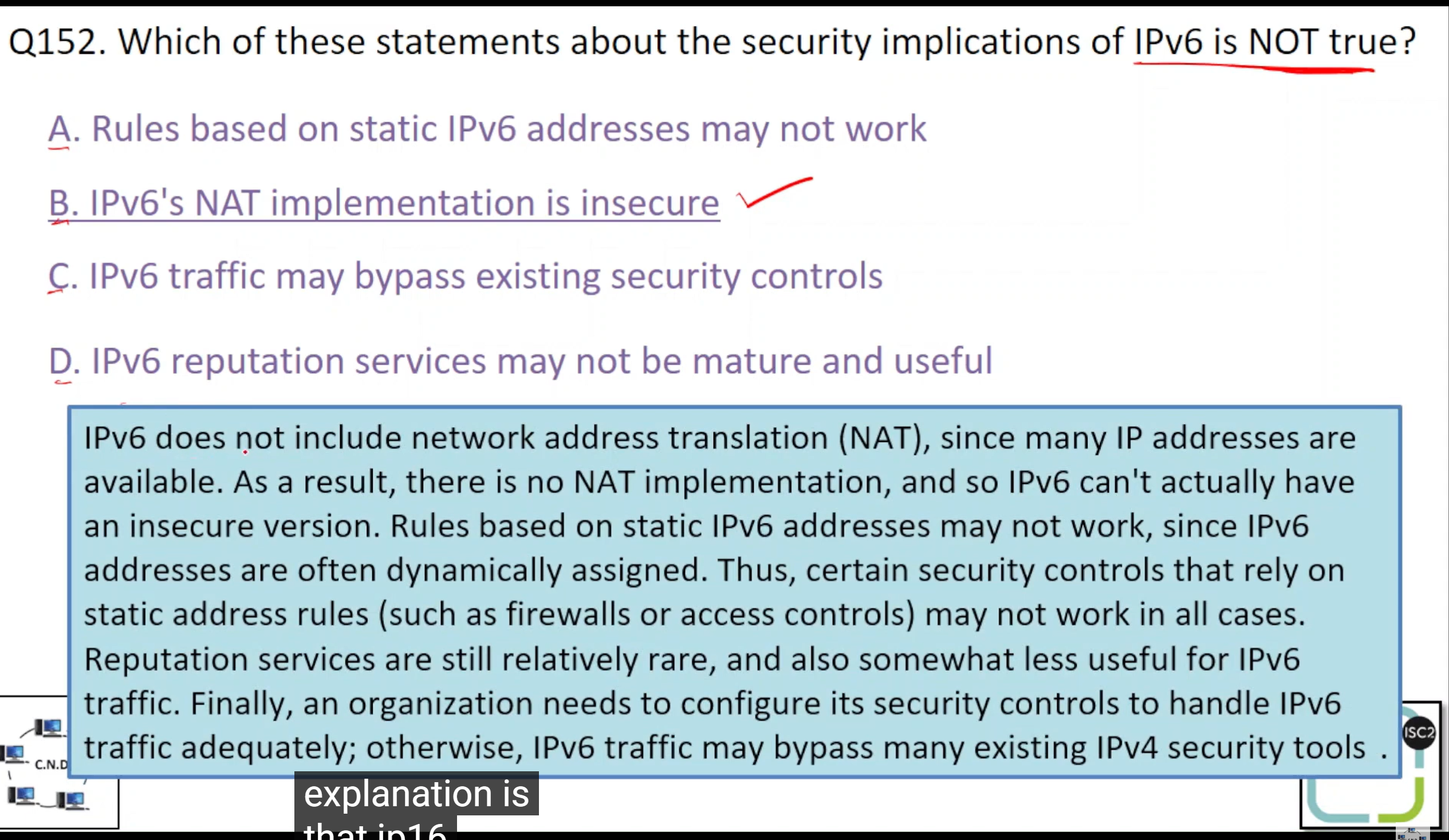
IPV4 = 32 bit 0-255, IPV6=128 bit
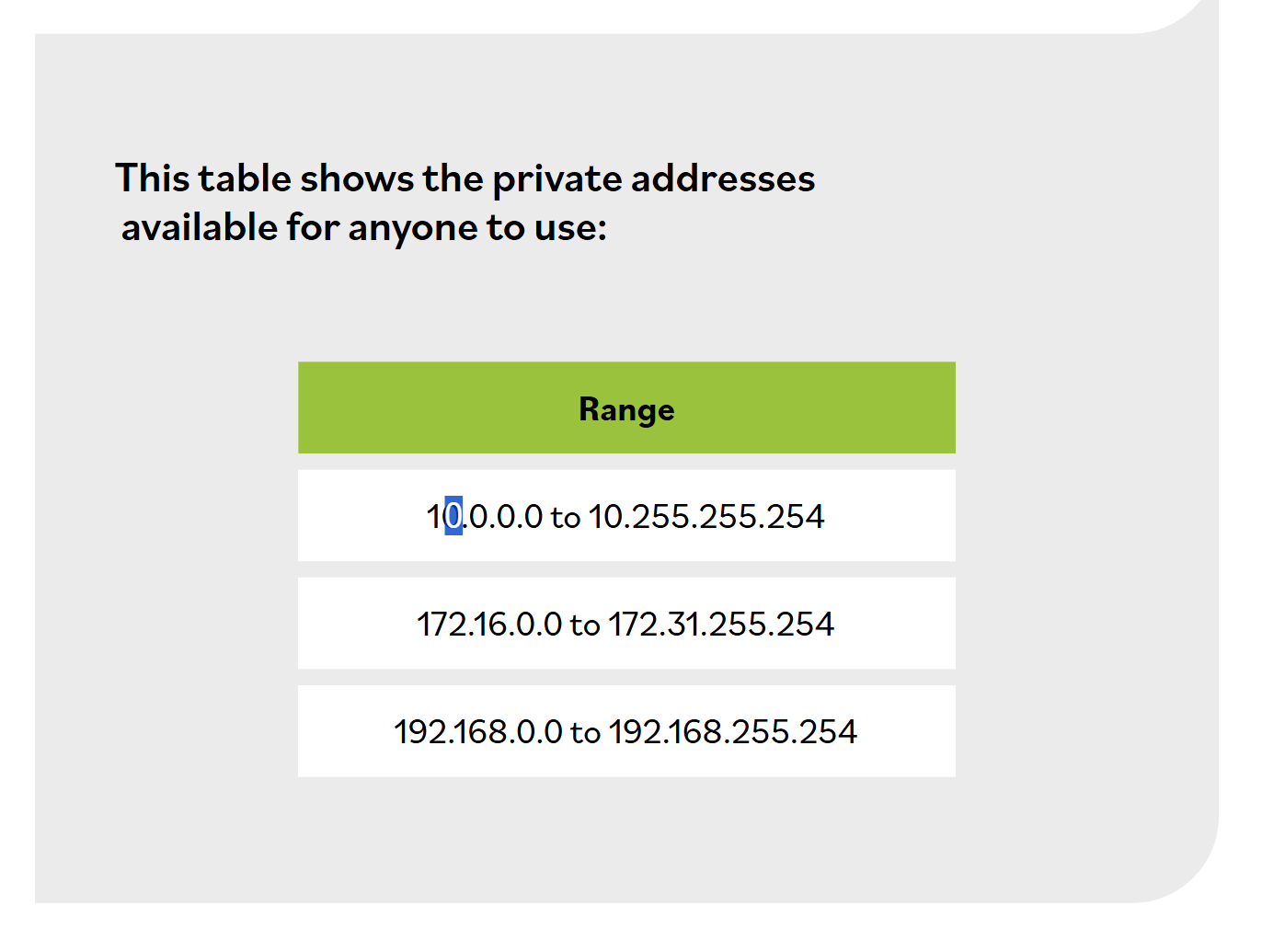
CLASS A, B, and C addresses
127.0.0.1 IPV4 loopback address used for self diagnosis
IPsec is a part of IPV6 MAC Address = 6×8 48 adress space
::1 IPV6 loopback 128 adress space
Network monitoring/sniffing= the act of monitoring patterns to obtain information about a network.
Physical Ports: ports on a switch or router where the cable is connected well known ports 0-1023 registered ports 1024-49151, dynamic ports: 49152-69535
LDAP SMB SNMP IMAP HTTP DNS TIME SMTP TELNET FTP
Service | Insecure Port | Secure Port |
|---|---|---|
LDAP | 389 | 636 (LDAPS) |
SMB | 445 | NFS over TLS (2049 Network File Storage) |
SNMP | 161 | 10161 (SNMPv3 with TLS) |
IMAP | 143 | 993 (IMAPS) |
HTTP | 80 | 443 (HTTPS) |
DNS | 53 | 853 (DoT), 443 (DoH) |
TIME | 37 | NTP uses 123 (with authentication) |
SMTP | 25 | 465 (SMTPS) or 587 (STARTTLS) |
TELNET | 23 | 22 (SSH as secure alternative) |
FTP | 21 | 990 (FTPS) or 22 (SFTP) |
SYN, SYN-ACK, ACK
spoofing = pretending to be someone else, phisihing = tricking others
THE CLIENT SENDS A SYN
THE SERVER SENDS A SYN ACK
THE CLIENT SENDS ACK
On Path Attack- Attackers place themselves between two devices
Side Channel- passive noninvasive attack that monitors systems
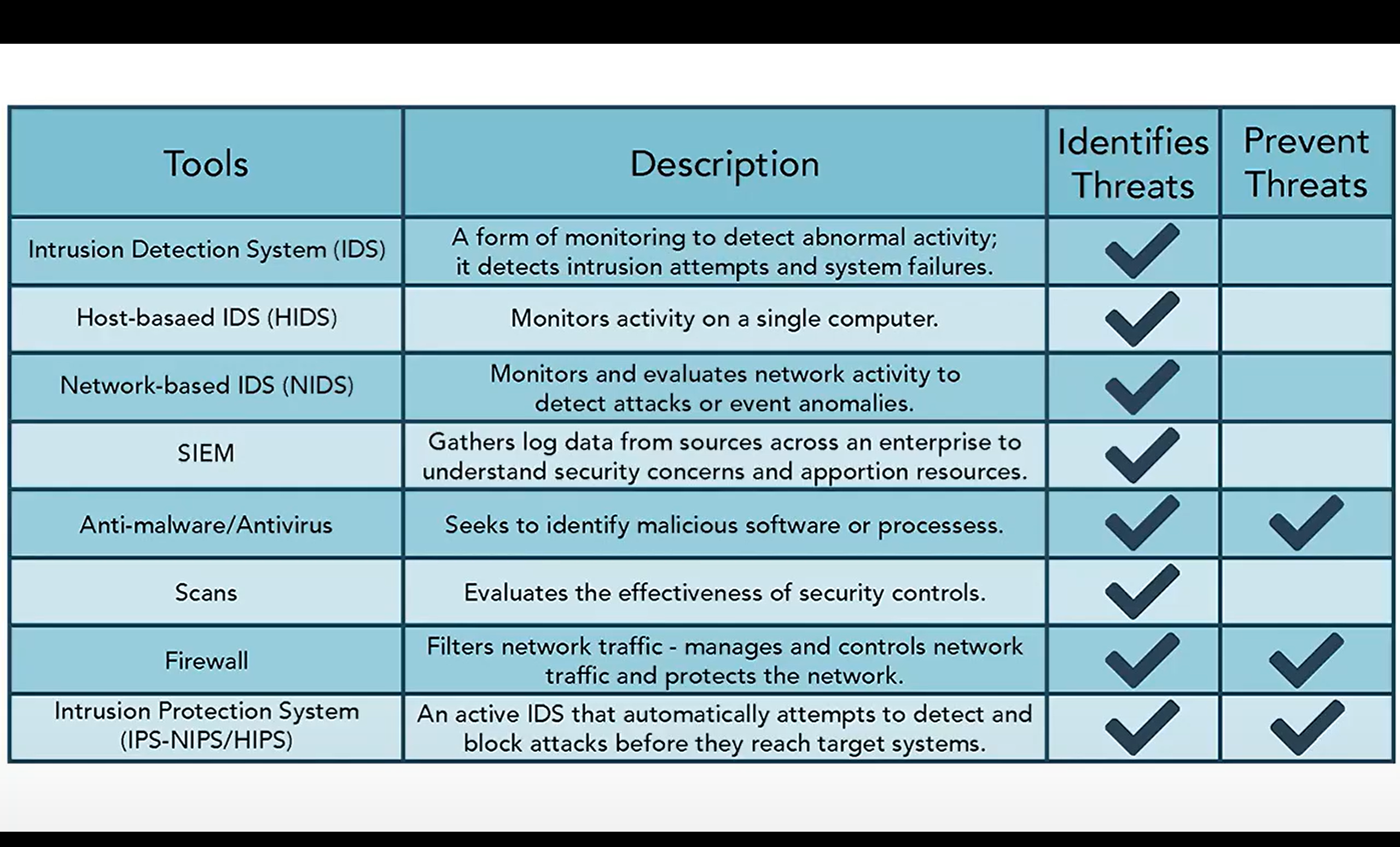
IDS are typically host based or network based
host based - monitors a system/computer
network based- monitors a network, SIEM - Security Information and Event Management - collect info about IT environment and respond based on necesary resource allocation ather log data from various sources across the enterprise to better understand potential security concerns and apportion resources accordingly.
HOW TO PREVENT INTRUSIONS: Update Applications, Remove or disable unnedded processes, use intrusion detection software, use firewalls, use up to date anti malware software, ANTIVIRUS ( requirement for PCI DSS)
IPS- Intrusion Prevention System- Prevents intrusion since all network traffic has to flow through it. Network IPS and Host based IPS (NIPS AND HIPS). IPS is placed in line with network traffic
DATA CENTERS: HVAC, POWER, FIRE SUPPRESSION, AND DATA RACKS.
Dry pipe systems is better for data centers, redundancy is a way to ensure proper operation when other components fail. Redundancy can be met by using UPS, and Generators
MOU, MOA, and JOA: (memorandum of agreement/understanding These are agreements in which two business or seperate facilities agree to use the other facilities infrastructure in the even of a disaster, ex hospitals relocating to another hospital due to flooding.
SLA -The cloud computing service-level agreement (cloud SLA) is an agreement between a cloud service provider and a cloud service customer based on a taxonomy of cloud computing–specific terms to set the quality of the cloud services delivered.
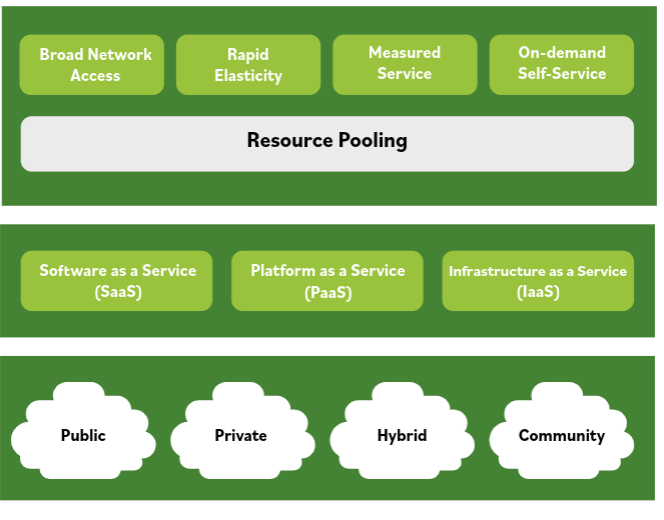
Cloud- rapid elasticity/ access to computing resources
Cloud models include: SaaS, PaaS, IaaS (
Hybrid cloud = A mix of your own private stuff (like your company's personal servers) and someone else's cloud (like Amazon AWS or Microsoft Azure) working together. It's like having some important files locked in a safe at home (private) but also storing some vacation photos on Google Drive (public). You use both, depending on what you need.
Community cloud = A shared cloud just for a specific group of people or organizations that have something in common. Think of it like a private clubhouse where only doctors, or only banks, or only schools are allowed. They all share the clubhouse because they have similar needs (like privacy rules), but it's not open to the public.
MSP- A company that manages information technology assets for another company (MDR) Managed Detection and Response. SLA- Service Level Agreement- manages the quality of services a company has to provide ( think of it like a legal binding contract with the granular detail of the quality provided by the company and outline of data destruction and so on.

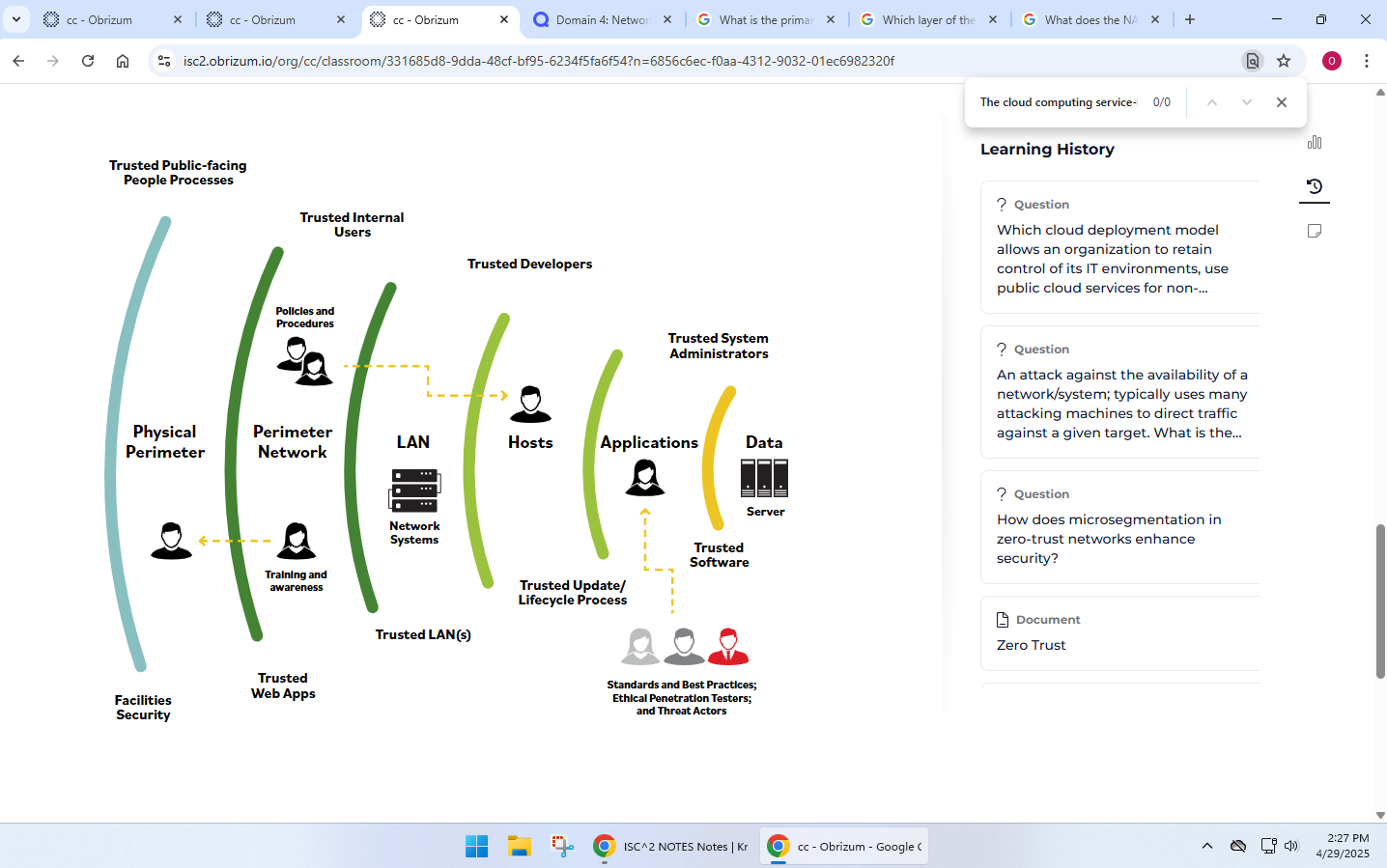
DMZ- Demilitarized Zone- a network area that is designed to be accessed by outside visitors but is still isolated from the private network of the organization.
Complete/Physical network segmentation- when a network is isolated from all outside communications, so transactions can only occure between devices withing the segmented network
VLANS- Created by switches to logically segment a network without altering its physical topology. Ex: VOIP VLAN, PAYROLL VLAN. (NAC uses a VLAN to determine if a device goes to guest or a corporate network)
VPN- communication tunnel that provides point-to-point transmission of both authentication and data traffic over an untrusted network.
Defense In Depth- using multiple types of access controls/ layers to help in organization and increase security
NAC- Network Access Control- concept of controlling access to an environment through strict adherence to and implementation of security policy. A way to prevent unwanted devices from connecting to a network. (ex: a hotel showing an AUP to users before allowing them to connect)
Which of the following tools can be used to grant remote users access to the internal IT environment?
ANSWER: VPN
The primary responsibility of the upper layer (host or application layer) in a network model is to transform data into a format that any system can understand
B. VLANs control whether devices connect to the corporate network or a guest network
How are VLANs used in Network Access Control (NAC) systems?
A. VLANs have no relevance to NAC systems
B. VLANs control whether devices connect to the corporate network or a guest network
C. VLANs determine the physical network switch to which NAC systems attach
D. NAC systems eliminate the need for VLANs
IOT Devices should be segmented because they are vulnerable to updates they use the TCP/IP protocols
The layer of the OSI model that corresponds to the Internet Layer in the TCP/IP protocol architecture is the Network Layer.
Embedded systems should be in VLAns to maximize security
What does the NAC device provide for access security and incident response?
Creation of access control policies
Guest user access
Network visibility
Exception for non-compliant devices
Zero Trust- Micro segmented networks with firewalls at every turn
STOPPED AT DOMAIN 5
ISC2 FLASHCARDS
2^n-2= number of host 2^(32-CIDR) -2 = HOSTS
ISO 27002: ISMS information security system standard
TCP AND UDP WORK ON THE OSI TRANSPORT LAYER:
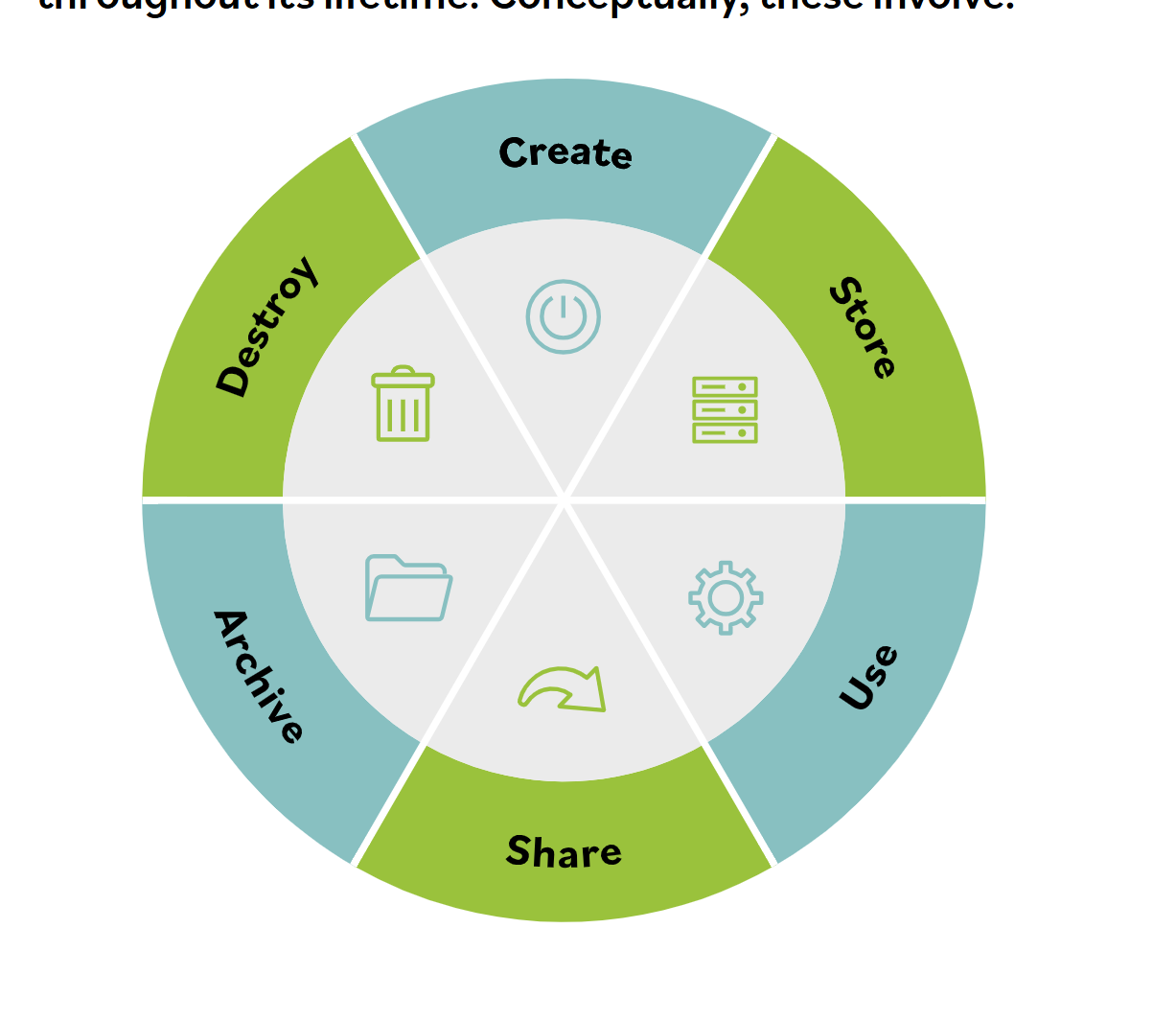
6 MAJOR LIFE CYCLES OF DATA PRODUCTS: Create, Store, Use, Share, Archive, Destroy
OSHA, HIPAA 10 YEARS, 30 YEARS OSHA.
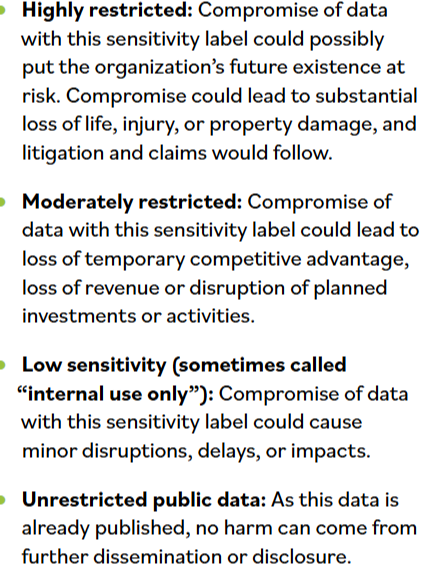
Classification: process of recognizing organizational impact if data/ info suffere security/confidentiality compromises.
Logs- records functions/requests very useful for audits.
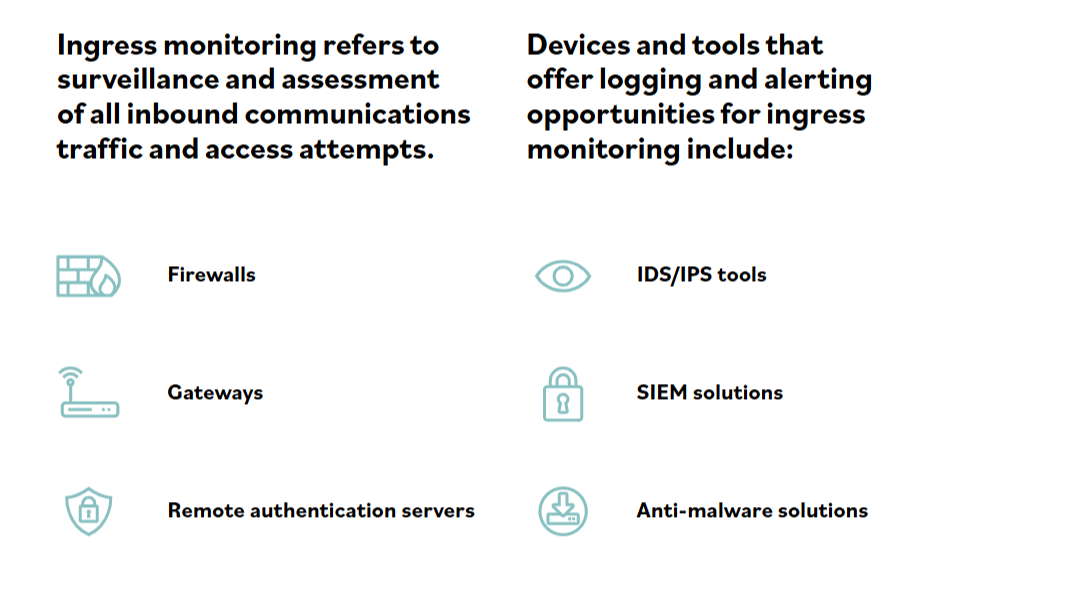
Ingress monitoring- refers to surveillance and assessment of all inbound communications traffic and access attempts.
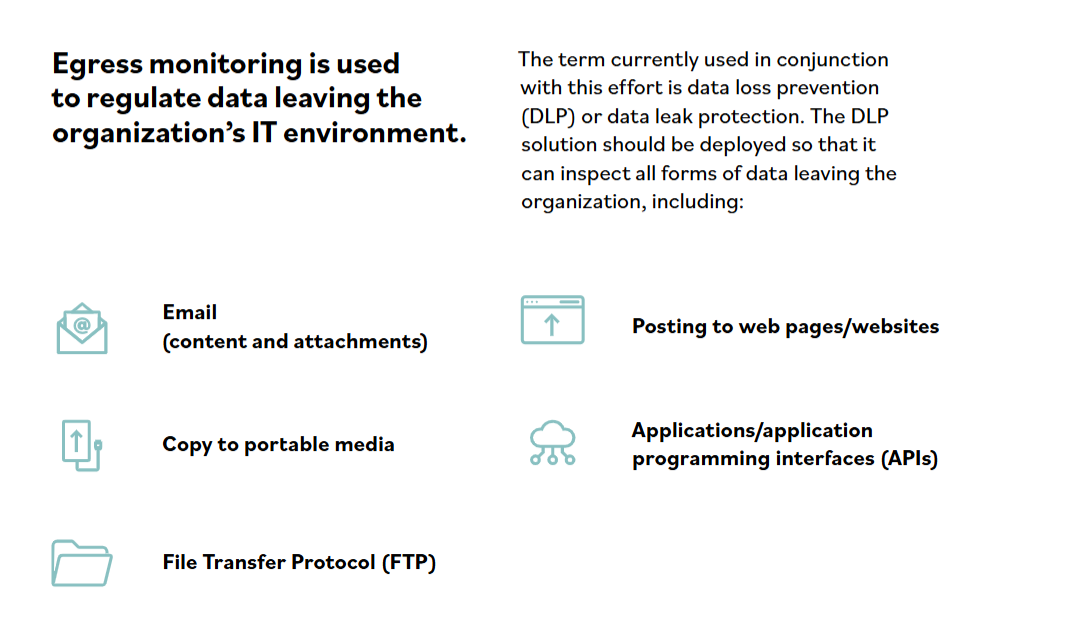
Egress monitoring- regulates data leaving the organization’s IT environment. (DLP - Data Loss Prevention)
Hash Functions solve integrity, and cryptography solves confidentiality.
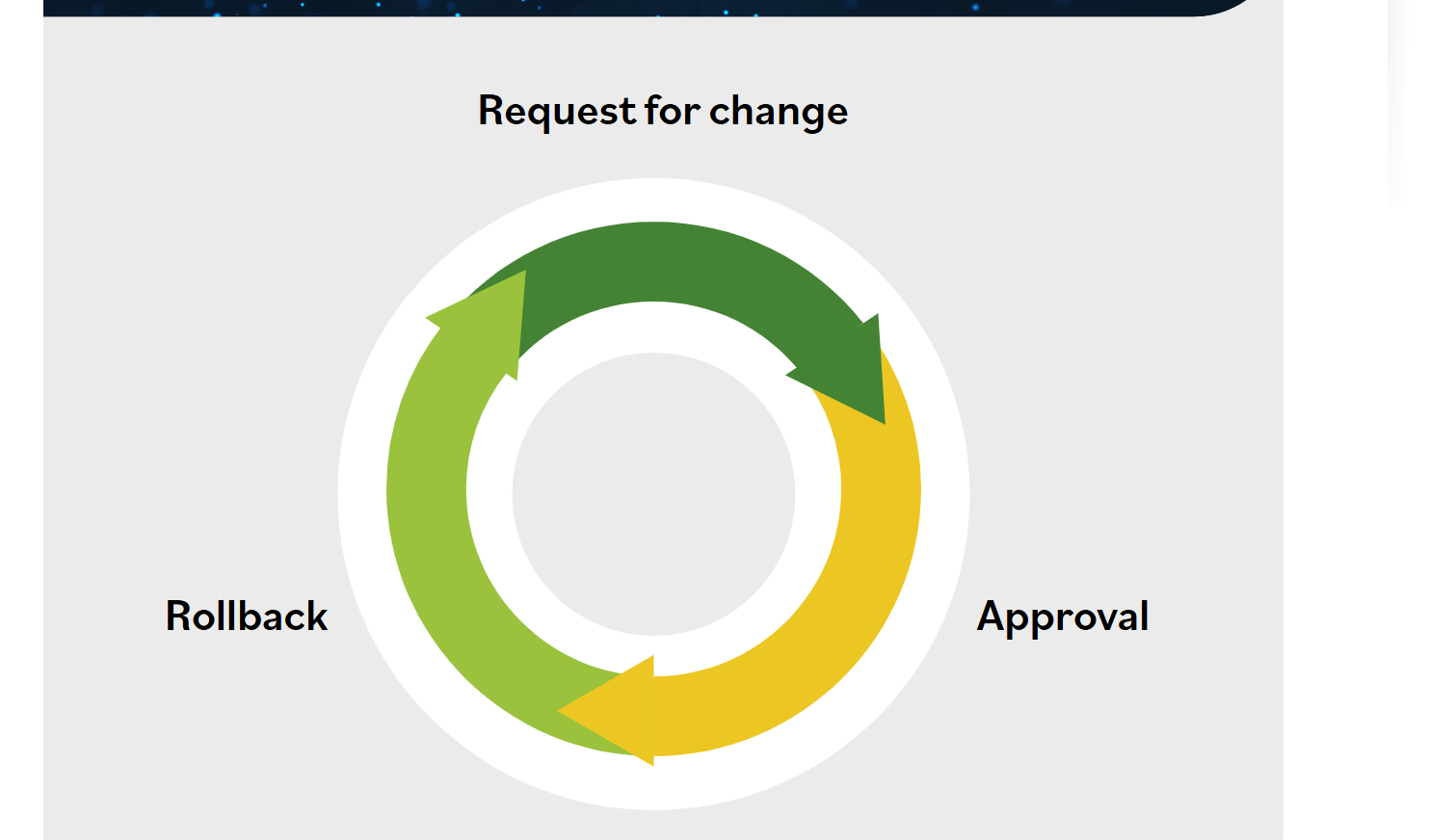
Configuration Management: Identification, Baseline, Change Control, and Verification Audit:
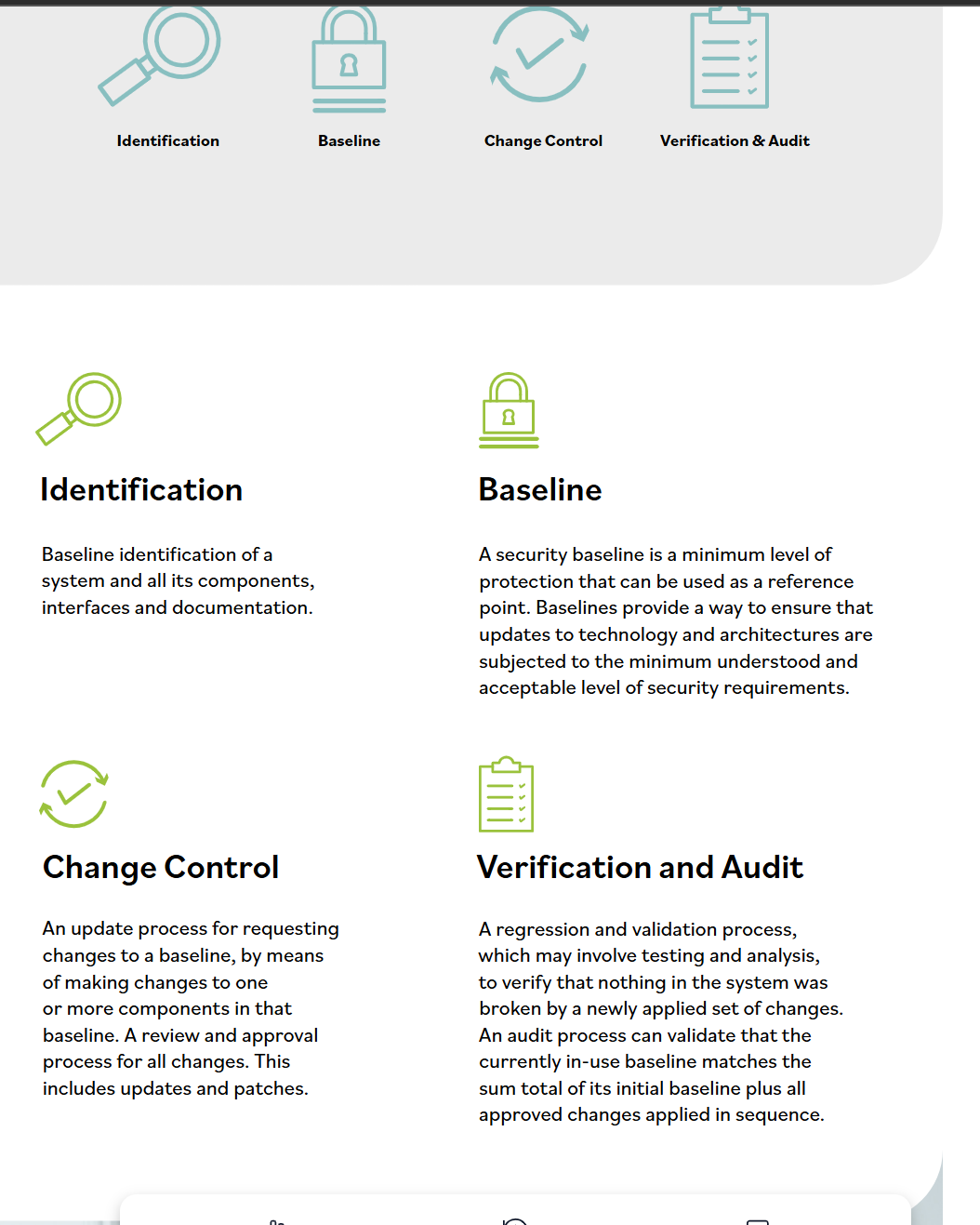
Change Management Components:
Asymmetric encryption uses one
key to encrypt and a different key
to decrypt the input plaintext. This
is in stark contrast to symmetric
encryption, which uses the same
key to encrypt and decrypt.
Think of it like a locked mailbox: anyone can drop a message in (using the public key), but only the person with the key to open it (the private key) can read the message.
quid pro quo=bribing, pretexting = impersonation, tailgating and vishing