Passwords
A secret string of characters that allows access to a computer system or service
\
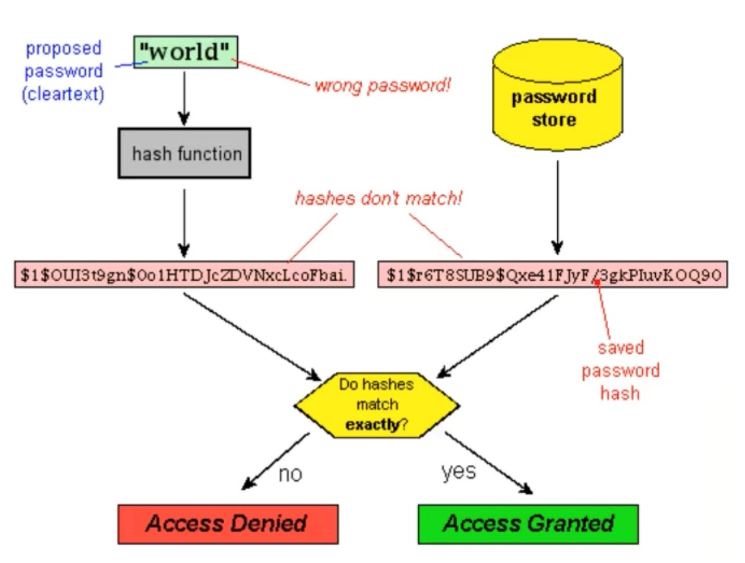
Challenge Response Protocol
- The user provides an identity
- A challenge is provided by the verifier (ex: They ask the user for a password, etc.)
- The verifier puts the answer to the challenge (ex: The proposed password given in plaintext) through a hash function and checks to see if the hashes match, and if so then access is granted
\n
- Cons * Dictionary Attacks * Rainbow Tables \n * One way of defending against these attacks is by using Salts * Another way is to nudge users to obey password policies
\n
Password usabilities
- nothing-to-carry
- physically effortless
- easy-to-learn
- easy-recover-from-loss
- etc.
\n
Password security properties
- Resilient-to-physical-observation
- Resilient-to-targeted-impersonation
- Resilient-to-theft
- Resilient-to-phishing
- Resilient-to-internal-observation
- Resilient-to-leaks-from-other-verifiers
- Unlinkable
- etc.
\
Password deployability
- Accessible
- Server compatible
- Browser compatible
- Mature
- etc.
\
Other types of passwords
- Graphical passwords * Three different approaches * Recognition based * Pure recall based * Cued recall based
\
\ \ \
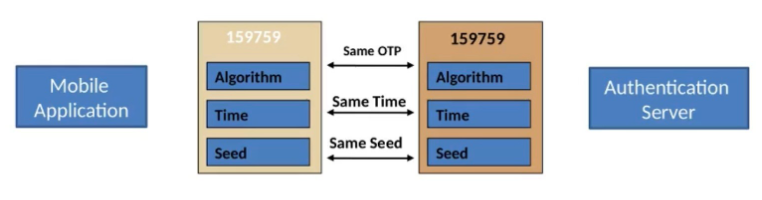
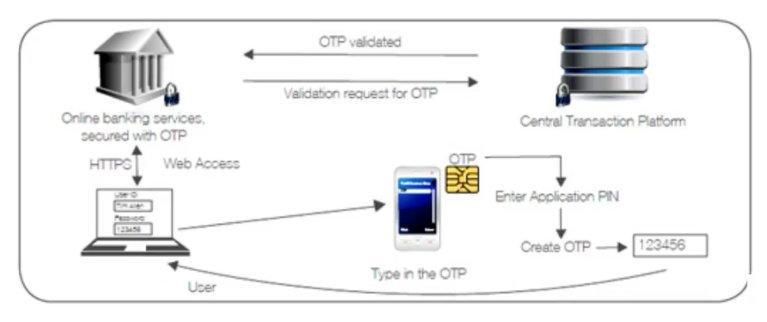
One-Time Passwords (OTP)
A password that is valid for only one login session or transaction, on a computer system or other digital device
\
Types of OTP
Software OTPs (An OTP generated by the company and sent to your mobile phone or PC)
- An event-based OTP (The moving factor is triggered by an event)
Hardware OTPs (An OTP generated by a security device/token)
- A time-based OTP (The moving factor is time)
\
OTP Generation
\ \ \
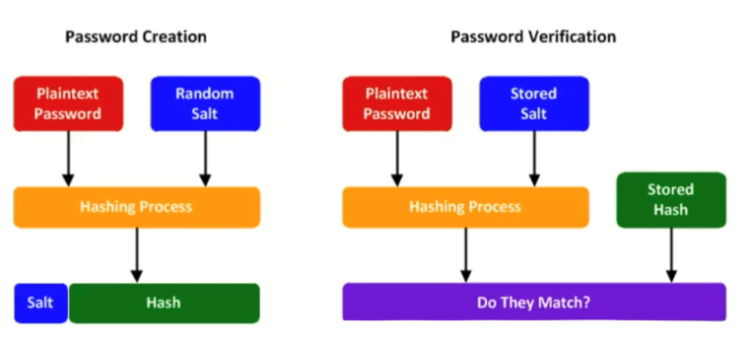
Salts
Adding a random value to a plaintext password before putting it through the hashing process
- Adding a random value makes it so that attacks that rely on pre-computation can no longer pre-compute the hashes in order to look through leaked databases to determine what password is what
- It also makes pre-computation impossible without brute forcing any and all possible random salts
- For password verification, the verifier will simply take the password provided by the user, add a Salt, put it through the hashing process, take the stored hash and see if they match
\
\ \