7 Virtual Private Networks (VPNs)
Virtual Private Networks
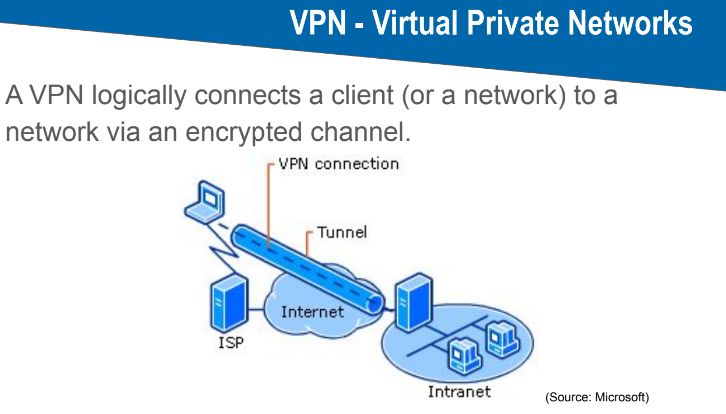
VPN Definition
VPN Properties
A device using a VPN obtains a different IP address, effectively being "logically" located in the remote network.
A VPN is responsible for routing packets between different networks.
Various protocols can be employed to establish the secure "tunnel". Common protocols include:
OpenVPN
Wireguard
IPSec
Numerous proprietary protocols
Security is guaranteed only between the tunnel endpoints (e.g., the VPN client and the VPN gateway). It's crucial to understand that traffic behind the endpoint, such as within an internal network, remains unencrypted.
Why Use a VPN
Control Access to a Company’s Internal Network: VPNs can restrict network access, ensuring that only authorized users can connect to a private network.
Circumvent Local Filters: VPNs enable users to bypass filters implemented by:
Organizations
Countries
Internet Providers
Circumvent Geo Blocking: VPNs can be used to access content that is restricted based on geographic location.
Secure Encryption and Mutual Authentication: VPNs provide a secure, encrypted connection and authenticate both the client and the server.
Protect Endpoint: The computer running the VPN client is protected by the VPN.
Access Internal Resources: VPNs allow access to resources that are only available from within the company network.