Digital Data and File Integrity Concepts
Understanding the importance of file integrity is crucial in the digital age, as it ensures that data remains unaltered during storage, transmission, and processing. Key aspects include checksum validation, encryption for secure data transfer, and regular audits to detect unauthorized changes. Implementing robust access controls and using data backup solutions are also vital strategies to maintain file integrity and safeguard against data loss.
Overview of File Types and Extensions
Students already understand different file types and their extensions, such as:
.csv: Commonly used for data interchange, particularly in applications like Microsoft Excel, where it represents spreadsheet data in a text format.
.doc: The primary file format for Microsoft Word documents, which can contain formatted text, images, tables, and more.
.png: This is a widely-used image format that supports lossless data compression and transparency, commonly used in web graphics.
These extensions are not just arbitrary designations; they play a crucial role in identifying file types and ensuring compatibility with appropriate software applications necessary for opening or editing these files. For instance, the operating system relies on file extensions to associate files with the respective applications, enabling users to manage documents and resources efficiently.
File Integrity and Hash Values
Students are introduced to hash values, which are used to verify that software or files are legitimate and unmodified. For instance, software companies may provide hash values for download to ensure the file’s integrity. Students learn the difference in content between file types by exploring the binary data using hex editors.
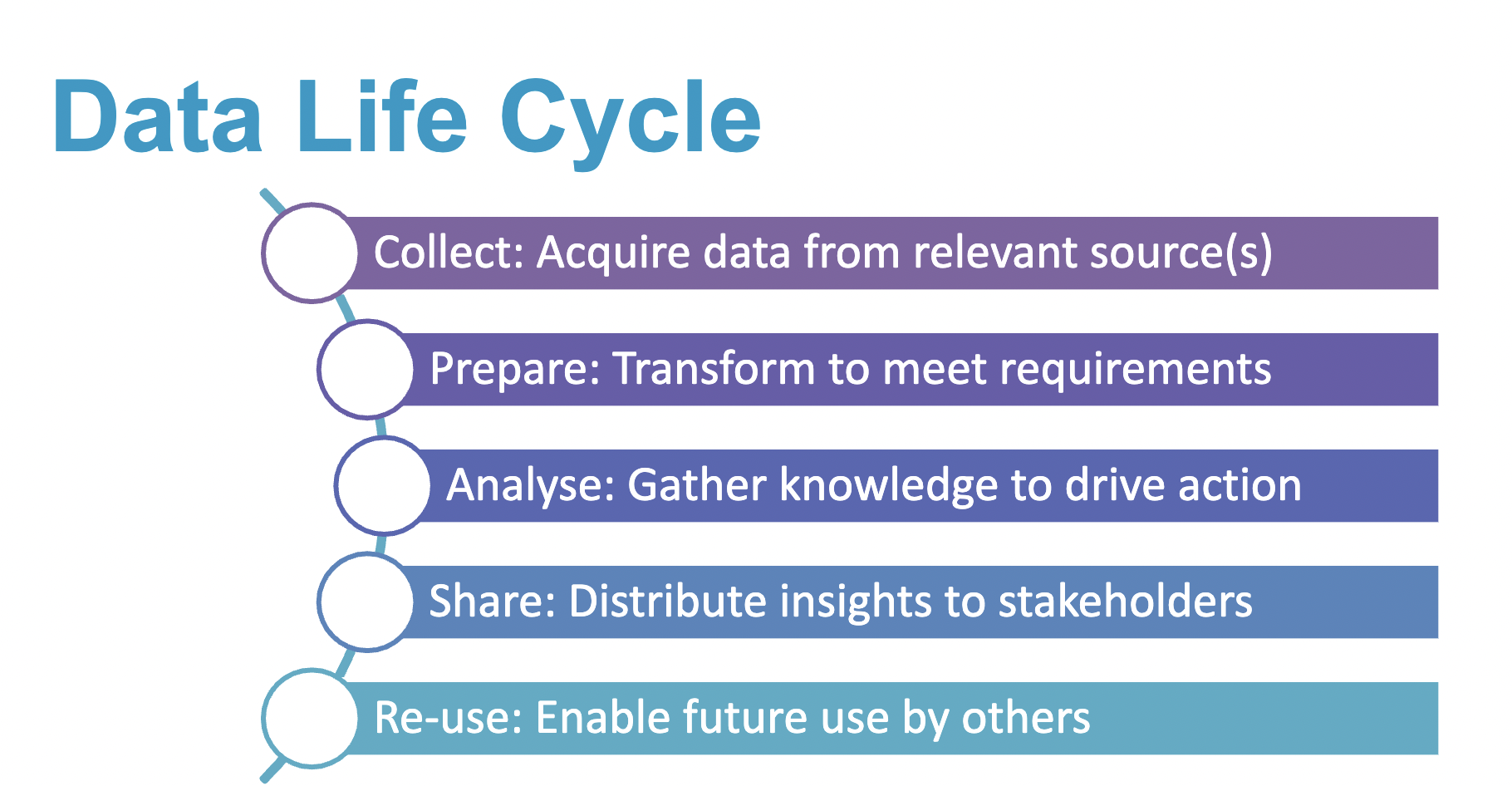
Data Life Cycle
A critical discussion surrounds the data life cycle consisting of: collecting, preparing, analyzing, sharing, and reusing data.
Collecting Data
Involves gathering raw data from various sources, such as customer transactions, surveys, IoT sensors, and social media.
Ensures a diverse dataset for comprehensive analysis.
Preparing Data
Involves cleaning to remove inconsistencies, filling in missing values, and transforming data into structured formats.
This phase is vital as it ensures quality and reliability, paving the way for accurate analyses.
Analyzing Data
Entails applying statistical and computational techniques to draw insights from the data.
Numerous methods can be employed, including descriptive statistics, predictive modeling, and machine learning algorithms.
Sharing Data
Communicates findings and insights to stakeholders through visualizations, reports, and dashboards.
It promotes collaboration and informed decision-making across departments or organizations.
Reusing Data
Involves utilizing previously analyzed data for new projects or analyses, maximizing data value.
Encourages continuous improvement and adaptation of business strategies based on past findings.
Examples provided illustrate the process where raw customer purchase data gets transformed into meaningful information leading to informed business decisions. This process emphasizes the importance of each phase, particularly the critical phase of preparation — cleaning and structuring data — before it can be analyzed for insights.
Exercises in File Exploration
The class engages in hands-on activities using software tools (e.g., Visual Studio Code and Hex Editor) to explore file formats, decode hexadecimal values, and verify data integrity. They conduct comparisons between .bmp and .png files to observe differences in their binary representation and compression methods. This practical application of theoretical concepts reinforces understanding.
Binary Systems and Digital Data
The explanation of binary systems as the foundational language of computers (0s and 1s) is simplified for comprehension. The distinction between bits and bytes is made, wherein 8 bits constitute a byte, facilitating more complex data storage across various formats (images, audio, text, etc.).
Encoding Systems and File Identification
The session highlights multiple encoding systems, including ASCII and UTF-8, and how they function. Students learn how files can be identified based on their headers and signatures. Emphasis is placed on file identification tools to determine the original format of files, particularly when extensions are misleading or absent.
Significance of File Hashing in Cybersecurity
The importance of data integrity concerning cybersecurity is discussed. Hashing is a method used to ensure that files remain unchanged during transmission or storage. The implications for businesses, such as the necessity of maintaining trustworthiness in data, are made clear.