Part-2-Introduction-in-Auditing-Computer-Based-Information-System-Copy
Audit ObjectiveObtain relevant and reliable audit evidence sufficient to draw reasonable conclusion therefrom”.
Difference between a computerized system and manual systemChanges in processing financial data
Changes in storage of financial data
Changes in communication of financial information
Changes in the organization structure and procedures
Effect of Computerization on Audit ProcessHowever, in a computerized accounting system. There are certain differences which must be considered, and which inevitably will lead for additional internal control.
Invisibility of processing which can invariably lead to a lack of audit trail
Potentially better internal control system. With less human intervention and automation, the system can be much more reliable than manual system.
Speed, accuracy, and consistency can be assured in a computer system. This is not the case with manual system.
There will often be a long-time lag between the conception and implementation of the system. It may take six months, a year, and even longer, in larger systems, before the accounting system is working adequately.
Centralization of processing. In manual systems the payroll, the sales, the purchases, are processed in separate department in isolation. In a computerized accounting system, processing is done in one location, the Central Processing Unit.
Characteristics of Computer Information SystemLack of visible transaction trails
In a manual system, it is normally possible to follow a transaction through the system by examining the source documents, entity’s records, and financial reports.
In a CIS environment, data can be entered directly into the computer system without supporting documents.
Furthermore, records and files may not be printed and can not be read without using the computer.
The absence of these visible documents supporting the processing of transactions makes the examination of evidence more difficult.
Consistency of performance
CIS performs functions exactly as programmed.
If the computer programed to perform a specific data processing task, it will never get tired of performing the assigned task in the same manner.
Because of this capability of the computer to process transactions uniformly, clerical errors that are normally associated with manual processing are eliminated.
On the other hand, an incorrect program could be very devastating because it will result to consistently erroneous data processing.
Ease of access to data and computer program
In a CIS environment, data and computer programs may be accessed and altered by unauthorized person leaving no visible evidence.
It is important, therefore, that appropriate controls are incorporated to the system to limit the access to data files and programs only to authorized personnel.
Concentration of duties
Proper segregation of duties is an essential characteristics of a sound internal control system.
However, because of the ability of the computer to process data efficiently, there are functions that are normally segregated in manual processing that are combined in a CIS environment.
As a particular example, in manual processing the function of recording cash disbursements is incompatible with the responsibility for reconciling disbursements.
Since one of these functions to one employee would enable that employee to commit and conceal errors or irregularities.
A properly programmed computer, on the other hand, has no tendency or motivation to commit irregularities or conceal its errors.
Hence, what appears to be an incompatible combination of functions may be combined in a CIS environment without weakening the internal control provided appropriate compensating controls are put in place.
Systems generated transactions
Certain transactions may be initiated by the CIS itself without the need for an input document.
For example, interest may be calculated and charged automatically to customers’ account balances on the basis of pre- authorized terms contained in a computer program.
Vulnerability of data and program storage data
In a manual system, records are written in ink on substantial paper.
The only way to lose information is to lose or to destroy the physical records.
The situation is completely different in a CIS environment.
The information on the computer can be easily changed, leaving no trace of the original content.
This change could happen inadvertently, and huge amount of information can be quickly lost.
The Benefits for Auditor of Using Computer SoftwareTime may be saved by eliminating manual casting and other routine calculation.
Calculations and comparisons are performed more accurately.
Audit sampling may be facilitated.
Potential weaknesses in a client’s internal control system may be identified more readily.
Potential of Material ErrorsData entry/processing – errors can happen during data entry as a result from negligence or human error.
Unauthorized Access – data and information can be altered without physical evidence by unauthorized person if he knows the password.
Lost of data – theft and accidental erasure can cause loss of invaluable data and information.
Internal Control in Electronic Data Processing (EDP) Environment
- The difference between computerized and manual accounting
system mean there is a requirement for additional internal
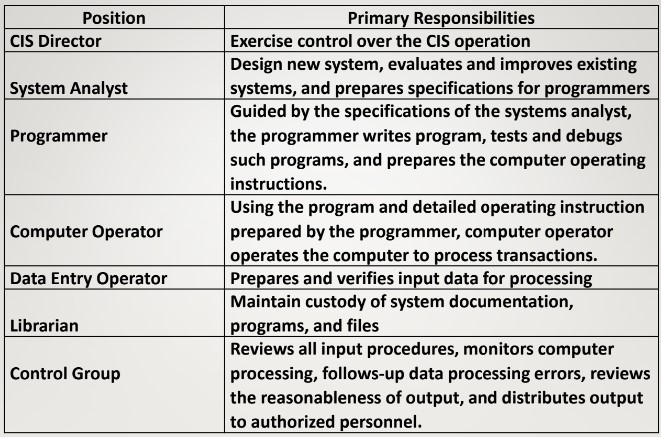
controls, and they are:General Controls ( Administration and System Development)These are controls which cover the environment in which the application is developed, maintained and operated, and which are therefore applicable to all parts of the EDP.
OBJECTIVE: to ensure proper development and implementation of applications and the integrity of program and data files and of computer operation.
Classified into 5 categories:
Organizational Controls
here should be written plan of organization, with clear assignment of authority and responsibility.
In CIS environment, the plan of organization for an entity’s computer system should include segregation between the user and CIS Department, and segregation of duties within the CIS Department.
a. Segregation between the CIS Department and User Departments.
CIS Department must be independent of all departments within the entity that provide input data or that use output generated by the CIS.
The function of CIS Department is to process transactions.
No transaction will be processed unless it is initiated by the user department.
All changes in computer files must be initiated and authorized by the user department.
b. Segregation of duties within the CIS Department
Functions within the CIS Department should be properly segregated for good organizational controls.
The entity’s organizational structure should provide for definite lines of authority and responsibility within the CIS department.
Systems Development and Documentation Controls
Software developments as well as changes thereof must be approved by the appropriate level of management and the user department.
To ensure that computer programs are functioning as designed, the program must be tested and modifies, if needed, by the user and CIS Department.
Moreover, adequate systems documentation must be made in order to facilitate the use of the program as well as changes that may be introduced later into the system.
Security and Access Controls
Every computer system should have adequate security controls to protect equipment, files and programs.
Access to the computers should be limited only to operators and other authorized employees.
Additionally, appropriate controls such as the use of passwords must be adopted in order to limit access to data files and programs only to authorized personnel.
Operations and Data Recovery Controls
CIS have vulnerability of files and programs.
Computer files can easily lose, and the lost of these files can be disastrous to an entity.
The survival of an entity affected by such disaster depends on its ability to recover the files on a timely basis.
A data recovery control provides for the maintenance of back-up files and off-site storage procedures
Data Recovery Controls
Computer files should be copied daily to tape or disks and secured off-site.
In the event of disruption, reconstruction of files is achieved by updating the most recent back-up with subsequent transaction data.
When magnetic tapes are used, a common practice in file retention called Grand-father, father, son requires an entity to keep the two most recent generation of master files and transaction files in order to permit reconstruction of master files if needed
Monitoring Controls
designed to ensure that CIS controls are working effectively as planned.
These include periodic evaluation of the adequacy and effectiveness of the overall CIS operations conducted by persons within or outside the entity.
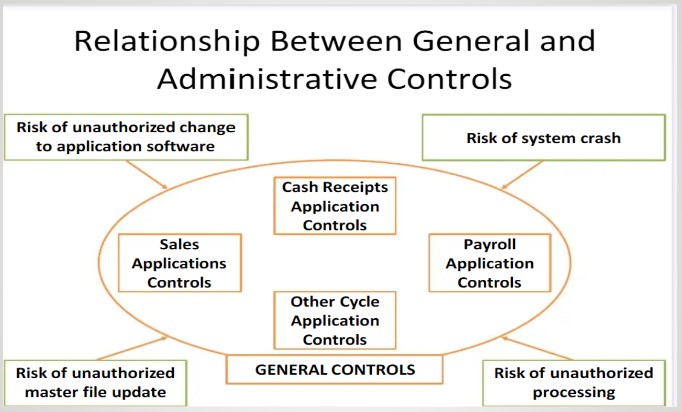
Application controlsThese are controls which seek to ensure the accuracy and completeness of the input processing, and the validity of the resulting accounting entries.
Apply to specific use of the computer systems applications.
These are designed to provide reasonable assurance that all transactions are authorized, and that they are processed completely, accurately and on a timely basis.
Classified into 3 categories:
Controls over input
are designed to provide reasonable assurance that the data submitted for processing are complete, properly authorized and accurately translated into machine readable form.
Many errors in a computer system are caused by inaccurate or incomplete data entry.
EXAMPLES:
A. Key verification -This requires data to be entered twice, usually by different operators, to provide assurance that there are no key entry errors committed.
B. Field check - This ensures that the input data agree with the required field format.
C. Validity check - Information entered are compared with valid information in the master file to determine the authenticity of thr input. Example: the employees’master file may contain 2 valid codes to indicate the employee’s gender “1” for male and “2” for female. A code of ‘3” is considered invalid and will be rejected by the computer.
D. Self-checking digit -This is a mathematically calculated digit which is usually added to a document number to detect common transpositional errors in data submitted for processing.
E. Limit check -is designed to ensure that data submitted for processing do not exceed a pre-determined limit or a reasonable amount.
F. Control tools
These are totals computed based on the data submitted for processing.
Control totals ensure the completeness of data before and after they are processed.
These controls include financial totals, hash totals and record counts.
Control over processing
are designed to provide reasonable assurance that input data are processed accurately, and that data are not lost. Added, excluded, duplicated or improperly changed.
Almost all the inputs controls that were mentioned earlier are also part of the processing controls because such controls are usually incorporated in the client’s computer program to detect errors in processing of transaction.
Control over output
are designed to provide reasonable assurance that the results of processing are complete, accurate, and that these outputs are distributed only to authorized personnel.
A person who knows what an output should look like must review the CIS output for reasonableness.
Control totals are compared with those computed prior to processing to ensure completeness of information.
Finally, CIS outputs must be restricted only to authorized employees who will be using such outputs.