Common Encryption Uses
You encrypt and decrypt data every day of your life. It could be when connecting to banking or healthcare websites or when you connect to your corporate network via a virtual private network (VPN) tunnel, as you will learn more about in this lesson. Encryption comes in a variety of forms and is used to protect data flowing through a network or when the data is stored on a disk. Data moving through a network is known as data in transit, while data that resides on a disk is known as data at rest. When the data is both encrypted in transit and at rest, you have end-to-end encryption. End-to-end encryption means that the data is never stored or transmitted in the clear.
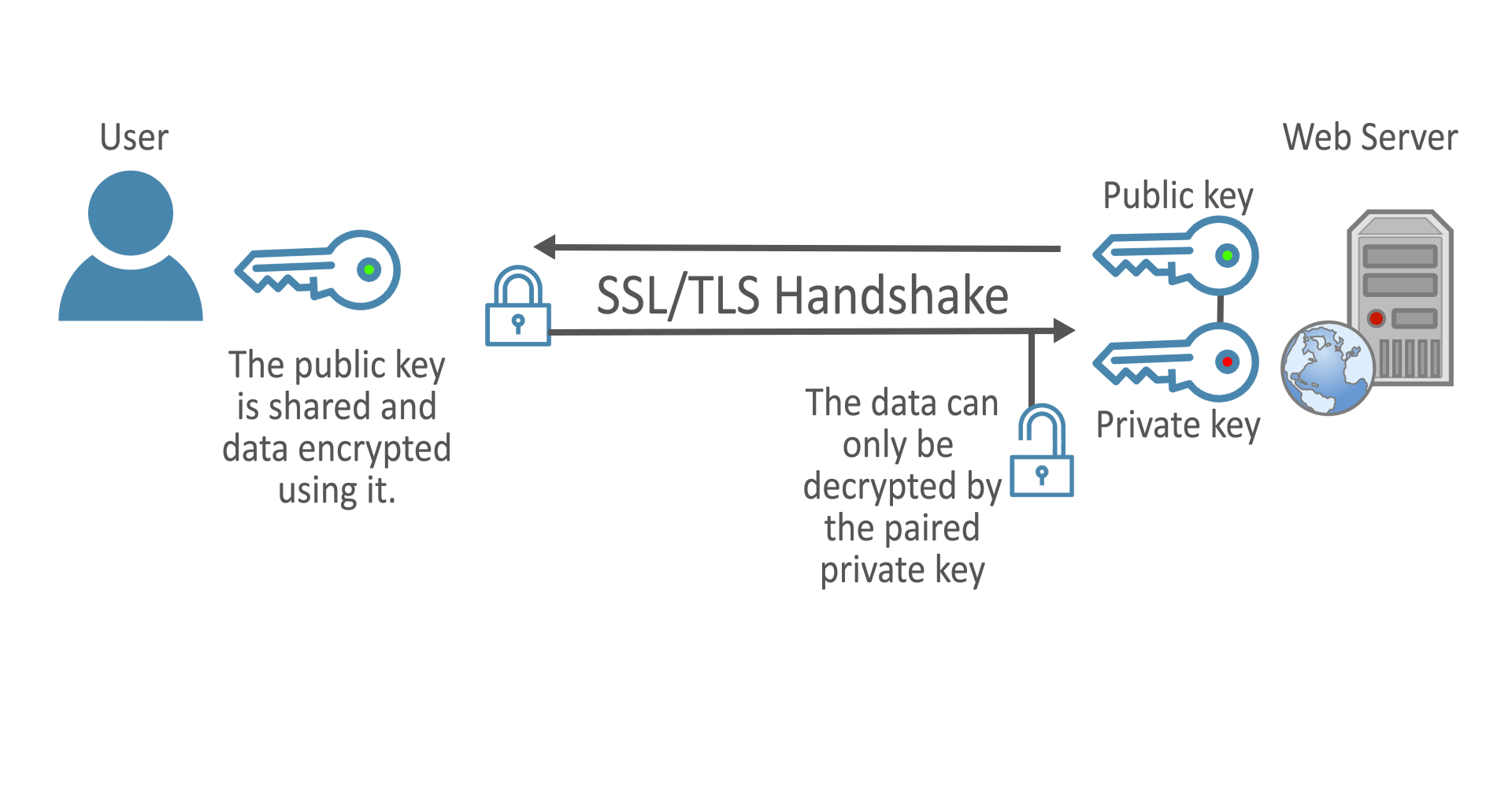
SSL/TLS Encryption
Diagram. How SSL/TLS encryption works.
Secure Sockets Layer (SSL) and Transport Layer Security (TLS) are the most common forms of encryption found on the internet today. Though SSL was deprecated in 2015, TLS provides similar functionality with more robust security. TLS creates a secure channel over the internet between a client computer and a server by exchanging a public key in the form of a certificate. The certificate is issued by a registered and well-known certificate authority (CA), such as Verisign. The certificate has a public key that is stored on the webserver and presented to the public whenever a user connects to the website. The private key is also stored on the webserver but is kept secret and protected.
When a client computer (the web browser) contacts the webserver, the client initiates an encryption handshake that establishes a symmetric key that will be used to encrypt their traffic. The key exchange starts with the client computer encrypting a token with the webserver’s public key. This ensures that only a computer holding the private key, the webserver, can decrypt the token. The webserver then decrypts the token using its private key, and then uses the token as a private key in the symmetric key cipher with the client, thereby ensuring both sides of the communication and the key exchange remain encrypted.
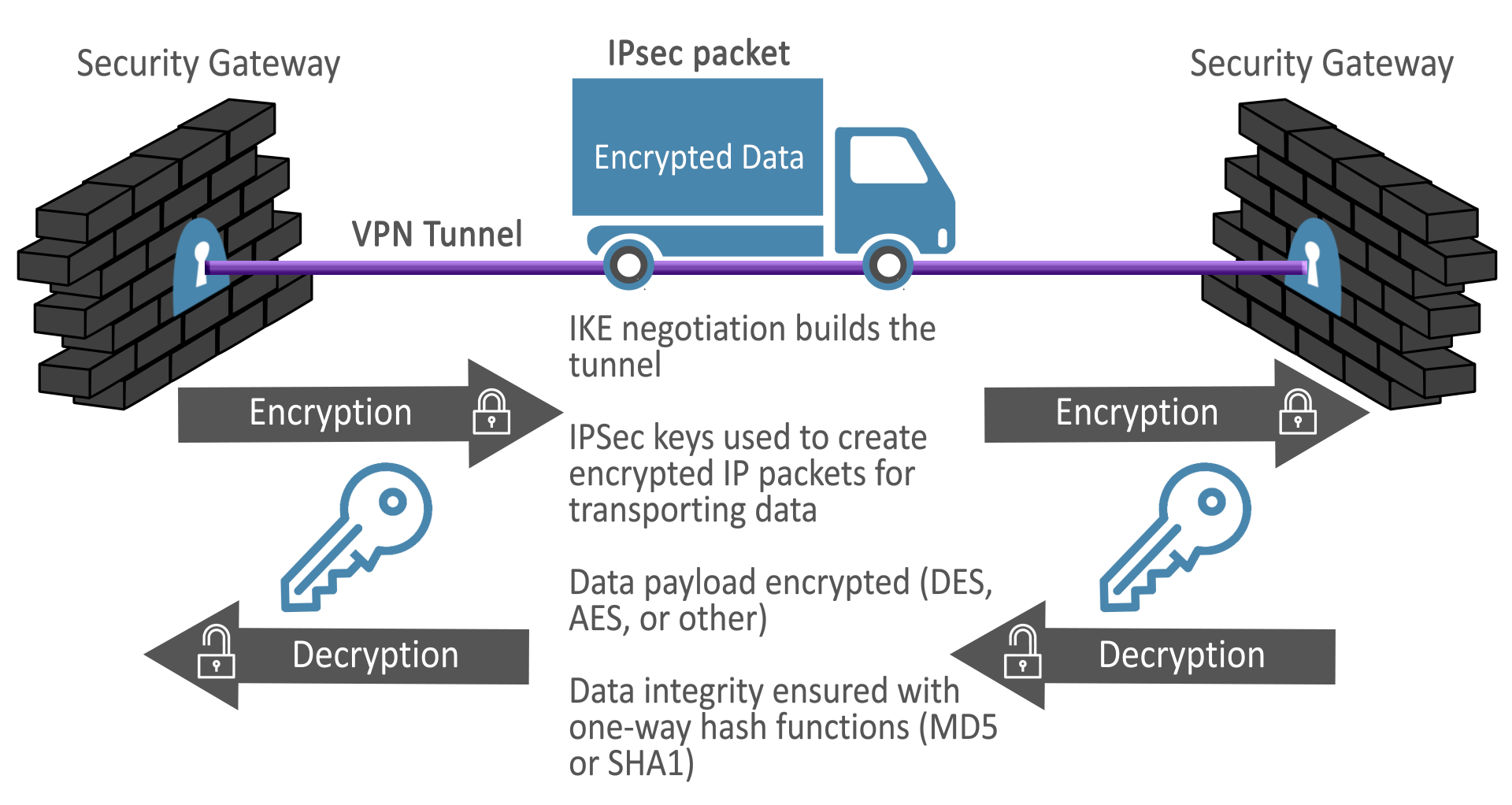
IPSec Encryption
Diagram. How IPSec encryption works.
Diagram Description
Internet protocol security (IPsec) provides an authentication and encryption solution that secures IP network traffic at Layer 3 of the OSI model. This is in contrast to the TLS protocol discussed above, which operates at Layer 6. TLS also differs in that it provides a PKI encryption method commonly used to encrypt web pages or data sent between one client and one server. IPsec, on the other hand, is commonly used to create virtual private network (VPN) tunnels across the internet or other untrusted networks to allow many computers to communicate with each other.
Though it is possible to have a client-to-server IPsec VPN tunnel, they are more often found in site-to-site configurations between devices, such as firewalls or routers. By terminating the encryption on a network device instead of a client computer or server, the computers are freed from the burden of encrypting and decrypting their traffic when communicating across the tunnel.
IPsec traffic is encapsulated and authenticated, which allows the devices to create an encrypted tunnel that traffic may pass through. This encapsulation hides the fact that the packets are flowing across an untrusted network, such as the internet, and gives the client computers the illusion that they are directly connected to one another or at least within the same network.
IPsec is composed of the Authentication Header (AH) protocol, which provides data integrity for the connection, the encapsulating security payload (ESP), which provides encryption for the connection, and the security associations (SA), which define the algorithms to be used and the key exchange method. IPsec is often used with internet key exchange (IKE) and IKEv2, though it is also possible to use IPsec with symmetric keys (more often called pre-shared keys because both devices must be configured to use the same key during the VPN negotiation process).
Common Data-at-Risk Algorithms
When data is stored in a permanent or semi-permanent state, the data is said to be at rest. Data at rest should be treated with the same level of care as data in transit because servers and their components can be physically stolen or compromised in such a way that the data is left in the clear and exposed to attackers.
Advanced Encryption Standard
You may have guessed from the earlier lessons that for bulk encryption of data, the preferred choice of ciphers would be a symmetric key algorithm. Currently, the most secure algorithm for storing and encrypting data at rest is the Advanced Encryption Standard (AES), a symmetric key cipher that makes use of different key and block sizes and creates a near-impenetrable encryption. AES modifies the plaintext input by performing a series of transformations on the data to create ciphertext. Depending on the key length, as many as 14 transformations can be made against a given block of data, making it exceptionally difficult, if not impossible, to reverse the encryption without the key or the aid of quantum computers.
\n