Domain 2 Risk Treatment: Risk Response Options - Risk Management Term Summary
Risk Management Terminology
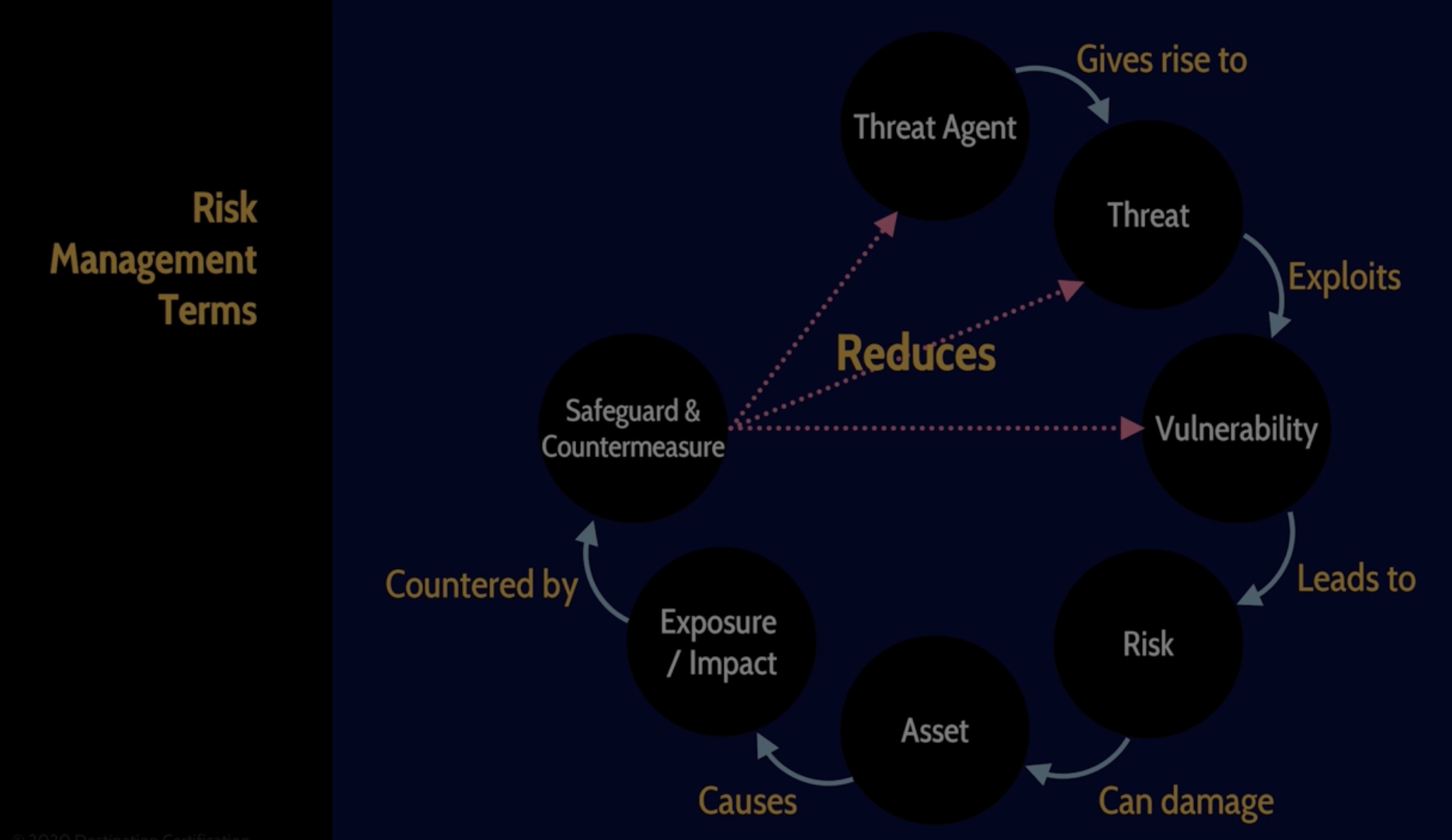
Threat Agent
Definition: A threat agent is an entity that has the capability to cause a threat. Examples include:
An attacker
A natural event such as a hurricane
A disaster like a fire
Threat
Definition: A threat is a potential danger that arises from a threat agent.
Connection to Threat Agent: Threats are a direct consequence of threat agents.
Vulnerability
Definition: A vulnerability is a weakness or flaw in a system that can be exploited by threats.
Connection to Threats: Threats exploit vulnerabilities, leading to increased risk.
Risk
Definition: Risk refers to the potential for damage to occur as a result of threats exploiting vulnerabilities.
Connection to Assets: Risks represent the possible loss or harm to assets.
Effect on Organization: Can lead to impacts that significantly affect an organization's functioning.
Asset
Definition: An asset is anything of value to an organization.
Importance: Assets are the targets of threats and vulnerabilities, making them central to risk management.
Impact / Exposure
Definitions:
Impact: The effect of risk occurring, which can manifest in several ways.
Exposure: The condition or state of being exposed to risk.
Examples of Impacts/Exposures:
Loss of reputation
Monetary loss
Loss of confidentiality (e.g., data breaches)
Loss of integrity (e.g., alteration of data)
Safeguards
Definition: Safeguards are proactive measures put in place to prevent risks from occurring.
Examples of Safeguards:
Directive Controls: Policies and procedures designed to guide and manage risk.
Deterrent Controls: Measures that aim to discourage the occurrence of risks.
Preventative Controls: Actions taken to reduce the likelihood of risks occurring.
Countermeasures
Definition: Countermeasures are reactive measures implemented to address risks that have already occurred.
Examples of Countermeasures:
Detective Controls: Identify and detect risks as they occur.
Corrective Controls: Fix or mitigate the consequences of risks that have happened.
Recovery Controls: Help restore systems and operations after a risk event.
Compensating Controls: Alternative measures to achieve security objectives when normal controls are not feasible.
Overall Risk Management Strategy
Goal: The ultimate aim of implementing safeguards and countermeasures is to reduce the likelihood and impact of threat agents and their associated threats, as well as to eliminate vulnerabilities wherever possible.
Summary of Risk Management Terminology: Understanding these terms and their interrelations is crucial for effective risk management.