Symmetric Cryptography
Both encryption and decryption operations use the same key
Secret-key systems have been around for many hundreds of years
Types
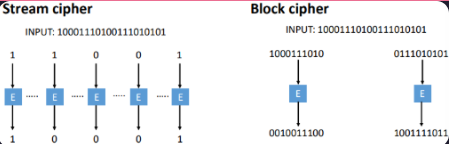
Stream Ciphers
A method that encrypts data one bit or byte at a time by combining it with a pseudorandom keystream, typically using the XOR operation
Require sender and receiver synchronicity
Method
Take as input a (short) key
Key is often combined with an initialisation vector (IV)
Key is converted into a continuous keystream
Working with one bit at a time, the plaintext is mixed with the keystream
Advantages
No error propagation
On-the-fly-encryption - good choice for real-time services
Fast and easy to implement, especially in hardware
How it Works
Keystream Generation - a small secret key and Initialisation Vector (IV) feed a PseudoRandom Number Generator (PRNG) to produce a long, seemingly random keystream
Encryption - each bit/byte of the plaintext is XORed with the corresponding bit/byte of the keystream to produce ciphertext
Decryption - the same keystream is XORed with the ciphertext to recover the plaintext
Examples
A5/1
Used in GSM (Global System for Mobile Communications)
No longer considered secure
Is used to provide over-the-air communication privacy in the GSM cellular telephone standard
Works by generating a 114-bit keystream for each conversation frame using three Linear Feedback Shift Registers (LFSRs)—lengths 19, 22, and 23 bits— which is then XORed with the plaintext data
RC4
Used in SSL/TLS
Owned by RSA, designed by Ron Rivest in 1987
Became public in 1994
Simple and effective design
Variable key size (typical 40 to 256 bits)
Widely used (web SSL/TLS, wireless WEP)
Simple workflow:The user inputs a plaintext and a secret key
The encryption engine then generates the keystream by using algorithms -KSA and PRGA
The keystream is now XOR with the plaintext, which is done byte by byte to produce the encrypted text
Block Ciphers
A method to transform fixed-length blocks of data (e.g., 128 bits) into ciphertext using a secret key
Method
Take as input a key and a block of plaintext and outputs a block of ciphertext
A good block cipher should be designed to provide confusion and diffusion
Confusion hides the relationship between the plaintext and ciphertext
Diffusion spreads the statistics of the plaintext through the ciphertext
Usually obtain protection from chosen plaintext attacks if the block cipher behaves like a pseudorandom permutation
Block length should be chosen to ensure a balance of efficiency and security
Examples
Data Encryption Standard (DES)/Triple DES (3DES)
Widely used through the 1980s and 1990s
3DES is still in use, but not recommended for new applications
International Data Encryption Algorithm (IDEA)
Camellia
Advanced Encryption Standard (AES)
Standardised by National Institute of Standards and Technology (NIST)
Widely adopted and supported
Modes of Operation
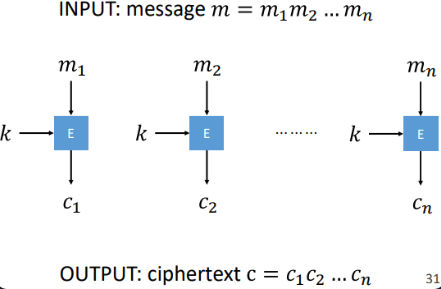
Electronic Code Books (ECB)
It is the simplest, most basic block cipher mode of operation where each plaintext block is encrypted independently using the same key, resulting in identical ciphertext blocks for identical plaintext
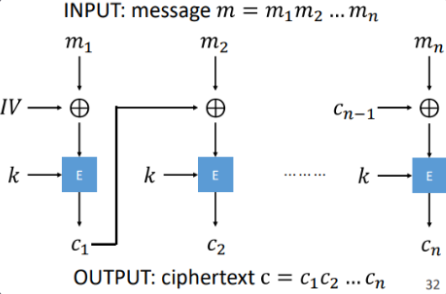
Counter Block Chaining (CBC)
A mode by XORing each plaintext block with the previous ciphertext block before encryption, breaking up patterns
It requires an initialisation vector (IV) for the first block to ensure uniqueness
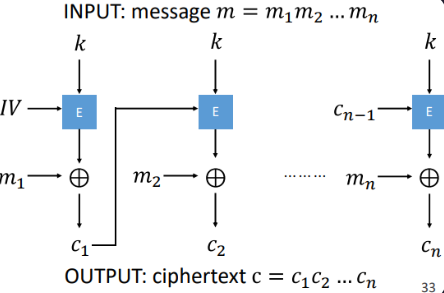
Cipher Feedback (CFB)
It works by encrypting the previous ciphertext block (or IV for the first block) using the block cipher algorithm, and XORing the result with the current plaintext to produce the ciphertext
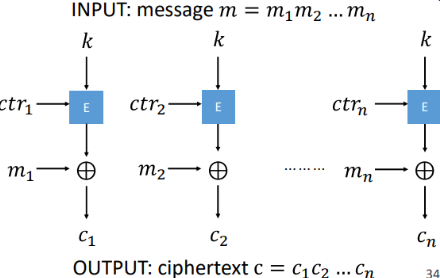
Counter (CTR)
It works by encrypting successive values of a counter to generate a keystream, which is then XORed with plaintext to produce ciphertext
Padding
Many block ciphers require the message to be a multiple of the block size
Data that does not fit the exact block size must be padded, which can add overhead
Padding extends a plaintext message to a multiple of the block size
Examples:
Bit padding
Zero padding