1.4 - CompTIA Security+
1.4a - Public Key Infrastructure: Professor Messer
Public key infrastructure (PKI)
Public key infrastructure (PKI): Refers to the management of digital certificates and the binding of public keys to people or devices.
Public key
Private key
Key escrow
Key escrow: Refers to someone else holding the decryption keys - private keys (for asymmetric cryptography) are held in the hands of a 3rd-party, although this may be in your organization.
Encryption
Level
Full-disk
Full-disk encryption: Encryption that protects an entire hard disk/storage drive, e.g., BitLocker (Windows), FileVault (macOS).
Partition/Volume
Partition/volume encryption: Encryption of sections of a storage drive - also achievable via BitLocker and FileVault.
File
File encryption: Encryption of individual files on a storage device, ensuring that only authorized users can access the contents. Examples include Encrypting File System (EFS) on Windows.
Database
Database encryption: Encryption of data stored in a database. Involves transparent encryption, where all database information is encrypted with a symmetric key.
Record
Record-level encryption: Encryption of individual columns within a database - separate symmetric keys are used for each column.
Transport/communication
Transport encryption: Encryption of data in transit or traversing a network (e.g., HTTPS or using a VPN).
Asymmetric
Asymmetric: A cryptographic method that utilizes a pair of keys, a public key that anyone can use to encrypt data, and a private key for decrypting data, ensuring that only the intended recipient can decrypt the message.
Symmetric
Symmetric encryption: A cryptographic method that uses the same key for both encryption and decryption. The message is encrypted/decrypted until it comes into contact with the key. Very fast compared to asymmetric encryption.
Key exchange
Key exchange: Refers to the logistical challenge of sharing the secret key between parties in a secure manner, ensuring that only authorized users can access the key and thus the encrypted data.
Out-of-band key exchange: Non-Internet transfer of encryption keys (e.g., telephone, postal services, or physical delivery methods).
In-band key exchange: Internet-based key exchange - the key is protected with symmetric encryption.
Algorithms
Encryption algorithms: Formulae used to encrypt/decrypt data that can vary in complexity, security, and performance.
Key length
Key length: Refers to the size of the key used in an encryption algorithm, which directly impacts the strength of the encryption; longer keys generally provide higher security but may result in slower performance.
128-bit keys are common for symmetric encryption, and 3,072-bit keys are common for asymmetric encryption
Tools
Trusted Platform Module (TPM)
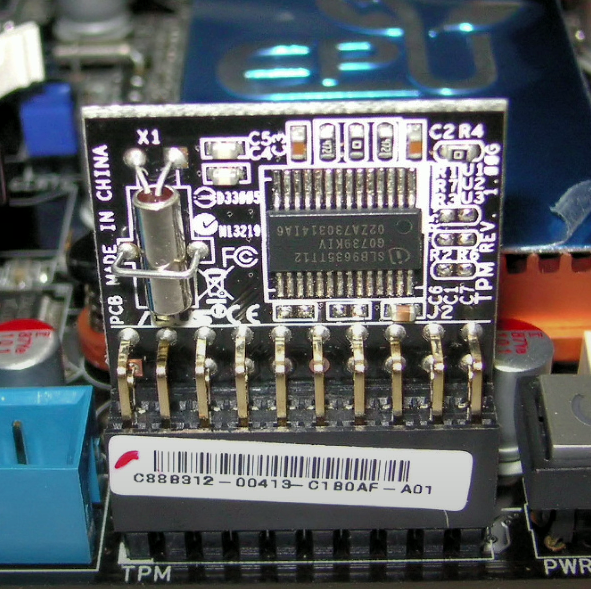
Trusted Platform Module (TPM): A hardware that performs cryptographic functions. Contains a cryptographic processor, persistent memory (unique keys burned in), FDE key storage, and password protection.
Hardware security module (HSM)

Hardware security module (HSM): High-end cryptographic hardware designed to manage thousands of cryptographic keys for hardware devices. Includes key backups and cryptographic accelerators.
Key management system
Key management system: Software used to provide centralized key management and protect cryptographic keys throughout their lifecycle, ensuring secure generation, storage, distribution, and destruction.
Secure enclave
Secure enclave: A secure area within a hardware component that provides a high level of security for sensitive information by isolating it from the rest of the system, ensuring that data can be processed, stored, and accessed in a trusted environment.
Obfuscation
Obfuscation: A technique used to deliberately alter or obscure the content of code or data to prevent unauthorized access or understanding.
Steganography
Steganography: A security technique used to conceal a message within another message or physical object. This includes hiding information within images (most common), TCP packets, or audio samples.
Tokenization
Tokenization: Replacing sensitive data with a non-sensitive placeholder - if an attacker intercepts the placeholder, it cannot be used to retrieve the original information that it represents. Commonly used for credit card payments.
Data masking

Data masking: Hiding most of the original data while retaining some data for validation purposes (e.g., hiding a credit/debit card and only showing the last four numbers).
Hashing
Hashing: Production of a fixed-length string of bits from an input plaintext - the input plaintext can be any length, and the hash produced is irreversible.
Salting
Salting: A security countermeasure that mitigates the impact of precomputed hash table attacks by adding a random value to the password before hashing it.
Digital signatures
Digital signatures: A method for verifying the authenticity and integrity of a message using a hash and encryption with the sender's private key.
Key stretching
Key stretching: Performing multiple cryptographic processes using a weak key to make the output more secure.
Blockchain
Blockchain: A distributed ledger technology that securely records transactions across multiple computers, ensuring that the data cannot be altered retroactively without the consensus of the network.
Many practical applications, including payment processing, digital identification, supply chain monitoring, and digital voting.
Open public ledger
Open public ledger: A decentralized database that stores records of transactions in a computer network, open-access (anyone can join the network), and decentralized (no public entity controls the network).
Function of blockchain: Requested transactions are verified by nodes (devices) on a network, adding transactions to blocks, then calculating hashes to verify blocks. If transactions/blocks are tampered with, the block is rejected by the blockchain.
Certificates
Digital certificates: Cryptographic information that binds a public key with a digital signature - used for verification and for trust (with digital signatures).
Certificate authorities
Certificate authorities: Organizations that issue and manage digital certificates - they verify the identity of individuals and organizations.
Certificate revocation lists
Certificate revocation list: A list of revoked/terminated digital certificates, managed by a certificate authority.
Multi-step process (CRL checking): Browser connects to a third-party website. The third-party website provides your browser with its certificate. The browser then looks through the cert to find the CRL distribution points and then follows one of those URIs to download the CRL list.
Online Certificate Status Protocol (OSCP)
Online Certificate Status Protocol (OSCP): A protocol used for obtaining the revocation status of a digital certificate in real-time via the SSL handshake.
Self-signed
Self-signed certificate: A digital certificate that is signed by the entity it certifies, rather than a trusted certificate authority, often used for testing and internal purposes but not recommended for production environments.
Third-party
Third-party certificates: Occurs when a root CA issues certificates to one or more intermediate certificate authorities, and the intermediate CAs issue certs to subjects.
Root of trust
Root of trust: PKI model that defines how users and different CAs can trust one another in a secure environment used to validate identities and secure communications by ensuring that digital certificates are authentic and issued by a trusted certification authority.
Certificate signing request (CSR) generation
CSR generation: The process of creating a digital signature/digital signing request. Functions by an organization sending a CA their public key, then the CA generates a digital certificate that binds the public key to the organization's identity, ensuring that it can be trusted in communications.
Wildcard
Wildcard certificate: A digital certificate that allows the use of a single certificate to secure multiple subdomains of a domain.