Denial of Service (DoS) and Distributed Denial of Service (DDoS) Attacks
Denial of Service (DoS) Attack
Denial of Service is an application layer attack in which an attacker sends a multitude of specially crafted packets from a single spoofed IP with the intention of crashing an application connected to the Internet
- The general principle is to overwhelm the target with superfluous requests
Types of DoS Attacks
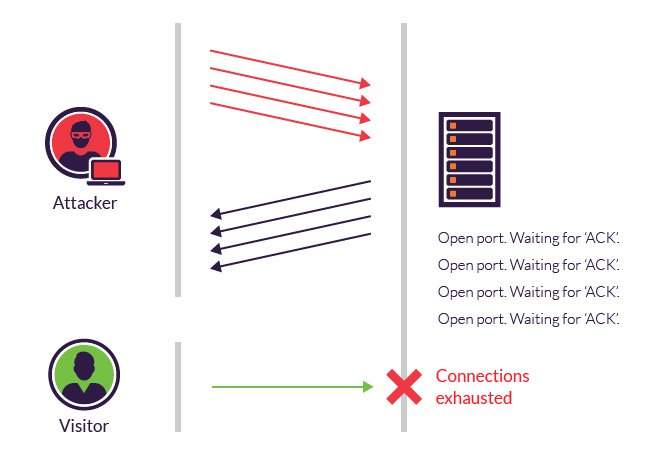
SYN Connection Flooding
- An attacker spoofs their IP address and sends a multitude of SYN packets, never allowing the server the space in its memory to respond and attempt to complete the three-way handshake
- The server uses up all its memory to track the deluge of fictitious half-open connections
- Once the server’s memory fills up, it crashes and stops servicing legitimate users
Defending Against DoS Attacks
Defending Against SYN Connection Flooding Attacks
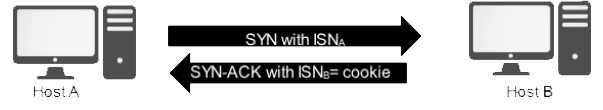
We can defend against these types of attacks using SYN Cookies
When the SYN segment arrives from a foreign client to a web server that’s set up to handle SYN cookies - either in its Apache configuration or as part of the protocol stack itself in the kernel - the server calculates a hash function
* A hash function is a kind of data fingerprint, a unique block of data that identifies a given inputAn SYN Cookie feeds into this hash function the source and destination IP address of the connection to the port with the addition of a unique, randomly generated number
The server uses this hash as its initial sequence number in the SYN/ACK packet
* At this point, the server doesn't have to allocate any memory to keep track of the connectionIf the SYN is from a legitimate client, the host returns an ACK and the final part of the three-way handshake is completed
The server computes that same hash function and verifies that the ACK is from a valid client and opens the TCP connection
If the client is illegitimate, the server never receives an ACK
* Since the server isn’t tracking that original SYN, it isn’t allocating any memory and so it's a non-issue
* People could send in SYNs all day, but they’ll go unanswered with no stress to the server whatsoever
Distributed Denial of Service (DDoS) Attack
In a Distributed Denial of Service attack, the attacker organizes thousands of compromised machines in a botnet so that the flooding traffic originates from multiple sources in an attempt to disrupt the regular traffic of a targeted server, service or network by overwhelming the target or its surrounding infrastructure with a flood of Internet traffic
- IP addresses aren’t spoofed in a DDoS attack because there are too many and there is no practical way to deny those IP packets
Types of DDoS Attacks
In all of these attacks, the attacker tries to send a packet that doesn't conform to any given standard in the hope that whoever programmed the protocol stack didn't do proper error handling
- When that unexpected packet arrives, there's a potential for the application to crash
Land Attack
- A non-volumetric attack where LAN sends a spoofed packet with the source and destination address port being the same on Windows machines that typically cause the machine to blue screen
Ping of Death
- The intention is the same as Land Attack, but attackers send an over-sized ping packet
Jolt2
- Sends a stream of fragments, none of which have an offset of 0
* Rebuilding consumes all processor capacity
Teardrop, Newtear, Bonk, and Syndrop
- Tools that send overlapping fragmented packets to crash a target machine
Reflection Attack
A reflection attack is a method of attacking a challenge-response authentication system that uses the same protocol in both directions
- A Reflection Attack will use a large number of resources like bots or compromised web servers (Reflection attacks use DNS as a source of DDoS traffic)
* An attacker will look for a UDP-based protocol on the Internet that sends a small amount of traffic into a service and gets a large amount of traffic back
* For example, a DNS lookup can be UDP-based
* We're typically doing a look-up for a hostname, but we could potentially get a very large list back from the DNS server of various areas where that resource is located
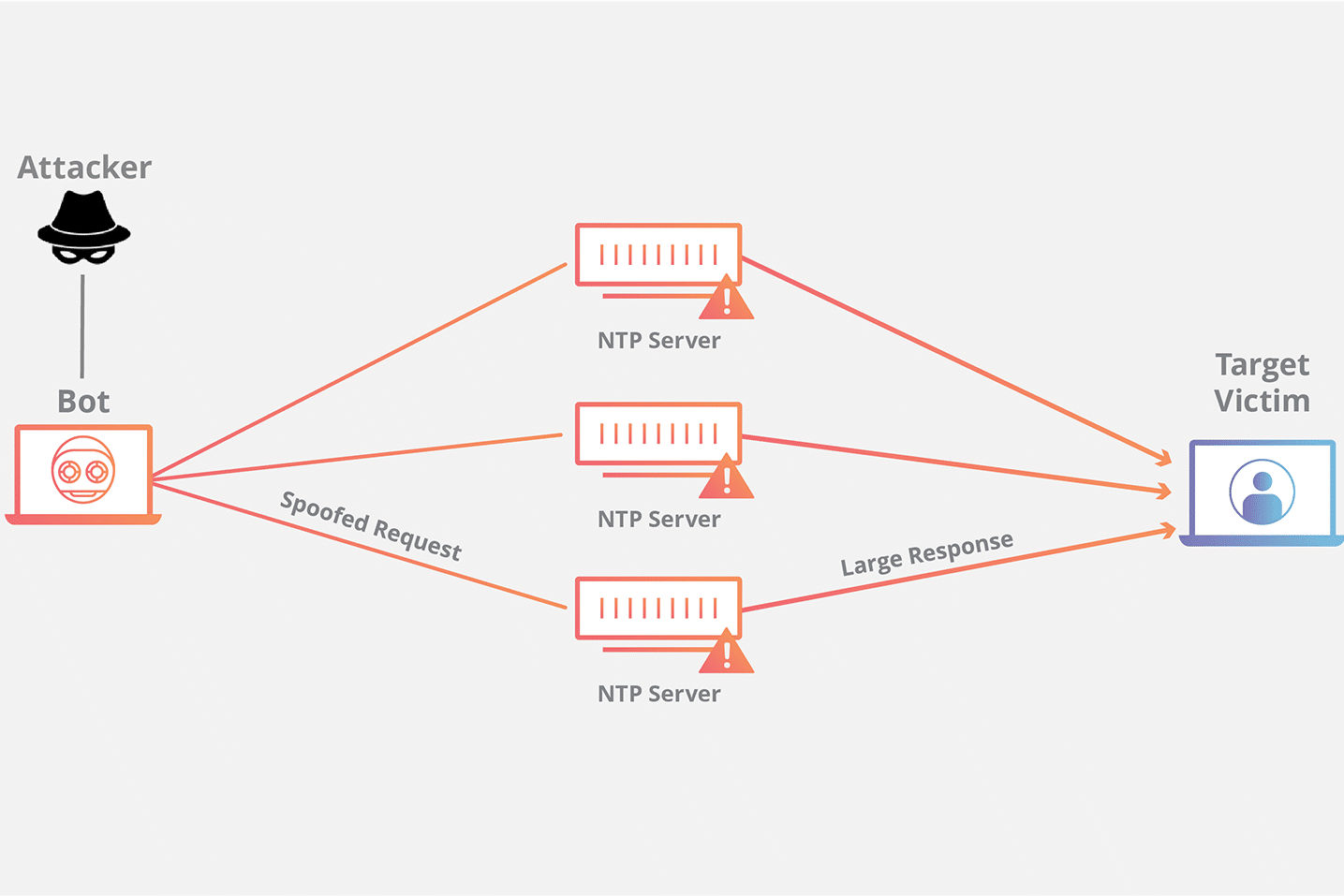
Amplification Attack
An attack where an attacker is able to use an amplification factor to multiply its power
- Amplification attacks are asymmetric, meaning that a relatively small number or low level of resources is required by an attacker to cause a significantly greater number or higher level of target resources to malfunction or fail
A Reflection Attack is sometimes called an Amplification Attack
- For example, NTP - the Network Time Protocol - is UDP-based
* An attacker can send a special command called a monlist on NTP that requests a list of recent machines that have asked for the time
* The attacker will send a very short message and get a long list back, effectively amplifying the traffic
* For the final part of the puzzle, the attacker will spoof their source address to be the victim's IP, making it so that the long list isn't sent back to the attacker, but is instead sent to the target
Types of amplification attacks
Memcached DDoS Attack
A Memcached distributed denial-of-service (DDoS) attack is a type of cyber attack in which an attacker attempts to overload a targeted victim with internet traffic
Defending Against DDoS Attacks
Don't let your systems become a bot
* Not really a defence, but good practice - If everyone works to prevent their systems from becoming bots, we won't have this problemFilter the bad packets from the good packets
* If the defender can find a pattern in the packets that are trying to overwhelm the resource, there is a possibility of being able to filter the bad packets from the good packetsBuild more resources than the attacker
* You very rarely hear about companies like Google and Amazon being victims of DDoS attacks
* An attacker would require a tremendous amount of bandwidth and computing power to run a DDoS against these organizationCreate a distributed infrastructure
* Technologies like Anycast are typically employed for protecting DNS servers against DDoS attacks
* The idea is to distribute a resource that an attacker might target so that there's no single point that can be potentially overwhelmed